Comprehensive Guide to Simple Compiler Implementation and Architecture
This document provides detailed insights on the implementation of a simple compiler, covering high-level architecture, frontend optimizations, and backend translation phases including NFA/DFA, AST, High-Level IR, and backend machine representations. It introduces memory management techniques, including memory pools, smart pointers, and intrusive lists. The guide also outlines a command-line parser capable of handling various option types, supports logging features, and describes low-level utilities tailored for operating system abstraction. Emphasis is placed on the use of STL and potential integration with Boost for enhanced functionality.

Comprehensive Guide to Simple Compiler Implementation and Architecture
E N D
Presentation Transcript
Simple Compiler - SCL Notes on implementation details
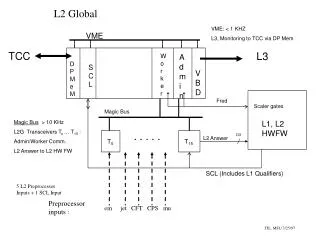
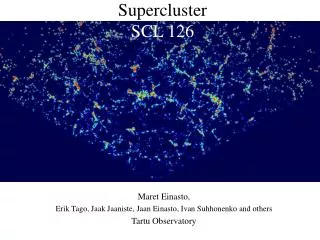
High-level architecture Frontend High-level optimizations Backend Translation phases NFA & DFA AST High-Level IR Backend IR Machine Description Representations Symbol Table Memory-Managed Containers Graph Data structures Dynamic Memory Allocation Memory manager Memory Pools (Specialized/Default) Smart Pointers Intrusive lists Command line parser Logs Utils Asserts C++ STL Other external SW (e.g. Boost) Low-level Utils Operating system abstraction layer
Low Level Utils • Assert macros • ASSERT(cond) just checks the condition while ASSERT_X(cond, where, what)prints out additional info on failure • ASSERT/ASSERTD, ASSERT_X/ASSERT_XDfor release/debug build • Most of the time ASSERT_XD should be used • Usage of STL is allowed • Below and including UTILS level • For non-critical functionality above UTILS • BOOST usage possibilty has not been studied yet
Utils • Intrusive lists • Double-linked lists that built peer pointers into the object via inheritance • An object can be involved in multiple lists • Command line options parser • Supports boolean, integer, floating-point and string options • Supports long and short forms of options • Logging support • Logging to file • Logs can form tree-like hierarchy
Intrusive Lists Doubly-liked lists. One object can participate in multiple list. The peer pointers are stored within the client object. Intrusive lists are created by subclassing instance of SListIface ( or MListIface for multiple lists) template corresponding to user class. MyClass MyClass NULL SListItem SListItem next next prev prev User Data User Data Typical syntax example: classMyClass: publicSListIface<MyClass> { … };