Identification and Authorization
Learn about user identification, authentication methods, protocols, and challenges like replay attacks. Understand user authentication means and technologies, such as Kerberos and federated identity management.

Identification and Authorization
E N D
Presentation Transcript
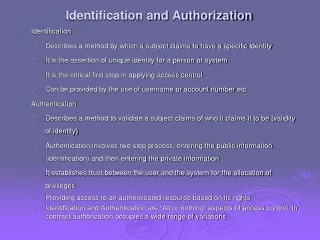
Identification and Authorization • Identification • Describes a method by which a subject claims to have a specific identity • It is the assertion of unique identity for a person or system • It is the critical first step in applying access control • Can be provided by the use of username or account number etc • Authentication • Describes a method to validate a subject claims of who it claims it to be (validity of identity) • Authentication involves two step process; entering the public information (identification) and then entering the private information • It establishes trust between the user and the system for the allocation of privileges • Providing access to an authenticated resource based on its rights • Identification and Authentication are “All or nothing” aspects of access control, in contrast authorization occupies a wide range of variations
User Authentication • fundamental security building block • basis of access control & user accountability • is the process of verifying an identity claimed by or for a system entity • has two steps: • identification - specify identifier • verification - bind entity (person) and identifier • distinct from message authentication
Means of User Authentication • four means of authenticating user's identity • based one something the individual • knows - e.g. password, PIN • possesses - e.g. key, token, smartcard • is (static biometrics) - e.g. fingerprint, retina • does (dynamic biometrics) - e.g. voice, sign • can use alone or combined • all can provide user authentication • all have issues
Authentication Protocols • used to convince parties of each others identity and to exchange session keys • may be one-way or mutual • key issues are • confidentiality – to protect session keys • timeliness – to prevent replay attacks
Replay Attacks • where a valid signed message is copied and later resent • simple replay • repetition that can be logged • repetition that cannot be detected • backward replay without modification • countermeasures include • use of sequence numbers (generally impractical) • timestamps (needs synchronized clocks) • challenge/response (using unique nonce)
One-Way Authentication • required when sender & receiver are not in communications at same time (eg. email) • have header in clear so can be delivered by email system • may want contents of body protected & sender authenticated
One-Way Authentication • have public-key approaches for email • encryption of message for confidentiality, authentication, or both • must know public keys • using costly public-key alg on long message • for confidentiality encrypt message with one-time secret key, public-key encrypted • for authentication use a digital signature • may need to protect by encrypting signature • use digital certificate to supply public key
Using Symmetric Encryption • as discussed previously can use a two-level hierarchy of keys • usually with a trusted Key Distribution Center (KDC) • each party shares own master key with KDC • KDC generates session keys used for connections between parties • master keys used to distribute these to them
Kerberos -Authentication • Kerberos is a de facto authentication standard for heterogeneous networks and used in distributed environments • Its an authentication protocol • It works on a client/server model • Uses Symmetric key algorithm • It has 4 elements necessary for enterprise access control • Transparency, reliability, scalability, security • It provides end-to-end security • Most Kerberos authentications work with shared secret keys, it eliminates the need to share the passwords over the network
Kerberos • provides centralised private-key third-party authentication in a distributed network • allows users access to services distributed through network • without needing to trust all workstations • rather all trust a central authentication server • two versions in use: 4 & 5
Remote User Authentication • use of public-key encryption for session key distribution • assumes both parties have other’s public keys • may not be practical • have Denning protocol using timestamps • uses central authentication server (AS) to provide public-key certificates • requires synchronized clocks
Federated Identity management Process • Cross-certification model • Each entity must authenticate with every other entity is worthy of its trust • The biggest problem is the scalability issue when more entities start participating • Trusted third party model (bridge model) • Each of the participating entity subscribes to the standard and practices of a third-party that manages the verification and due diligence process for all participating companies • The third-party acts a bridge between the participating organizations for identity verification purposes.
Federated Identity Management • use of common identity management scheme • across multiple enterprises & numerous applications • supporting many thousands, even millions of users • principal elements are: • authentication, authorization, accounting, provisioning, workflow automation, delegated administration, password synchronization, self-service password reset, federation • Kerberos contains many of these elements
Network Security and IDS • THREAT TO NETWORK SECURITY A significant security problem for networked system is, or at least unwanted, trespass by users or software. • User trespass can take form of unauthorized logon to a machine or, in case of an authorized user, acquisition of privileges or performance of actions beyond those that have been authorized. • Software trespass can take form of a virus, worm or Trojan horse.
Intruders • significant issue for networked systems is hostile or unwanted access • either via network or local • can identify classes of intruders: • masquerader • misfeasor • clandestine user • varying levels of competence
Types of Intruders • In an early study of intrusion, Anderson identified three classes of intruders: • Masqueraders: An individual who is not authorized to use the computer and who penetrates a system’s access controls to exploit a legitimate user’s account. • Misfeasor: A legitimate user who accesses data, programs or resources for which such access is not authorized, or who is authorized for such access but misuses his or her privileges. • Clandestine user: An individual who seizes supervisory control of the system and uses this control to evade auditing and access controls or to suppress audit actions.
What is an intrusion? • Any set of actions that attempt to compromise the confidentiality, integrity, or availability of a computer resource
Consequences of Intrusion Intruder attacks range from benign to the serious. At the benign end of the scale, there are many people who simply wish to explore internet and what is out there. At the serious end, intruder may attempt following: • Read privileged data. • Perform unauthorized modification to data. • Disrupt the system settings.
What is Intrusion detection system? • Intrusion • Any unauthorized access, not permitted attempt to access/damage or malicious use of information resources • Intrusion Detection • Detection of break-ins and break-in attempts via automated software systems • Intrusion Detection Systems(IDS) • Defense systems, which detect and possibly prevent intrusion detection activities
Why IDS ? Straight Forward Reason to protect data and system integrity. Fact : can not be done with ordinary password and file security Misconception : A network firewall will keep the bad guys off my network, right? My anti-virus will recognize and get rid of any virus I might catch, right? And my password-protected access control will stop the office cleaner trawling through my network after I've gone home, right? So that's it – “I'm fully protected”
Here is the Reality • Anti-virus systems are only good at detecting viruses they already know about • Passwords can be hacked or stolen or changed by other • Firewalls DO NOT recognize attacks and block them • Simply a fence around your network • no capacity to detect someone is trying to break-in(digging a hole underneath it) • Can’t determine whether somebody coming through gate is allowed to enter or not. • Roughly 80% of financial losses occur hacking from inside the network “BEWARE OF INTERNAL INTRUDERS” • Example : In April 1999, many sites were hacked via a bug in ColdFusion. All had firewalls to block other access except port 80. But it was the Web Server that was hacked.
Intrusion Detection Systems (IDS) • Intrusion detection is the process of identifying and responding to malicious activity targeted at resources • IDS is a system designed to test/analyze network system traffic/events against a given set of parameters and alert/capture data when these thresholds are met. • IDS uses collected information and predefined knowledge-based system to reason about the possibility of an intrusion. • IDS also provides services to cop with intrusion such as giving alarms, activating programs to try to deal with intrusion, etc.
Functions of IDS • An IDS detects attacks as soon as possible and takes appropriate action. • An IDS does not usually take preventive measures when an attack is detected. • It is a reactive rather than a pro-active agent. • It plays a role of informant rather than a police officer.
Principles of Intrusion Detection Systems • An IDS must run unattended for extended periods of time • The IDS must stay active and secure • The IDS must be able to recognize unusual activity • The IDS must operate without unduly affecting the system’s activity • The IDS must be configurable
Typical intrusion scenario -Find as much as info. As possible -who is lookup and DNS Zone transfers -Normal browsing ; gather important info. Information Gathering -ping sweeps, port scanning -web server vulnerabilities -version of application/services Further Information Gathering -start trying out different attacks -try to find misconfigured running services -Passive Attack / Active Attack Attack ! -install own backdoors and delete log files -replace existing services with own Trojan horses that have backdoor passwords or create own user accounts Successful Intrusion • Steal confidential information • Use compromised host to lunch further attacks • - Change the web-site for FUN Fun and Profit
Intrusion Techniques • aim to gain access and/or increase privileges on a system • basic attack methodology • target acquisition and information gathering • initial access • privilege escalation • covering tracks • key goal often is to acquire passwords • so then exercise access rights of owner
Password Guessing • one of the most common attacks • attacker knows a login (from email/web page etc) • then attempts to guess password for it • defaults, short passwords, common word searches • user info (variations on names, birthday, phone, common words/interests) • exhaustively searching all possible passwords • check by login or against stolen password file • success depends on password chosen by user • surveys show many users choose poorly
Password Capture • another attack involves password capture • watching over shoulder as password is entered • using a trojan horse program to collect • monitoring an insecure network login • eg. telnet, FTP, web, email • extracting recorded info after successful login (web history/cache, last number dialed etc) • using valid login/password can impersonate user • users need to be educated to use suitable precautions/countermeasures
Intrusion Detection • inevitably will have security failures • so need also to detect intrusions so can • block if detected quickly • act as deterrent • collect info to improve security • assume intruder will behave differently to a legitimate user • but will have imperfect distinction between intruder and user
Approaches to Intrusion Detection • statistical anomaly detection • rule-based detection • Audit Records
Audit Records • fundamental tool for intrusion detection • native audit records • part of all common multi-user O/S • already present for use • may not have info wanted in desired form • detection-specific audit records • created specifically to collect wanted info • at cost of additional overhead on system
Statistical Anomaly Detection • threshold detection • count occurrences of specific event over time • if exceed reasonable value assume intrusion • alone is a crude & ineffective detector • profile based • characterize past behavior of users • detect significant deviations from this • profile usually multi-parameter
Audit Record Analysis • foundation of statistical approaches • analyze records to get metrics over time • counter, gauge, interval timer, resource use • use various tests on these to determine if current behavior is acceptable • mean & standard deviation, multivariate, markov process, time series, operational • key advantage is no prior knowledge used
Rule-Based Intrusion Detection • observe events on system & apply rules to decide if activity is suspicious or not • rule-based anomaly detection • analyze historical audit records to identify usage patterns & auto-generate rules for them • then observe current behavior & match against rules to see if conforms • like statistical anomaly detection does not require prior knowledge of security flaws
Rule-Based Intrusion Detection • rule-based penetration identification • uses expert systems technology • with rules identifying known penetration, weakness patterns, or suspicious behavior • compare audit records or states against rules • rules usually machine & O/S specific • rules are generated by experts who interview & codify knowledge of security admins • quality depends on how well this is done
Base-Rate Fallacy • practically an intrusion detection system needs to detect a substantial percentage of intrusions with few false alarms • if too few intrusions detected -> false security • if too many false alarms -> ignore / waste time • this is very hard to do • existing systems seem not to have a good record
Distributed Intrusion Detection • traditional focus is on single systems • but typically have networked systems • more effective defense has these working together to detect intrusions • issues • dealing with varying audit record formats • integrity & confidentiality of networked data • centralized or decentralized architecture
Honeypots (Intrusion Prevention) • decoy systems to lure attackers • away from accessing critical systems • to collect information of their activities • to encourage attacker to stay on system so administrator can respond • are filled with fabricated information • instrumented to collect detailed information on attackers activities • single or multiple networked systems
Password Management (Intrusion Prevention) • front-line defense against intruders • users supply both: • login – determines privileges of that user • password – to identify them • passwords often stored encrypted • should protect password file on system
Managing Passwords - Education • can use policies and good user education • educate on importance of good passwords • give guidelines for good passwords • minimum length (>6) • require a mix of upper & lower case letters, numbers, punctuation • not dictionary words • but likely to be ignored by many users
Managing Passwords - Computer Generated • let computer create passwords • if random likely not memorisable, so will be written down (sticky label syndrome) • even pronounceable not remembered • have history of poor user acceptance
Managing Passwords - Reactive Checking • reactively run password guessing tools • note that good dictionaries exist for almost any language/interest group • cracked passwords are disabled • but is resource intensive • bad passwords are vulnerable till found
Managing Passwords - Proactive Checking • most promising approach to improving password security • allow users to select own password • but have system verify it is acceptable • simple rule enforcement compare against dictionary of bad passwords • use algorithms