Microsoft Forefront Identity Manager 2010
Microsoft Forefront Identity Manager 2010. Daniel MEYER Enterprise Technology Architect EMEA. Agenda. IdA Concepts MS Strategy FIM Functional Overview FIM Technical Overview Architecture Main Features (How MS IT use FIM) FIM Positionning. Concepts. Identity and Access Management.

Microsoft Forefront Identity Manager 2010
E N D
Presentation Transcript
Microsoft Forefront Identity Manager 2010 Daniel MEYER Enterprise Technology Architect EMEA
Agenda • IdA Concepts • MS Strategy • FIM FunctionalOverview • FIM TechnicalOverview • Architecture • Main Features • (How MS IT use FIM) • FIM Positionning
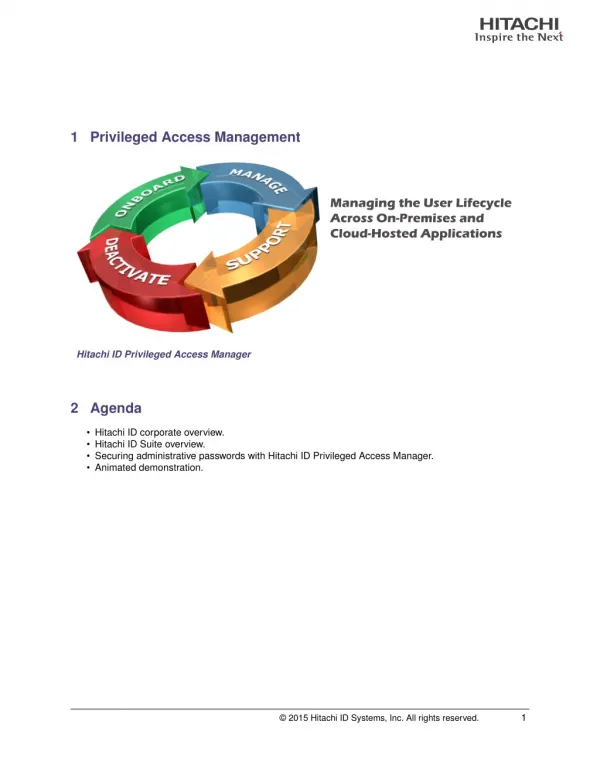
Identity and Access Management Create Provision user Provision credentials Provision resources Retire Policy Management De-provision identities Revoke credentials De-provision resources Policy authoring Policy enforcement Approvals and notifications Audit trails Update Role changes Password and PIN reset Resource requests
Identity & Access Customer Challenges Compliance with regulatory requirements Auditable processes for granting access to resources Reducing help desk burden for end user requests Managing the complexity of distributed identity information Operational Efficiency Compliance Business Agility IT Security Integrated user provisioning & credential management Ensuring that only authorized users can access resources Enabling new high businessvalue scenarios Supporting mergers, acquisitions & reorganizations 5
Microsoft’s Integrated Solutions Delivering TCO in the drive to Dynamic IT Management Simplified and integrated management Identity and Access Systems • Security Threat Mitigation Comprehensive security Cloud Network Application Endpoint Identity Based Access End-to-end access Remote Network Application Information Identity Infrastructure Common platform and infrastructure Username and Credentials Secure Platform Cloud Server Client Mobile Across physical and virtual environments
Encrypting File System (EFS) Forefront Stirling Management BitLocker™ Information Protection Identity & AccessManagement SystemsManagement Microsoft Security: Defense In Depth A well Managed Secure Infrastructure is the key! Services Edge Edge Server Applications Server Applications Network Access Protection (NAP) Client and Server OS Client and Server OS Certificate Lifecycle Management Active Directory Federation Services (ADFS) Mobile Device Manager 2008 TWC Data Protection Manager Configuration Manager 2007 SDL Operations Manager 2007
Business Ready Security Solutions Integrated Security Secure Messaging Secure Collaboration Secure Endpoint Information Protection Identity and Access Management
Business Ready Security Solutions Integrated Security Secure Messaging Secure Collaboration Secure Endpoint Information Protection Identity and Access Management Active Directory®®Federation Services
FIM Manage Identity Operation: • Create, Modify, Delete, Synchronize, Provision Identity Data: • Users*,Groups & DLs,Certificates, SmartCard ... • * Users = Employees, Contractors, Partners, Customers... • Using: • Portal, Policies, Workflow • How: • Manually, automatically, by a scheduling
Forefront Identity Manager 2010 Databases Self-Service integration WindowsLog On LOB Applications Forefront Identity Manager Portal Policy Management Credential Management User Management Group Management Custom IT Departments Directories ISV PartnerSolutions
End User Scenarios Example Scenario Advantages UserManagement • Automatic routing of multiple approvals • Approval process through Office • Audit trail of approvals CFO gives final approval for newuser to access in-scope SOX app Credential Management • Integration with Windows logon • No need to call help desk • Faster time to resolution Self-service smart card provisioning GroupManagement • Automatic updating of business applications • No need to call help desk • Faster time to resolution User changes their cell phone number PolicyManagement • Request process through Office • No waiting for help desk • Faster time to resolution User requests to join secure distribution list for newproduct development 14
IT Administrator Scenarios Example Scenario Advantages UserManagement • Centralized management • Automatic policy enforcement across systems Author policy to require HRapproval for job title change • Generation and delivery of initialone-time use password • Integration of smart cardenrollment with provisioning Credential Management Create workflow to automatically issue passwords and smart cards to new users GroupManagement • Automatic policy enforcement across systems • Management of role changes & retirements Automatically provision new employees with identity, mailbox, and credentials PolicyManagement • Automatic management of group membership • Secure access to departmental resources, with audit trail Design policy to automatically create departmental security groups 15
FIM Architecture Solutions Custom Group Mgmt Credential Mgmt Policy Mgmt User Mgmt FIM Client Experiences FIM-CM Portal Outlook FIM Portal Windows Custom FIM Service and Portal FIM Sync FIM Service FIM-CM Sync DB App DB FIM-CM DB Action Workflow Request Processor Delegation& Permissions AuthN Workflow AuthZ Workflow Adapters Cert Mgmt Identity and data stores Directories Applications Databases E-Mail Systems
Forefront Identity Manager Features UserManagement • SharePoint-based console for policy authoring, enforcement & auditing • Extensible WS– * APIs and Windows Workflow Foundation workflows • Heterogeneous identity synchronization and consistency Credential Management • Heterogeneous certificate management with 3rd party CAs • Management of multiple credential types, including One Time Passwords • Self-service password reset integrated with Windows logon GroupManagement • Integrated provisioning of identities, credentials, and resources • Automated, codeless user provisioning and de-provisioning • Self-service profile management PolicyManagement • Rich Office-based self-service group management tools • Offline approvals through Office • Automated group and distribution list updates 20
How you extend it Customizable Identity Portal SharePoint-based Identity Portal for Management and Self Service Add your own portal pages or web parts Build new custom solutions Expose new attributes to manage by extending FIM schema Choose SharePoint theme to customize look and feel
White pages • The portal includes a white pages view that can be searched against
Creating Users • If you have permission, users can be created within the portal as well • Normally most FTE users will come in through an Identity System (e.g. SAP HR) • Temporary users can be created through the portal
Applying Business Rules to DLs • Business rules and policies can be implemented in a number of ways, for example through the use or dynamic/calculated memberships to groups
Management Policies • Used to define policy within the organisation for sets of data (for example ‘people’)
Management Policies • Here we are saying all users can update and read there own attributes • We can also assign this policy to kick off a workflow if required
Workflow • Workflows can be defined for such things as approvals • We associate workflows with actions such as a group approval
Workflow • Workflows can be defined for such things as approvals • We associate workflows with actions such as a group approval
Workflow • Workflows can be defined for such things as approvals • We associate workflows with actions such as a group approval
User Self Service • Users by default can perform self service on themselves, create groups (that expire after a period of time), and view the white pages
User Self Service • Users by default can perform self service on themselves, create groups (that expire after a period of time), and view the white pages
Password Reset And Synchronization MELISSA PASSWORD SYCHRONIZATION WINDOWSMACHINE ILM “2” iPLANET FINANCEAPPLICATION ACTIVEDIRECTORY FINANCEPORTAL
Connecting to systems • Connecting to systems is done via a Management Agent in the Synchronisation Engine • Included in this is the attributes that you want to make available to the portal and the schema configuration
Synchronisation Rules • Synchronisation rules define relationships and attribute flows to downstream identity systems, they can be configured for inbound, outbound or bidirectional data flow
Connecting and attribute flow • Two ways in Forefront Identity Manager • Via the Management Agent for Attribute flow and provisioning • Via Sync Rules in the Forefront Identity Manager portal • Either can be used based on the deployment scenario, for example we may use provisioning rules and attribute flow via the MA for devices installed out of the box. This reduces the complexity for customers.
Approval processes confirm permission Office 2007 Integration allows group memberships and approvals to be done from Outlook 2007.
FIM ‘Certificate Management’ (CM) Single administration point for smart cards & digital certificates • User self-service capabilities to help reduce helpdesk burden • Configurable policy-based workflows for common tasks • Enroll / renew / update • Personalize smart card • Recover / smart card replacement • Issue temporary / duplicate smart card • Revoke / retire / disable smart card • Detailed auditing and reporting capabilities • Support for centralized, decentralized and self-service scenarios • Extensibility to support additional authentication technologies including one time password (OTP) devices, physical access cards & biometrics • Tightly integrated with Active Directory and Certificate Services Portail CM CM DB Gest. Cert Gestion des certificats
MS IT deployment overview
Key Challenges • 6 Forests, 13 domains • Migration/co-existence with legacy applications • Complex deployment design across multiple scenarios • Initial population of database • Driving password reset registration • First large scale deployment
MSIT Deployment • Goals • Validate FIM’s value proposition • Reduce cost by automating processes • Eliminate custom costly custom solutions • Validate product readiness across the feature sets in a large enterprise environment • Customer proof • Process • Highly collaborative • Cross-functional teams on both sides
Scenario Overview – Password Reset Jill has been out on vacation for a few weeks. As a result, she has forgotten her password and must reset it. Today With FIM • Jill needs to call the helpdesk to reset her password • Jill is able to reset her password without calling the helpdesk Company incurs a significant cost in managing credentials for 175,000 employees like Jill • Microsoft IT maintains a centralized set of policies & common tools • Company needs to maintain different tools for managing the credentials for employees and contractors • Employees can reset their credentials directly from the Windows logon screen or through the FIM 2010 Portal
Define The Problem for MSIT 42,000 X $20 = $850,000 The company incurs a significant cost in managing credentials for employees and contractors Resets/Year = $600,000 Soft costs – Melissa is unproductive for 15 minutes while waiting to get her password reset per yearin savings
Scenario Overview – Group Management • Melissa Meyers has now started her job as an Analyst in the Finance department. As part of her daily tasks she will need to join new groups as well as manage her own project related groups. With FIM Today Melissa goes to the web site to use the custom group management tool Melissa can create/join DLs right from the FIM 2010 Portal Joining groups that need approval require access to the custom group management tool Owners can approve groups via Outlook or the FIM 2010 Portal Calculated groups automatically update membership Dynamic group membership is not available to end users & requires a custom tool
Define the Problem for MSIT Developing and maintaining group management tools costs millions of dollars Support of custom group management tools Complexity of deployment and lack of long term vision Lack of connectivity to group management tool results in soft costs around user productivity Security Group creation causes token bloat Bolt on applications that only administrators have access to, (ADUC) or other group management tools
Define The Problem for MSIT > $3,000,000 Custom software maintenance and upgrades Estimated per yearin savings
Summary: Software for policy-based management of identities,credentials, and resources across heterogeneous environments Provides Office-based self-service tools SharePoint admin console to manage identities Greater productivity through faster time to resolution • Empowers People Reduces costs through automation and self-service Maximizes existing investments in Identity Infrastructure Integrates with familiar developer tools to enable new scenarios Delivers Agility and Efficiency Integrates identity, credential, and access management Rich permissions and delegation model Enables system auditing and compliance Increases Security and Compliance
Resources Learn more about Forefront Identity Manager • FIM 2010 Product Page: www.microsoft.com/fim • ILM 2007 Product Page: www.microsoft.com/ILM2007 Learn about Microsoft Forefront Identity and Security • Forefront Home Page: www.microsoft.com/forefront Evaluate the Identity Manger • Visit www.microsoft.com/fim • To download this presentation click here :
© 2008 Microsoft Corporation. All rights reserved. Microsoft, Windows, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U.S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION.