By Ajith U Kamath 60-564 Project
310 likes | 490 Vues
By Ajith U Kamath 60-564 Project. Survey on Areas of standardization For Securing Ad hoc networks. Based on. Standardization Areas for securing Ad hoc networks By Rajesh Talpade and Anthony McAuley Data Security in Ad hoc networks using Multipath routing

By Ajith U Kamath 60-564 Project
E N D
Presentation Transcript
ByAjith U Kamath60-564 Project Survey onAreas of standardizationForSecuring Ad hoc networks
Based on • Standardization Areas for securing Ad hoc networks By Rajesh Talpade and Anthony McAuley • Data Security in Ad hoc networks using Multipath routing By Souheila Bouam and Jalel Ben-Othman
AGENDA • Introduction • Attacks in Ad hoc networks and Areas of standardization • Node configuration • Key Management • Routing protocol security • Data security based on multipath routing • Intrusion Detection • Conclusion
Introduction • What are Mobile Ad hoc networks ? • Characteristics • Problems encountered
Attacks in Ad hoc networks • Passive attacks • Active attacks • Black hole attack • Worm hole attack • Routing tables overflow attacks
Attacks in Ad hoc networks • Active attacks • Sleep deprivation attacks • Location disclosure attacks • Denial of service attacks • Impersonation attacks "Problems worthy of attack prove their worth by hitting back.“ – By Piet Hein
Areas of Standardization It is expected in future, multi vendor ad hoc devices would inter-operate securely on a large scale. Standardization Areas, • Node configuration • Key management • Routing protocol security • Intrusion detection
Node Configuration In realistic deployment scenarios nodes of ad hoc network should support auto-configuration. • Link Local IP address assignment Private address spaces (e.g. 169.254/16 prefix) • IPv6 address generation based on hardware interface Problems: different designs for different link-layers, non-unique interface addresses in some link-layers or vendors, and changeable interface addresses.
Node Configuration • Distributed dynamic host configuration protocol • MANET Initialization • New node joining the MANET • Graceful departure of the node • Migration of Requester • tolerate message losses, network partitioning and mergers • does not account for the possibility of nodes behaving maliciously
Key Management For enforcing confidentiality, integrity, authentication and non-repudiation of messages in ad hoc networks. • Key management Service through CA A centralized CA-based approach is not applicable to ad hoc networks. Replicating the CA, introduces the problem of maintaining the synchronization across the multiple CA’s
Key Management • Threshold cryptography An (n; t + 1) threshold cryptography scheme allows ‘n’ parties to share the ability to perform a cryptographic operation, so that any ‘t + 1’ parties can perform this operation jointly, whereas it is infeasible for at most ‘t’ parties to do so, even by collusion.
Key Management But places unreasonable requirement of forcing some nodes to “volunteer” for specific roles. Ref: Parallel reliable threshold multisignature by Yair Frankel and Yvo G
Key Management • Self organized public key infrastructure • Public key certificates are issued by the users. • When user u wants to obtain the authentic public key of user v, it acquires a chain of public key certificates such that the first certificate of the chain can directly be verified by u using a public key that u holds and trusts. • Similar to PGP but self organized. • The approach is probabilistic.
Key Management Ref: The Quest for Security in Mobile Ad Hoc Networks by Jean-Pierre Hubaux, Levente Butty´an and Srdan Capkun
Routing Protocol Security An attacker can inject incorrect routing information, replay old information, or cause excessive load to prevent proper routing protocol functioning. • Data security based on multipath routing. Exploit the feature of existence of multiple paths between nodes in an Ad hoc network.
Routing Protocol Security • Assumptions made by the protocol • The sender ‘A’ and the receiver ‘B’ are authenticated. • WEP (Wireless Equivalent Privacy) is used for the encryption/decryption of all the frames at MAC layer and the authentication of the terminals. • A mechanism of discovering the topology of the network is available. • The used routing protocol supports multi-routes.
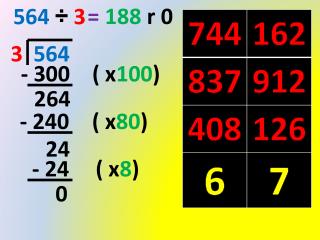
Routing Protocol Security • Description • It uses n routes (n ≥ 3) among N available. • There exist two types of channels • The original message m is divided into (n-1) parts. • The protocol generates, then, a random number x (1< x ≤ (n-1), x integer). • Algorithm can be run with both reactive and proactive routing protocols.
Routing Protocol Security Ref: Data Security in Ad hoc Networks Using MultiPath Routing By Souheila BOUAM and Jalel BEN-OTHMAN
Routing Protocol Security • Position of SDMP • The SDMP header
Routing Protocol Security • Improvements (Accepted in the 2004 International Workshop on Mobile Ad Hoc Networks and Interoperability Issues.) • Error and Retransmit management Ref: Securing Data Transmissions and Retransmissions Management in Ad hoc Networks By Souheila BOUAM and Jalel BEN-OTHMAN
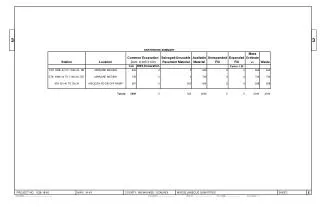
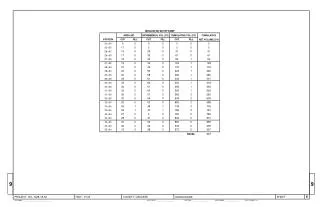
Routing Protocol Security • Experimental results • Sending data using the algorithm (n=8 and n=4) and using classical method with one channel are compared. The transmitted file is 4.48 MB length and length of each block is 64 Kbytes. Ref: Data Security in Ad hoc Networks Using MultiPath Routing By Souheila BOUAM and Jalel BEN-OTHMAN
Routing Protocol Security • In the second test, different block sizes at each data transmission were used. A base file of 19200 Bytes was used. Ref: Data Security in Ad hoc Networks Using MultiPath Routing By Souheila BOUAM and Jalel BEN-OTHMAN
Routing Protocol Security • Drawbacks of the protocol • Diversity coding provides single line failure with only one extra line instantaneously without communicating with the transmitter. But this feature is not made use of in the protocol. • A particular sequence has to be followed to get each message parts. If a message part is lost, all the remaining parts cannot be obtained until receiver receives the lost message part. • More bandwidth is consumed for transmitting the message.
Routing Protocol Security • Protocols based on multi path routing • SPREAD (Security Protocol for Reliable data delivery) – uses threshold secret sharing system. Provides maximum security along with reliability of some extent. • Split multi path routing - uses the source routing. The message parts are sent on maximum routes with maximally disjoint paths. The protocol builds multiple routes using request/reply cycles. • M-TCP – Multipath TCP
Routing Protocol Security • Dynamic Source Routing • Source routing is a routing technique in which the sender of a packet determines the complete sequence of nodes through which to forward the packet. • Assumes that all hosts wishing to communicate with other hosts within the ad hoc network are willing to participate fully in the protocols of the network. • Route Discovery protocol
Routing Protocol Security • Grudging Nodes in DSR • Once non-cooperative behavior has been detected and exceeds threshold values, an ALARM message is sent.
Intrusion Detection In an ad hoc network, there does not exists natural traffic concentrators such as firewalls/gateways and localized communication pattern. • Intrusion Detection in Ad hoc networks • Every node in the ad-hoc network participates in intrusion detection and response. • Each node is responsible for detecting signs of intrusion locally and independently. • Neighboring nodes can collaboratively investigate in a broader range.
Intrusion Detection The conceptual IDS model at every system in the ad hoc network. Ref: Intrusion Detection in Wireless Ad Hoc Networks By Yongguang Zhang and Wenke Lee
Intrusion Detection Standardization of the intrusion detection mechanisms and processes enables nodes from multiple vendors to share information and collectively determine the intruding node(s).
Conclusion Even though significant research work exists in the above areas of ad hoc networks, little or no attempt has been made to standardize mechanisms that would enable multi vendor nodes to inter-operate on a large scale and permit commercial deployments of ad hoc networks. Based on the requirements for each of the identified areas, candidate proposals will need to be evaluated.
Thank You Questions ? Comments ?