What does 21 CFR 11 Require?
What does 21 CFR 11 Require?. The FDA requires corporate compliance on the areas listed below. This document specifically deals with the FDA audit trail . Validation is required for all systems ( “all versions of application software, operating systems, and software development tools.”)

What does 21 CFR 11 Require?
E N D
Presentation Transcript
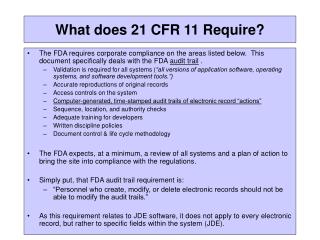
What does 21 CFR 11 Require? • The FDA requires corporate compliance on the areas listed below. This document specifically deals with the FDA audit trail . • Validation is required for all systems (“all versions of application software, operating systems, and software development tools.”) • Accurate reproductions of original records • Access controls on the system • Computer-generated, time-stamped audit trails of electronic record “actions” • Sequence, location, and authority checks • Adequate training for developers • Written discipline policies • Document control & life cycle methodology • The FDA expects, at a minimum, a review of all systems and a plan of action to bring the site into compliance with the regulations. • Simply put, that FDA audit trail requirement is: • “Personnel who create, modify, or delete electronic records should not be able to modify the audit trails.” • As this requirement relates to JDE software, it does not apply to every electronic record, but rather to specific fields within the system (JDE).
Why this is important • FDA only checks a signature (audit trail) when there is doubt in the veracity of a document. • A document can be adulterated for exactly one of two reasons: error or fraud. • The technology’s “integrity check” function makes the probability of an unidentifiable error extremely (i.e., 2exp128) remote. • Therefore, the very action of challenging a signature is the equivalent of an accusation of deliberate fraud. (i.e., a crime) • Senior management needs to develop, deploy, enforce, and document policies and procedures that mitigate this business risk. • The result will be a combination of ongoing effort, internal and external audits, rigor, vigilance, and some INFOSEC technology.