How to Protect Your PC
How to Protect Your PC Grayware Adware, Malware, Spyware Annoying software and Malicious Software

How to Protect Your PC
E N D
Presentation Transcript
How to Protect Your PC GraywareAdware, Malware, Spyware
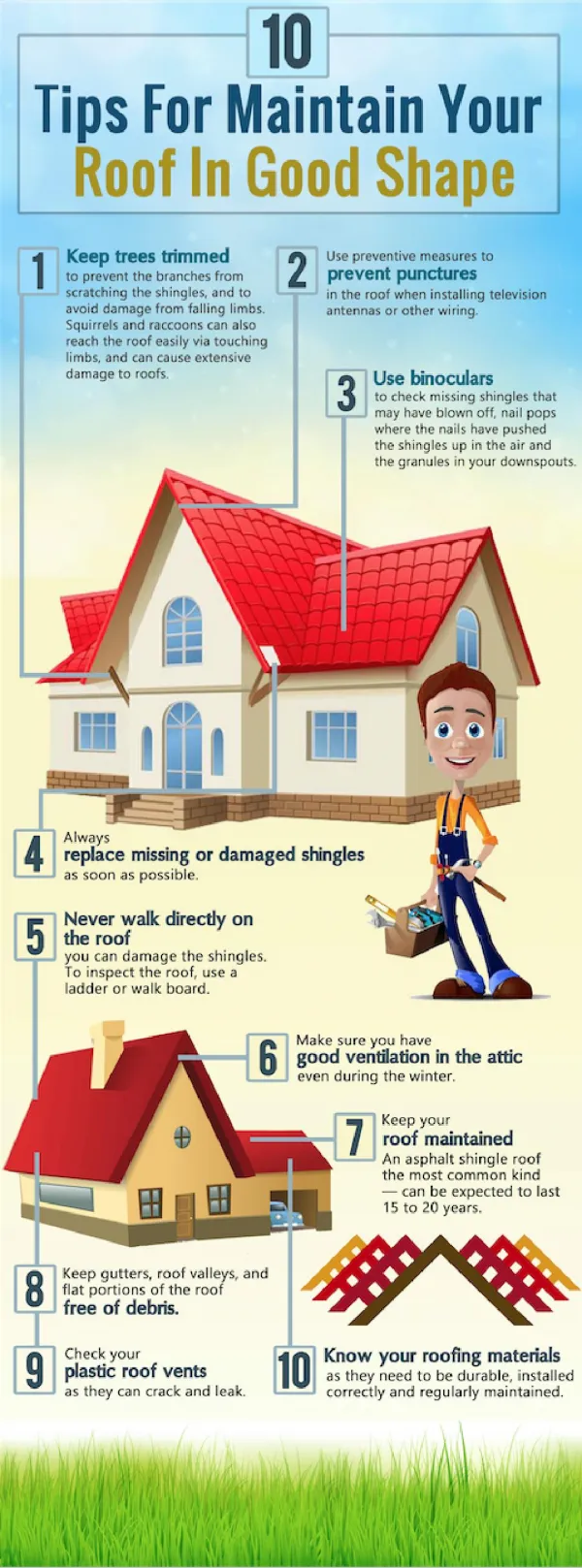
Annoying software and Malicious Software Grayware – Grayware encompasses spyware, adware, dialers, joke programs, remote access tools, and any other unwelcome files and programs apart from viruses that can harm the performance of computers on your network. Grayware refers to applications or files that are not classified as viruses or Trojan horse programs, but can still negatively affect the performance of the computers on your network and introduce significant security risks to your organization. Adware - software that displays advertising banners, re-directs you to websites, and otherwise conducts advertising on your computer (not to be confused with popup ads, which come from the websites that you visit). Malware - malicious software that is intended to do harm to your computer or software, including viruses, Trojans, and worms. Spyware - software that gathers information about you, your browsing and Internet usage habits, as well as other data.
How does grayware get onto my computer? • Grayware can get onto your computer several ways • If you install a peer-to-peer file-sharing system, grayware is often “bundled” in the install process. This is also common with other downloads/installs. • Be suspicious of programs “enhancing” your computer. These could be tricky ways to get you to install grayware onto your computer. Examples are “smileys” for your email, new mouse cursors, screen savers, etc. • If your PC is not properly protected, it is possible for grayware and other unwanted files to be installed onto your computer without your knowledge.
What can I do to prevent “Grayware?” • Update your PC security! • grayware authors know and attempt to exploit security “holes” in software. Be sure to keep all of your software up to date, especially your operating system, firewall, & anti-virus. • Browse wisely. You can change your internet browser settings (Internet Explorer, Firefox) with a few clicks. A good site for information is: http://privacy.getnetwise.org/browsing • Download programs ONLY from sites you trust. • Use grayware detection programs, such as firewalls, anti-virus protection, and adware/malware scanners. • Read the fine print! Many programs, security warnings, and privacy statements contain critical information, including what you are installing.
E-avesdropping: Web Bugs • Unfortunately, Ad-aware can't isn’t a sure fix. “Net snoops” might also track your surfing habits through Web bugs, clear images that send back your ISP address, telling others that you are viewing their page or content. Not all Web bugs are bad. Some companies use clear image files to count how many readers visit a particular page. Guard-IE is one particular product that alerts you to the presence of Web bugs on a site, then lets you block them if you choose. Guard-IE also removes Web referrers, tags that tell Web sites the last site you visited. Finally, Guard-IE removes your Internet cookies, browser history, and any temp files created on your hard drive…a good way to keep your surfing habits from prying eyes. • As good a privacy tool as Guard-IE is, only Internet Explorer users will benefit.For a good, all-around, ad-blocking andprivacy-enhancing product for bothNetscape and Internet Explorer, a goodtool is AdSubtract Pro. • Source: C|NET
E-avesdropping: E-Mail • Someone could be reading your e-mail. Consider this: Your e-mail program probably sends your mail as an alphanumeric text file. That means that anyone, whether at your company or at your Internet service provider, could intercept, open, and read your mail with a text editor such as Windows Notepad. Sharing banana-bread recipes online? You probably don't have much to worry about. But if you discuss business deals via e-mail, you'll need extra protection. • A few products can encrypt the contents of your mail. If you're looking for a free program to do encrypted e-mail, the selection is limited, if you want to integrate with Outlook. Thunderbird+Enigmail+GnuPG or GPG4Win does integrate with Outlook 2003
Resources • Set Internet browsers securelyhttp://privacy.getnetwise.org/browsing • McAfee Home Editionhttp://www.purdue.edu/securePurdue/news/detail.cfm?NewsID=124