Network Security FAQ Virtual Private Networks
Network Security FAQ Virtual Private Networks

Network Security FAQ Virtual Private Networks
E N D
Presentation Transcript
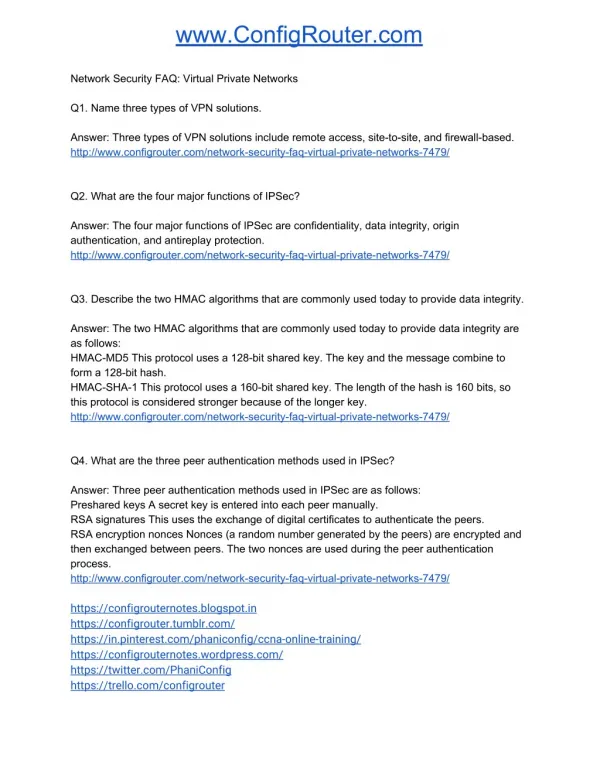
www.ConfigRouter.com NetworkSecurityFAQ:VirtualPrivateNetworks Q1.NamethreetypesofVPNsolutions. Answer:ThreetypesofVPNsolutionsincluderemoteaccess,site-to-site,andfirewall-based. http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/ Q2.WhatarethefourmajorfunctionsofIPSec? Answer:ThefourmajorfunctionsofIPSecareconfidentiality,dataintegrity,origin authentication,andantireplayprotection. http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/ Q3.DescribethetwoHMACalgorithmsthatarecommonlyusedtodaytoprovidedataintegrity. Answer:ThetwoHMACalgorithmsthatarecommonlyusedtodaytoprovidedataintegrityare asfollows: HMAC-MD5Thisprotocolusesa128-bitsharedkey.Thekeyandthemessagecombineto forma128-bithash. HMAC-SHA-1Thisprotocolusesa160-bitsharedkey.Thelengthofthehashis160bits,so thisprotocolisconsideredstrongerbecauseofthelongerkey. http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/ Q4.WhatarethethreepeerauthenticationmethodsusedinIPSec? Answer:ThreepeerauthenticationmethodsusedinIPSecareasfollows: PresharedkeysAsecretkeyisenteredintoeachpeermanually. RSAsignaturesThisusestheexchangeofdigitalcertificatestoauthenticatethepeers. RSAencryptionnoncesNonces(arandomnumbergeneratedbythepeers)areencryptedand thenexchangedbetweenpeers.Thetwononcesareusedduringthepeerauthentication process. http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/ https://configrouternotes.blogspot.in https://configrouter.tumblr.com/ https://in.pinterest.com/phaniconfig/ccna-online-training/ https://configrouternotes.wordpress.com/ https://twitter.com/PhaniConfig https://trello.com/configrouter
www.ConfigRouter.com http://flip.it/y5znjX https://www.reddit.com/user/phani_config/ https://www.scoop.it/t/ccna-exam-answers http://feeds.feedburner.com/ConfigRouter CCNA 200-125 Dump With Questions and Answers with Explanation CCNA NetAcad Training CCNA RS Training CCNA Cyber Ops Training CCNA Data Center Training CCNA Security Training https://www.youtube.com/c/CiscoNetworkingVideos NexusOSBasicsandFundamentalsCompleteVideoCourse https://www.youtube.com/watch?v=pwn0sT4pOEo&list=PL9UP_4zHScPw49YXOCkK9UFRbPP S55RD2 CCNACyberOpsSECFND210-250CompleteVideoCourse https://www.youtube.com/watch?v=eT88kco4u5M&list=PL9UP_4zHScPxTqWXRTbTHOUZ4IH BfItpZ CCNAWireless200-355CompleteVideoCourse https://www.youtube.com/watch?v=yNnGavnlTZ0&list=PL9UP_4zHScPweZMvKm2mhucuF0X- kO5jV CCNACloudCLDADM210-455CompleteVideoCourse https://www.youtube.com/watch?v=GjD27VyOYEQ&list=PL9UP_4zHScPz35gaincmzptwnH1cB M8Oj CCNADataCenterDCICT200-155CompleteVideoCourse https://www.youtube.com/watch?v=QMe8ZgviyZ4&list=PL9UP_4zHScPwrrIVgNHW8c2weI-pIgF DL CCNADataCenterDCICN200-150CompleteVideoCourse https://www.youtube.com/watch?v=VAJv3C4BgjE&list=PL9UP_4zHScPyjupWBcyODSaJjlR7Se Ik- CCNACloudCLDFND200-451CompleteVideoCourse https://www.youtube.com/watch?v=C3SdnXLAA7M&list=PL9UP_4zHScPy8PX3z55iFF0rW66n- 1PDf
www.ConfigRouter.com Q5.TherearetwomainIPSecframeworkprotocolsavailable.Statetheirnamesandgiveabrief explanationofwhattheydo. Answer:ThetwomainIPSecframeworkprotocolsareasfollows: AHAHistheprotocoltousewhenconfidentialityisnotrequired.Itprovidesdataauthentication andintegrityforIPpacketsbetweentwosystems.Itverifiesthattheoriginofthepacketis correctandthatthepacketisnotmodifiedduringtransport.Itdoesnotencryptthedatapacket. Alltextistransportedincleartext. ESPThisprotocolcanbeusedtoprovideencryptionandauthentication.Itprovides confidentialitybyperformingencryptionattheIPpacketlayer.ESPprovidesauthenticationfor theIPpacketandtheESPheader.AswithAH,ESPverifiesthreethings:thatthepacket originatedfromwhereitdeclaresitdid,thatthepacketiswhatitsaysitis,andthatthepacket hasnotbeenmodifiedduringtransport. http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/ Q6.BothESPandAHcanbeappliedtoIPpacketsintwodifferentways.Listthosetwomodes andexplainthedifferencebetweenthem. Answer:Thetwomodesareasfollows: TransportmodeThismodeisprimarilyusedforend-to-endconnectionsbetweenhostsor devicesactingashosts.Transportmodeprotectsthepayloadofthepacketbutleavesthe originalIPaddressreadable.ThisaddressisusedtoroutepacketsthroughtheInternet. Transportmodeprovidessecuritytothehigherlayerprotocolsonly. TunnelmodeThismodeisusedbetweengatewayssuchasrouters,PIXFirewalls,orVPN concentrators.TunnelmodeisusedwhenthefinaldestinationisnotahostbutaVPNgateway. Inthismode,insteadofshiftingtheoriginalIPheadertotheleftandtheninsertingtheIPSec header,theoriginalheaderiscopiedandshiftedtothelefttoformanewIPheader.TheIPSec headeristhenplacedbetweenthenewandtheoriginalIPheaders.Theoriginaldatagramisleft intact. http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/ Q7.ListthefunctionsforwhichIKEPhase1isresponsible. Answer:IKEPhase1isresponsibleforthefollowingfunctions: AuthenticatingtheIPSecpeers NegotiatinganIKEsecurityassociationbetweenthepeers InitiatingasecuretunnelforIPSecusingtheInternetSecurityAssociationandKey ManagementProtocol(ISAKMP) http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/
www.ConfigRouter.com Q8.ListthefunctionsforwhichIKEPhase2isresponsible. Answer:IKEPhase2isresponsibleforthefollowingfunctions: Negotiatingthesetofsecurityparametersforthetunnel CreatingtheIPSectunnel http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/ Q9.WhatstepsshouldbecompletedbeforeconfiguringadevicetouseIPSec? Answer:BeforeconfiguringadevicetouseIPSec,youshouldcompletethefollowingsteps: Step1.EstablishanIKEpolicyThispolicymustbeidenticalonbothsidesoftheVPN. Step2.EstablishanIPSecpolicyOnlycertaintraffichastogothroughtheIPSectunnel.Of course,youcandecidetosendalltrafficbetweenpeersthroughthattunnel,butthereisa significantperformancepenaltywhenusingIPSec.Itisbettertobeselective.Asinstep1,both peersneedtohavethesameIPSecpolicies. Step3.ExaminetheexistingconfigurationCheckyourdevicestoavoidconflictswithexisting settingsononeofthedevices. Step4.TestthenetworkbeforeIPSecCheckwhetheryoucanpingthepeersthataregoingto participateinIPSec.Ifyoucannotpingthem,youmustfixthisbeforeyoucanconfigureIPSec. Step5.PermitIPSecportsandprotocolsIfthereareaccesslistsenabledonthedevicesalong thepathoftheVPN,makesurethatthosedevicespermittheIPSectraffic. http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/ Q10.DescribebrieflyhowtheIPSecprocessworks. Answer:ThefollowingstepsoutlinehowanIPSecprocessworks: Step1.InterestingtrafficinitiatesthesetupofanIPSectunnel. Step2.IKEPhase1authenticatespeersandestablishesasecuretunnelforIPSecnegotiation. Step3.IKEPhase2completestheIPSecnegotiationandestablishesthetunnel. Step4.SecureVPNcommunicationcanoccur. Step5.WhenthereisnotraffictouseIPSec,thetunnelistorndown,eitherexplicitlyor becausetheSAtimedout. http://www.configrouter.com/network-security-faq-virtual-private-networks-7479/