Max M. North, Ph.D.
Max M. North, Ph.D. Applicant for the tenure-track faculty position in Management Information Systems March 2006 Southern Polytechnic State University. Teaching Philosophy & Techniques. Extensive Use of Technology Interactive Examples and Discussion Case Studies Assignments and Handouts

Max M. North, Ph.D.
E N D
Presentation Transcript
Max M. North, Ph.D. Applicant for the tenure-track faculty position in Management Information Systems March 2006 Southern Polytechnic State University
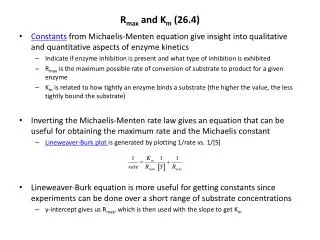
Teaching Philosophy & Techniques • Extensive Use of Technology • Interactive Examples and Discussion • Case Studies • Assignments and Handouts • Presentations (Individual and/or Group) • Brief In-class/Take-home Quizzes and Essays • Research using Scholarly Site (ACM…) • Research using Internet (Cautiously) • Integrated teaching approach • Learner-centered school of thought (Communication of ACM, April 1996). • www.spsu.edu/mgnt/max • Make Learning FUN!
What Are The Issues Facing CIOs Today and How Should They Deal With Them? • Change of terminology… Challenges, rather than Issues
CIO’s ChallengesAcademic-Based Perspective • The Information Systems Investment • The Strategic Business • Globalization • The Information Architecture & Infrastructure • Responsibility and Control
CIO’s ChallengesAcademic Perspective (continued) • The Information Systems Investment Challenge -One of the greatest challenges! -To insure that their companies do indeed obtain meaningful returns on their information systems investments -How can we evaluate our information systems investments? -Are we receiving the return that we should on our investments?
CIO’s ChallengesAcademic Perspective (continued) • The Strategic Challenge -Computer technology has grown more rapidly than the ability of organizations to use it. -Many companies need to make fundamental changes in employee and management behavior and develop new business models etc. -What complementary assets are needed to use information technology effectively?
CIO’s ChallengesAcademic Perspective (continued) • The Globalization Challenge -The rapid growth in international trade and the emergence of a global economy call for information systems that can support both producing and selling goods in many different counties -How can firms understand the business and system requirements of a global economic environment?
CIO’s ChallengesAcademic Perspective (continued) • The Information Architecture and Infrastructure Challenge -Complex information systems which put constraints on business strategy and execution -How can organizations develop an information architecture and information technology infrastructure that can support their goals when business conditions and technologies are changing so rapidly?
CIO’s ChallengesAcademic Perspective (continued) • The Responsibility and Control Challenges -Job Elimination -Personal Data Collections (Privacy and Security) -System Outages -Illegal activities using the Internet -Information Security (more on this later) -How can we design information systems that people can control and understand? -How can organizations ensure that their information systems are used in an ethically and socially responsible manner?
CIO’s ChallengesResearch-Based Perspective Methodology • Online Survey of 545 CIOs (randomly selected) • A broad range of industries including manufacturing, medical/healthcare, insurance, finance, education, wholesale/retail/distribution and federal, state and local government. • Annual revenue of less than $100 million (40%). Between $101 million and $999.9 million (30%). Annual revenue of more than $1 billion (21%).
CIO’s ChallengesResearch Perspective (continued) • What are the five biggest barriers to your effectiveness in your role right now? 1. Unrealistic or unknown expectations 2. Inadequate budgets 3. Shortage of time for strategic thinking/planning 4. Difficulty proving the value of IT 5. Lack of alignment between business goals & IT efforts 6. Risk and uncertainty due to volatile economic conditions 7. Overwhelming pace of technology change 8. Lack of key technical skill sets within IT 9. Lack of business knowledge within IT department
CIO’s ChallengesResearch Perspective (continued) • What are your top five technology priorities? Please guess three now…
CIO’s ChallengesResearch Perspective (continued) • What are your top five technology priorities? 1. Integrating/enhancing systems and processes 2. Ensuring data security and integrity 3. External customer service/relationship management 4. Redesigning/rationalizing the IT architecture 5. Enabling/enhancing e-commerce 6. Automating/optimizing the supply chain 7. Implementing new technologies 8. Scaling IT globally
CIO’s ChallengesResearch Perspective (continued) • What are your top management priorities? 1. Increasing business efficiency through IT-enabled process improvement 2. Aligning IT and business goals 3. Improving internal customer (user) satisfaction 4. Creating competitive advantage through IT 5. Controlling IT costs 6. Staff development/leadership development/developing business skills within IT 7. Ensuring privacy of customer and employee data 8. Measuring and communicating impact of IT
CIO’s ChallengesResearch Perspective (continued) • What impact did IT have on the overall business? 1. Reduced costs through efficiency/increased productivity 2. Enabled growth 3. Enabled business innovation 4. Improved customer (external) satisfaction 5. Created or enabled competitive advantage 6. Enabled global operations 7. Streamlined the supply chain 8. Grew existing revenue
CIO’s ChallengesResearch Perspective (continued) • What impact do you expect IT will have in 2005/2006? Please guess three now…
CIO’s ChallengesResearch Perspective (continued) • What impact do you expect IT will have in 2005/2006? 1. Reduce costs through efficiency/increase productivity 2. Enable business innovation 3. Create or enable competitive advantage 4. Enable growth 5. Improve customer (external) satisfaction 6. Generate/enable new revenue streams 7. Enable global operations 8. Streamline the supply chain 9. Grow existing revenue streams
CIO’s ChallengesResearch Perspective (continued) • On which of the following activities do you spend the most time? [14%] Interacting with your company's CXOs & business executives [12%] Strategic planning [11%] Interacting with IT vendors/outsourcers/service providers [11%] Learning about technologies/making strategic systems decisions [10%] Hiring, developing and managing the IT staff [10%] Leading projects [ 9%] Managing crises/putting out fires [ 8%] Designing/optimizing business processes [ 7%] Budgeting [ 4%] Interacting with outside business partners/suppliers/customers [ 4%] Other
CIO’s ChallengesResearch Perspective (continued) • What personal skills are most critical for success in your role? Please guess three now…
CIO’s ChallengesResearch Perspective (continued) • What personal skills are most critical for success in your role? [28%] Ability to communicate effectively [24%] Strategic thinking and planning [22%] Understanding business processes and operations [ 9%] Understanding industry trends and market forces [ 7%] Negotiation/sales skills [ 6%] Thorough knowledge of technology options [ 4%] Technical proficiency
CIO’s ChallengesResearch Perspective (continued) • What skill set do you believe you will have the greatest need for from new hires? Please guess three now…
CIO’s ChallengesResearch Perspective (continued) • What skill set do you believe you will have the greatest need for from new hires? [41%] Infrastructure technology (knowledge of several platforms & systems) [ 4%] Open source technology [14%] Industry knowledge (knowledge of IT practices in specific industries) [20%] Business knowledge (understanding of business processes, e.g. profit & loss) [10%] Emerging technology (understanding of new or future systems) [11%] Other
CIO’s ChallengesResearch Perspective (continued) • Is your IT investment delivering expected ROI? [ ? %]Yes[ ? %]No Please guess now…
CIO’s ChallengesResearch Perspective (continued) • Is your IT investment delivering expected ROI? [54%]Yes[46%]No
The Summary of Challenges… • Fitting technology to the organization (or vice versa).
…How to deal with challenges? • Case Studies and Research - UPS - Delta - Google - Pepsi - GM - Boeing - …
Use Modern and Practical Approaches • Systems Development Life Cycle (SDLC) • Systems Planning and Selection • Systems Analysis • Systems Design • Systems Implementation • Alternatives to Systems Development Life Cycle • Prototyping • Rapid Application Development (RAD) • CASE • …
General Recommendations… • Communication • Integration (using Enterprise Systems) • Mind Change • Training • Structured Approach • Technology • Decision Support Systems (all levels) • Use Successful Models & Techniques • … • Please list a few more… Assignment
Research and Creative Activity • Human-Computer Interaction/Interface A.K.A. Human Factors • Virtual Reality Technology/Applications Pioneered Virtual Reality Therapy… • Collaboration U.S. Army Research Laboratory Boeing Computer Services NSF, NASA… Ga. Tech (GVU), Purdue University, Clark Atlanta University… • Information Security & Ethics Awareness
Subject in testing phase of the project, performing various operations on the virtual vector container
The virtual scene showing a virtual Vector implementation in 3D graphics using WorldUp product from the Sense8 Corporation
National Center ofAcademic Excellence in Information Assurance Education for academic years 2006-2009 Collaboration with the Clark Atlanta University
Information Security & Ethics Awareness: A challenge for Management Information Systems Presented at ACM/SE 2006 March 11, 2006 Collaboration with the Clark Atlanta University
Abstract • Information Security: A challenge for MIS • Computer security and ethics awareness at Historically Black Colleges and Universities (HBCU). • 465 student volunteers (computer technology courses) • Questionnaire (21 questions) • The majority of the participants had a satisfactory awareness of computer security and ethics • 20% to 52% lack of awareness of computer security is highly risky • 14% to 24% violation of the code of ethics is not acceptable
Introduction • According to a quantitative survey of 435 higher education institutions by EDUCAUSE, only a third have security awareness training for students and faculty. • There is no data that relates to the HBCU student population.
Methodology • Four hundred sixty five (465) Introduction to Computer Technology students volunteered to participate in the survey. • A concise questionnaire consisting of 21 questions was used. • The first part measured the participant’s awareness of computer security. • The second part measured their ethical awareness of computer use.