Linear Cryptanalysis of DES
Linear Cryptanalysis of DES. M. Matsui. Linear Cryptanalysis Method for DES Cipher . EUROCRYPT 93, 1994. The first experimental cryptanalysis of the Data Encryption Standard . CRYPT0 94, 1994. . Linear Approximations.

Linear Cryptanalysis of DES
E N D
Presentation Transcript
Linear Cryptanalysis of DES M. Matsui. Linear Cryptanalysis Method for DES Cipher. EUROCRYPT 93, 1994. The first experimental cryptanalysis of the Data Encryption Standard. CRYPT0 94, 1994.
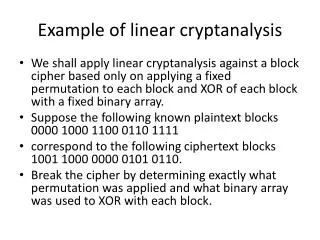
Linear Approximations • A function with one bit output is a linear function over if output is XOR of input bits. • Example: • If the f function in DES is linear then we can break DES. • g has a p-linear approximation if with probability p the output is equal to a linear function. • Example: has a 3/4-linear approximation. • Every function has a ½-approximation.
Using Linear Approximations of DES • Assume that 1 bit of the output has a linear approx. • Example: Assume that if we pick M at random and C=DES(M,K), then with probability 0.51 Attack: • Pick a pair message, encryption M, C= DES(M,K), at random. • Compute and conclude that with probability 0.51. • To increase probability repeat many times and take majority.
Using Linear Approximations of DES How do we find linear approximations in DES? We will consider 3-round DES, without IP and IP-1. We will start with a S-BOX.
The S-Box S5 • Does not look random: • 1,2 ,7,11 appears only in left side • 4,12,13 appear 3 times in left side • 8,10,14 appear 2 times in each side • 0,3,5,9,15 appears only in right side • 6 appears 3 times in right side • The XOR of the numbers in left-side is 1 S5
The f function of DES 17—20
The permutation P We need to trace the bits 17-20 that come from to S5 After P they are bits 3,8,14,25
The f function of DES Bit 26 in k 26 26 17-20 Bits 3,8,14,25
The Expansion function E We need bit 26 – the second bit that goes to S5
The f function of DES Bit 17 in R Bit 26 in k 26 26 17-20 Bits 3,8,14,25
3 Round DES Bits 3,8,14,25 Bit 17 Bit 26 Bits 3,8,14,25 Bits 3,8,14,25 Bit 26 Bit 17 Bit 17 Bits 3,8,14,25
The Attack on 3 Round DES • From first round with probability 52/64 • From third round with probability 52/64 • Thus, with probability (52/64) 2+(12/64)2 0.7 • Finds one bit of the key
Linear cryptanalysis: Learning One Bit • If a bit of the outputs has a 1/2+p linear approximation in i-round DES, then • Get O(1/p2) message, encryption pairs • For each pair compute “the bit” of the key • Take the value that appears more times • Get correct value with high probability • Learn one bit of key • Can do better…
4 Round DES ? Bits 3,8,14,25 Bit 17 • Only 6 bits in K4 affect bit 17 of • With the correct 6 bits the • 3-round approximation holds with • prob. 0.7 • With incorrect 6 bits • is random • Check 26 options of these bits and • find the correct bits • Found 7 bits of key! Bit 26 KK Bit 26 ? Bits 3,8,14,25 Bit 17 K4 4 4 Bits 3,8,14,25
Linear cryptanalysis • If a bit of the outputs has a 1/2+p linear approximation in i-round DES, then we choose O(1/p2) messages in (i+1)-round DES and compute 7 bits of the key. • Can do the same trick with first round and last i-rounds, get another 7 bits • Use exhaustive search to find the other 42 bits.
Known Attacks • 8 rounds: 221 plaintexts (40 seconds) • 12 rounds: 233 plaintexts (50 hours) • 16 rounds: 243 plaintexts (50 days, 12 computers) • Uses two 14-rounds approximation • Using each approximation it finds 13 bits • Finds 30 bits by exhaustive search