Assessing Machine Learning Algorithms as Intrusion Detection Systems
Assessing Machine Learning Algorithms as Intrusion Detection Systems. Greig Hazell. Outline. Motivation Past Research Approach Early Results Going Forward Q & A. Motivation. What are Intrusion Detection Systems? IDS – Security Tool to strengthen security of communication systems.

Assessing Machine Learning Algorithms as Intrusion Detection Systems
E N D
Presentation Transcript
Assessing Machine Learning Algorithms as Intrusion Detection Systems Greig Hazell
Outline • Motivation • Past Research • Approach • Early Results • Going Forward • Q & A
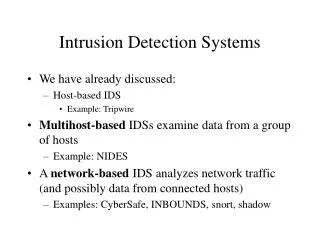
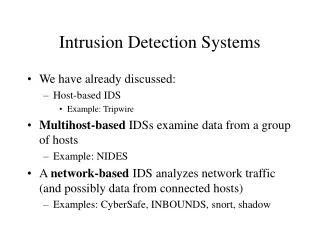
Motivation • What are Intrusion Detection Systems? • IDS – Security Tool to strengthen security of communication systems. • Two Categories • Anomaly-Based IDS • Misuse-Based IDS • Anomaly-Based Systems • Pattern matching of known attack signatures. • High accuracy of known attacks. • Misuse-Based Systems • Profiles Normal System Behavior. • Flags Behavior which deviates from normal profile.
Past Research • Focused on Classification Rate of IDS. • However Network-IDS also require: • High throughput • Low Resource Utilization
Approach • Utilize Several Machine Learning Algorithms: • KNN, MLP, RBF • Dataset • KDD 99 Data Cup (10%) • [http://kdd.ics.uci.edu/databases/kddcup99/kddcup99.html] • 41 Features • 21 Attack Types in Training Data • Testing Data Included new attacks not present in training data. • Pre-processing of data to an input compatible with MLAs. • Approx.: 400K Training Records, 300K Testing
Early Results • MLP • Layers: 41-25-2, Epochs: 30 • Classification Accuracy on Test Data • Throughput • Total Time: 52 s • 0.17 ms / classification • approx.: 6000 classifications / s
Going Forward • Determine throughput and resource usage • Pre-processing & Normalization of data • PCA • 0 Mean & Unit Variance. • Compare Results to Anomaly-Based Systems.