Biometrics II
Biometrics II. CUBS, University at Buffalo http://www.cubs.buffalo.edu http://www.cedar.buffalo.edu/~govind/CSE717 govind@buffalo.edu. Maintaining Biometric Databases. Enrollment Base truth established through seed documents Positive Enrollment Negative Enrollment Problems in enrollment

Biometrics II
E N D
Presentation Transcript
Biometrics II CUBS, University at Buffalo http://www.cubs.buffalo.edu http://www.cedar.buffalo.edu/~govind/CSE717 govind@buffalo.edu
Maintaining Biometric Databases • Enrollment • Base truth established through seed documents • Positive Enrollment • Negative Enrollment • Problems in enrollment • Biometric System is only as secure as its enrollment • Fake Identities • Duplicate Identities • Quality • The biometric zoo • Sheeps,Goats,Wolves,Lambs
Large Scale Databases • How large is ‘large scale’? • Application • US-VISIT • National ID – Thailand, Hong Kong • Voter Registration – Peru • Accuracy issue • FARN= N*FAR • FRRN = FRR • Number of False accepts scales as O(N2) • Scalability and retrieval • Indexing • Filtering • Binning
Indexing Problem • Biometric template have no natural order • Natural groups cannot be inferred from statistical descriptors
Indexing Problem: Solutions Binning and pruning Natural feature representation
Fingerprint matching Signature matching Hand geometry matching Alice Bob : Alice Bob : Alice Bob : 26 12 : 0.31 0.45 : 5.54 7.81 : Combination algorithm Alice Bob : 0.95 0.11 : Combination of biometric matchers • Combination of the matching results of different biometric features provides higher accuracy.
Alice Bob : 0.95 0.11 : Sequential combination of matchers Fingerprint matching Combination algorithm 1 No Desired confidence achieved? Yes Signature matching Combination algorithm 2 Yes No Desired confidence achieved? Hand geometry matching Combination algorithm 3
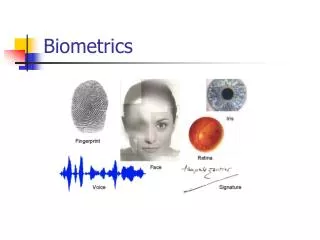
Information Fusion • Multiple sensors • Compensates environmental variation • Multiple samples • Allows interaction induced variation • Multiple instances of the same biometric • Multiple matchers • May use multiple representations • Serial and hierarchical combination • Multi-modal biometrics • Feature level Fusion • Score level Fusion • Decision level Fusion • Loosly coupled integration • Combination of biometrics and tokens
Security of biometric data • Issues in biometrics • Biometrics is secure but not secret • Permanently associated with user • Used across multiple applications • Can be covertly captured • Types of circumvention • Denial of service attacks • Fake biometrics attack • Replay and Spoof attacks • Trojan horse attacks • Back end attacks • Collusion • Coercion
ID : 8809 Attacks on a Biometric System Biometric Sensor Feature Extraction Database Enrollment Feature Extraction Biometric Sensor Matching Authentication Result
Securing biometric templates • Liveness testing • Cancelable biometrics • Signal domain distortion • Feature domain distortion • Hashing • Uses non invertible transform • Watermarking and steganography • Ensures that sensor input can be trusted • Encryption and digital signature • Combines security of encryption with non-repudiation of bometrics • Challenge response systems • Conversational biometrics • CAPTCHAs
Privacy, social and ethical concerns • Aspects of privacy • Secrecy • Solitude • Anonymity • Unintended functional scope • Retinal pattern is capable of revealing diabetes • Hand irregularities can be correlated with genetic defect • This information may be used for discrimination • Unintended application scope • Can compromise anonymity of an individual • Biometric can be used for covert surveillance • Can be used to track purchases leading to spam • Social acceptance • Stigma associated with biometrics • Reduces level of expected privacy
Face recognition Palm verification Key stroke dynamics Speaker recognition Soft biometrics Multimodal biometrics Classifier combination Binning and Indexing Security of biometrics Interchange standards and API Avenues for research
Summary • Enrollment into biometric databases • Large scale databases • Filtering, binning and indexing biometric templates • Combination of classifiers • Multimodal biometrics • Attacks on Biometric System • Securing Biometric Templates • Privacy Social and Ethical Concerns
Thank You ssc5@cedar.buffalo.edu