Nmap Tutorial For Beginners | Nmap Vulnerability Scan Tutorial | Simplilearn
In this presentation on Nmap Tutorial for beginners, we cover the basic explanation and operation of nmap. We also have a nmap vulnerability scan tutorial at the end of our lesson where we use Nmap to run multiple scans and breach a windows computer. This nmap hacking tutorial also lists the different modes of scanning and a couple of alternative tools to be considered.<br><br>1. Introduction <br>2. Phases In Ethical Hacking<br>3. What Is N-Map?<br>4. Modes of Operation<br>5. Alternatives to N-Map<br>6. Live Demonstration


Nmap Tutorial For Beginners | Nmap Vulnerability Scan Tutorial | Simplilearn
E N D
Presentation Transcript
Phases In Ethical Hacking What Is N-Map? How Does N-Map Work? Modes of Operation Alternatives to N-Map Live Demonstration Agenda for the Day
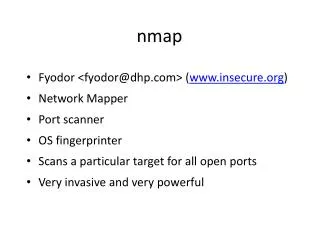
Open source and free network scanner created by Gordon Lyon • Used during reconnaissance stage of hacking • Can discover hosts and services on a system by the responses received • Finds vulnerable ports and services on a network What Is N-Map?
Specially-crafted packets to generate replies How Does N-Map Work? Victim Machine Host replies to Nmap’s requests for analysis Life of host, Ports opened, Services Used, Host OS
Ping Sweep • SYN Scan • TCP Connect Scan • Idle Scan • RPC Scan • Windows Scan • Bounce Scan • UDP Scan • FIN Scan • NULL Scan Modes of Operation
Installing N-Map on a fresh system • Running different types of scans • Using different scan filters • Scanning for vulnerabilities on attack box machines Live Demonstration