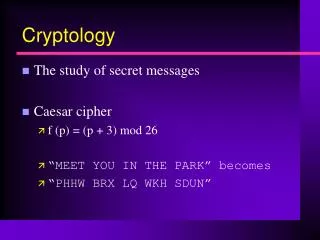
Cryptology
Cryptology. Making & Breaking Codes & Ciphers. Cryptology. Cryptography Science of creating codes or ciphers Cryptanalysis Science of breaking codes and ciphers. Codes vs. Ciphers. Code Substitution of words or phrases by others Example: Navajo “code talkers” of WW II:

Cryptology
E N D
Presentation Transcript
Cryptology Making & Breaking Codes & Ciphers
Cryptology • Cryptography • Science of creating codes or ciphers • Cryptanalysis • Science of breaking codes and ciphers AJ 115
Codes vs. Ciphers • Code • Substitution of words or phrases by others • Example: Navajo “code talkers” of WW II: • turtle means tank • sea turtle means landing craft • Cipher • Algorithmic scrambling/unscrambling • Example: Caesar cipher • Replace each letter with the letter 3 positions after it in the alphabet (a d, b e, etc.) AJ 115
Terminology • Plaintext • The unencrypted (readable) message • Ciphertext • The encrypted version of the message • Secure channel • A communications path safe from eavesdropping • Insecure channel • A communications path that may be tapped AJ 115
Stream & Block Ciphers • Stream cipher acts on one character at a time • Replaces each character with a different symbol • Fixed: Each plaintext ‘a’ is always replace by the same ciphertext symbol • Example: Caesar cipher (‘a’ always replaced by ‘d’) • Example: rot13 (used to encode “obscene” text) • Variable: Different occurrences of ‘a’ in the plaintext are replaced with different symbols in the ciphertext • Example: German Enigma cipher machine of WWII AJ 115
Jefferson’s Cipher Machine • A stack of code wheels threaded on a central axis • Could be any length, but typically ~30 • Each had all letters of the alphabet, but no two were identical • To encrypt a message • Divide message into blocks = stack size • Turn wheels so plaintext shows on one row • Lock the wheels • Transmit any other row AJ 115
Jefferson’s Cipher Machine • To decrypt a message • Set wheels to match the ciphertext for each block • Lock the wheels • Look for the one row that contains readable plaintext • Jefferson’s machine was used, successfully, for almost a century AJ 115
Zimmermann Telegram AJ 115
Enigma & Ultra • Used by Germany during WW II • Considered it “unbreakable” • Broken in 1940 by Britain (“Ultra”) • Team at Bletchley Park, headed by Alan M. Turing AJ 115
How Enigma Worked • Operator typed plaintext message • 3 rotors scrambled each letter • Ciphertext character lit up on upper panel • Rotors turned after every letter AJ 115
How Enigma was Solved • Lots of similar messages • Germans sent weather information to U-boats every day, all in same format • Human error • Lazy or tired operators re-used rotor settings instead of changing them • Repeated first 3 characters of message • Weakness of algorithm • Would never translate a letter to itself AJ 115
How Enigma was Solved • The “Bombe” • Computer at Bletchley Park • Searched thousands of possible Enigma settings, looking for one that yielded readable plaintext • Captured code books • Naval vessels carried books of Enigma settings • British captured U-559 in Sept. 1942 • By 1943, Britain could read intercepted Enigma messages before the Germans could! AJ 115
Exchanging Keys • Prior to 1976, all ciphers were “symmetric” • Used the same key to encrypt and decrypt • Problem with all old encryption schemes is the key exchange • Recipient must have the same key as the sender • How do you transmit a secret key over an insecure channel? AJ 115
Public-Key Cryptography • New Directions in Cryptography • Whitfield Diffie & Martin Hellman, 1976 • Proposed using two keys • One to encrypt messages (the public key) • A different key to decrypt (the private key) • Also known as asymmetric cryptography • Two keys are related, but one cannot be derived from the other • Public key can be published AJ 115
The RSA System • Select two prime numbers, p and q • Ex: choose p = 11, q = 3 • Compute n = pq, f = (p-1)(q-1) • Ex: n = 11 3 = 33, f = 10 2 = 20 • Choose e, the encryption key, less than n, so that e and f have no common factors • Ex: choose e = 3 AJ 115
The RSA System • Find d (the decryption key) • Need ( e d / f ) to leave a remainder of 1 • Ex: 3 d / 20 leaves remainder 1 if d = 7 • Key pair is (n,e) and (n,d) • Encryption (public) key is (33, 3) • Decryption (private) key is (33, 7) AJ 115
The RSA System • Encrypting a message • ciphertext = (plaintext)e mod n • Ex: plaintext = 13 • ciphertext = 133 mod 33 = 2197 mod 33 = 19 • Decrypting the message • plaintext = (ciphertext)d mod n • plaintext = 197 mod 33 = 893871739 mod 33 = 13 AJ 115
Why is RSA Secure? • Real versions use very large numbers • Modulus, n, is at least 1024 bits long • About 340 decimal digits • So p and q are each about 200 digits long • Numbers are easy to multiply, but hard to factor • It’s easy to compute n if you know both p and q • It’s almost impossible to factor n into p & q AJ 115
Just How Secure Is It? • No cipher is 100% unbreakable • Except “one-time pads,” but they have other problems • By making the modulus larger, RSA can be made arbitrarily hard to break • With a 2048-bit modulus, all the computing power in the world would take over 70 years to break one cipher AJ 115
What are the Problems? • Asymmetric encryption is S-L-O-W • Can take even powerful computers 1-2 seconds to encrypt or decrypt a message • Can be fooled by someone posing as someone else • If Eve claims to be Bob and publishes “Bob’s” public key, any messages encrypted with it will be readable by Eve, not Bob AJ 115
Speeding Things Up • DES (Data Encryption Standard) • Proposed in 1974 by NSA, IBM • Symmetric cipher • Algorithm can be implemented in hardware • Key very short • 56 bits long (40-bit key and 16-bit header) • Could be broken “by force” with enough computing power (which NSA has) AJ 115
DES and 3DES • Shortness of key used by DES considered a weakness • Newer version is “triple-DES” or 3DES • 136 bits long (120-bit key + 16-bit header) • AES (Advanced Encryption Standard) • Uses 128-bit key • DES, 3DES, and AES are all symmetric AJ 115
SSL • Secure Sockets Layer (SSL) • Invented by Netscape in 1995 • Uses RSA to exchange a “session key” • DES, 3DES, or AES key used for that browser session only • Gets both speed and security • RSA only used to exchange session key • Session key expires when user logs out AJ 115
Digital Certificates • Overcome “spoofing” attack • Perform same function as notary public • Purchase from Certificate Authorities (CAs) • VeriSign, Thawte, Comodo, GeoTrust, … • Contain my public key • “Signed” by the root certificate • Located in your browser AJ 115
Digital Signatures • Asymmetric cryptography can be used to digitally “sign” documents • Achieves all purposes of conventional signature (but better): • Cannot be forged • Cannot be stolen and re-used • Cannot be repudiated • Assume Alice wants to sign a document and send it to Bob. Here goes … AJ 115
Digital Signatures • Alice computes the MD5 (or SHA-1) digest value for the document • She encrypts the (document+digest) combination using her own private key • She then encrypts the previous message using Bob’s public key and sends Bob the result. AJ 115
Digital Signatures • Bob decrypts the message from Alice using his own private key. • He then decrypts the resulting message using Alice’s public key. • He isolates the digest value and compares it with the value he computes for the rest of the message. • If everything matches, he knows that Alice signed this document. AJ 115
Digital Signatures • Can Alice later repudiate her signature? • No, because only she has her private key • Can Bob or Eve forge Alice’s signature? • No, for the same reason • Can Eve steal Alice’s signature and use it to “sign” a different document? • No, because then the digest values wouldn’t match AJ 115
State of the Art • Public-key cryptography allows people to communicate securely even if they have never met • Necessary for electronic commerce • Ciphers cannot be made 100% secure, but they can be made arbitrarily secure • Use longer keys • Both good guys and bad guys can use this technology • Cryptanalysis is essentially obsolete AJ 115