Chapter 6 Enumeration
Chapter 6 Enumeration. 2009 fall SCSC 555 Frank Li. Objectives. Introduction to Enumeration Enumerate Microsoft OS Enumerate *NIX OS Enumerate NetWare OS (skip). Introduction to Enumeration. Enumeration extracts information about: Resources or shares on the network

Chapter 6 Enumeration
E N D
Presentation Transcript
Chapter 6 Enumeration 2009 fall SCSC 555 Frank Li
Objectives • Introduction to Enumeration • Enumerate Microsoft OS • Enumerate *NIX OS • Enumerate NetWare OS (skip)
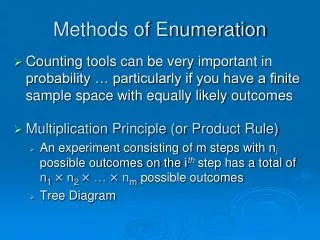
Introduction to Enumeration • Enumeration extracts information about: • Resources or shares on the network • User names or groups assigned on the network • Last time user logged on • User’s password • Enumeration is more intrusive than passive port scanning • First need to determine OS of the target host • By Port scanning and footprinting • E.g. NBT (NetBIOS over TCP/IP) is the tool for enumerating Microsoft OSs
Introduction to Enumeration • Using enumeration tool nbtscan • Use nbtscan command to scan a range of IP addresses • Example: nbtscan 192.168.0.0./24
Objectives • Introduction to Enumeration • Enumerate Microsoft OS • Enumerate *NIX OS
Enumerating Microsoft OS • Study OS history • Knowing your target makes your job easier • Many attacks that work for older Windows OSs still work with newer versions
NetBIOS Basics • Network Basic Input Output System (NetBIOS) • Is a MS programming interface • Allows computer communication over a LAN • Used to share files and printers • NetBIOS names are computer names assigned to Windows systems • Must be unique on a network • Limit of 16 characters • The last character (suffix) is reserved for identifies type of service running next page
NetBIOS Null Sessions • One of the biggest vulnerabilities of NetBIOS system -- NetBIOS Null session • Is unauthenticated connection to a Windows computer • Does not use logon and passwords values • Attackers use enumeration tool to establish a null session • to gather logon accounts, group membership, and file shares from target hosts
NetBIOS NULL sessions in Windows • NetBIOS NULL sessions are enabled by default in Windows NT and 2000. • Windows XP and 2003 will allow anonymous enumeration of shares, but not accounts.
Ports for NULL sessions • For the most part if the appropriate ports are accessible a NULL session is possible.
NetBIOS Enumeration Tools (1) • Use IP address obtained when port scanning to perform a NetBIOS enumeration • NetBIOS Enumeration Tools • Nbtstat • Net view • Net use • NetScanTools Pro • DumpSec • Hyena • NessusWX • Enum • Hunt
NetBIOS Enumeration Tools (2) • Nbtstat command • Powerful enumeration tool included with the Microsoft OS • Displays NetBIOS table • E.g., Nbstat –a salesrep
NetBIOS Enumeration Tools (2) • Net view command • Shows whether there are any shared resources on a network host • E.g., net view \\192.168.0.106
NetBIOS Enumeration Tools (continued) • Net use command • Used to connect to a computer with shared folders or files • view the information about current computer connections. • also can controls persistent network connections. • E.g., To assign the disk-drive device name E: to the Letters shared directory on the \\Fin server, type: net use e: \\fin\letters
NetScanTools Pro • NetScanTools Pro produces a graphical view of NetBIOS running on a network • Enumerates any shares running on the computer • Verifies whether access is available for shared resource using its Universal Naming Convention (UNC) name • Example: figure 6-10, 6-11 • the \\SALEsMGR\SharedDocs comment entry is blank. to see whether access is available, an attacker enters the UNC \\SALEsMGR\SharedDocs in the Run dialog ox in Windows
DumpSec • DumpSec http://www.systemtools.com/cgi-in/download.pl?DumpAcl • Produced by Foundstone, Inc. • Allows user to connect to a server and “dump” the following information • Permissions for shares • Permissions for printers • Permissions for the Registry • Users in column or table format • Policies and rights • Services
Hyena • Hyena is GUI product for managing and securing Microsoft OSs • Shows shares and user logon names for Windows servers and domain controllers • Displays graphical representation of: • Microsoft Terminal Services • Microsoft Windows Network • Web Client Network • Find User/Group
NessusWX (1) • NessusWX allows enumeration of different OSs on a large network • Running NessusWX • Nessus server is up and running • Open the NessusWX client application • To connect your NessusWX client with the Nessus server • Click Communications, Connect from the menu on the session window • Enter server’s name • Log on the Nessus server
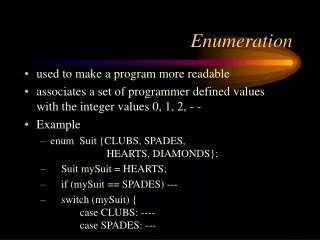
NetBIOS Enumeration Tools Enumhttp://www.bindview.com/Services/RAZOR/Utilities/Windows/enum_readme.cfm • one of the best tools for exploiting the NULL session vulnerability • allowing you to exploits every aspect of this flaw. • the ability to enumerate users, • and then try to brute force the password using a supplied password list.
NetBIOS Enumeration Tools Hunthttp://www.foundstone.com/resources/freetools/hunt.zip • Part of the NT Forensic Toolkit from Foundstone, • this tool makes it very easy to enumerate users and shares from a vulnerable windows host, and is the most accurate
NessusWX (2) • Nessus identifies • NetBIOS names in use • Shared resources • Password information
NessusWX (3) • Nessus also identifies: • OS and service pack • OS vulnerabilities • Firewall vulnerabilities
Objectives • Introduction to Enumeration • Enumerate Microsoft OS • Enumerate *NIX OS
Enumerating the *NIX Operating System • variations of Unix • Solaris • SunOS • HP-UX • Linux • Ultrix • AIX • BSD UNIX • FreeBSD • OpenBSD
UNIX Enumeration Tools • Finger utility • Is the most popular tool for security testers • Finds out who is logged in to a *NIX system • Determine owner of any process • Nessus can also be used for *NIX enumeration
Another example of finger • E.g., # finger -b -p james display the following information about the user james. Login name, Computer Hope on since Feb 11 23:37:16 on pts/7 from domain.computerhope.com28 seconds Idle TimeUnread mail since Mon Feb 12 00:22:52 2001