Ransomware
Ransomware. Pirating Cyber Style. Overview. What is Ransomware ? History CryptoLocker BlackHole Exploit Kit. Ransomware. Stops PC from Running Often Called “FBI Moneypak ” or “FBI Virus” Two Types Lock Screen Ransomware Locks Screen so System Cannot be Used Encryption Ransomware

Ransomware
E N D
Presentation Transcript
Ransomware Pirating Cyber Style
Overview • What is Ransomware? • History • CryptoLocker • BlackHole Exploit Kit
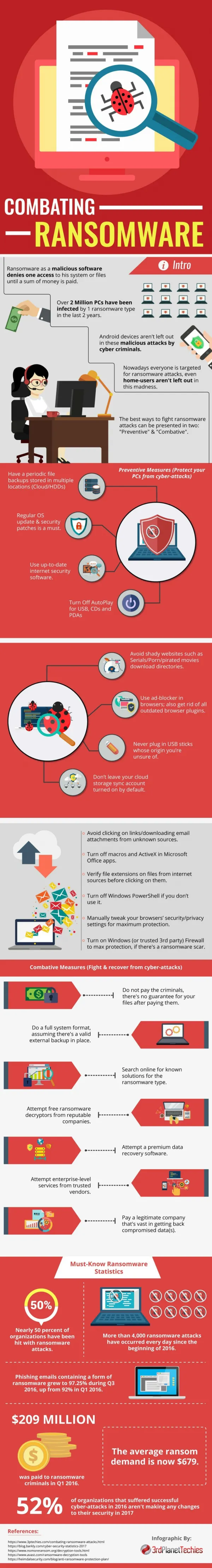
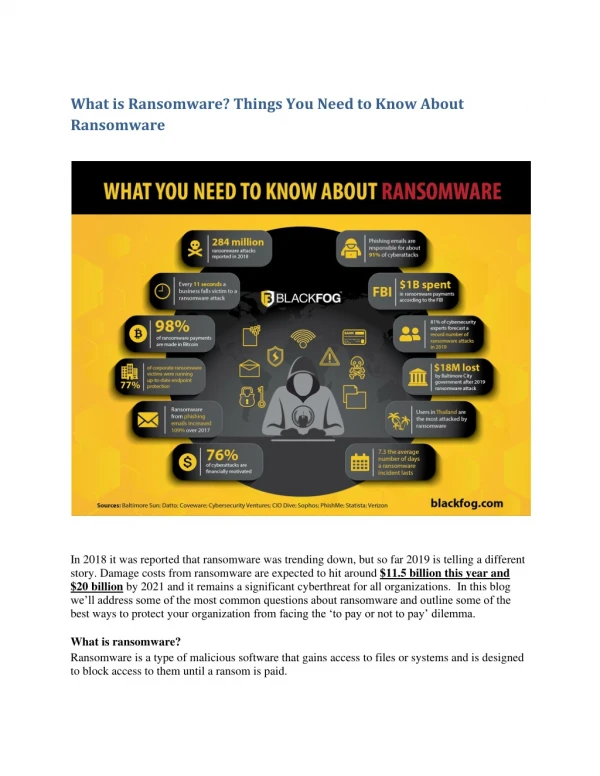
Ransomware • Stops PC from Running • Often Called “FBI Moneypak” or “FBI Virus” • Two Types • Lock Screen Ransomware • Locks Screen so System Cannot be Used • Encryption Ransomware • Locks Files so They Cannot be Accessed • Uses Scare Tactics • Goal Extort Money from Victim
History • PC Cyborg Trojan • Creator Dr. Joseph Popp • Released 1989 • Encrypt All Files on C Drive • Krotten • Released 2006 • Disabled Nearly All Files • Preyed on Windows Directory
History • WinLock • Originated in Russia • Restricts Access to System • Displays Pornographic Images • Reveton • First Seen in 2012 • “Police Trojan” • Engaged in Illegal Activity • Send Fee
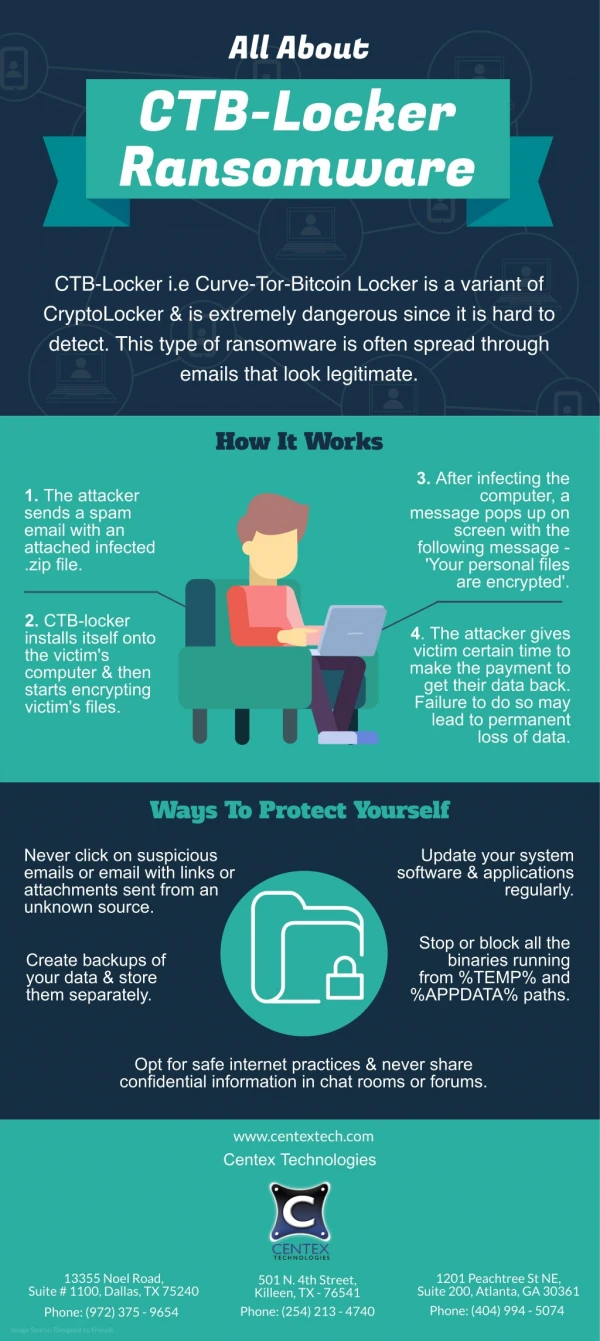
History • CryptoLocker • First Seen 2013 • Use 2048-Bit RSA Key • Private Key Held Threatened Erase • Most Common Infection Mode – E-Mail Attachment • Will Run in Safe Mode
CryptoLocker • Found to have used 2764 unique victim IP's contacting the sinkholeddomains • Highest number was recorded on Wednesday October 16, with 1266 unique IP addresses
CryptoLocker • Top 30 countries infected
CryptoLocker • Countermeasures • Do Not Open Attachments Unless Source is Verified • Up-to-Date Antivirus – Maybe to Late • Configure System so CryptoLocker Cannot Run • Block Executables from Running in %AppData% Directory • Block Executables from Running in %AppData%\* Directory • Block WinRAR Attachments from Opening %Temp%\Rar\*.exe • Block 7zip Attachments from Opening %Temp%\7z\*.exe • Block WinZip Attachments from Opening %Temp%\wz*\*.exe • Block Built-in Zip Support from Opening %Temp%\*.zip\*.exe
BlackHole Exploit Kit • Launched in late 2010 – Russian Hacker • Currently Most Popular Exploit Kit • MySQL Backend • Auto Update • Contains Many Recent Java Exploits • Contains Exploit for CVE-2012-1889 (MS XML) • 0-Day at the time • Good JavaScript Obfuscation • Many Different Payloads can be Carried
BlackHole Exploit Kit • How It Works:
BlackHole Exploit Kit • August to September 2012 Payloads: Money Collecting Information Stealing Click Fraud
Conclusions • Best Option, Avoid Getting Infected • Keep Good Backups – Even in Homes • Avoid Paying Ransom • Paying Only Encourages More Ransomware / Malware
References • History: http://www.microsoft.com/security/portal/mmpc/shared/ransomware.aspx http://nakedsecurity.sophos.com/2013/02/26/technical-paper-exploring-the-history-and-technology-of-ransomware/ http://www.computerweekly.com/news/2240102909/Ransomware-and-computer-blackmail-viruses-a-history http://ezfimblog.com/2013/10/28/cryptolocker-rears-its-ugly-head-a-history-of-ransomware/ http://www.theoaklandpress.com/lifestyle/20131103/how-to-break-your-computer-free-of-ransomware
References • Reveton: http://threatpost.com/reveton-ransomeware-adds-password-purloining-function • CryptoLocker: http://www.virusbtn.com/blog/2013/11_18.xml?rss http://www.securelist.com/en/blog/208214109/CryptoLocker_Wants_Your_Money http://www.thirdtier.net/downloads/NewCryptolockerWarning.pdf http://www.thirdtier.net/downloads/CryptolockerWaystoaddExemptions.pdf
References • Blackhole: http://nakedsecurity.sophos.com/2012/03/29/exploring-the-blackhole-exploit-kit/ http://nakedsecurity.sophos.com/exploring-the-blackhole-exploit-kit/ http://krebsonsecurity.com/tag/blackhole-exploit-kit/ http://nakedsecurity.sophos.com/2012/11/30/technical-paper-blackhole/ http://nakedsecurity.sophos.com/2013/01/16/technical-paper-black-hole-2/ http://media.blackhat.com/bh-us-12/Briefings/Jones/BH_US_12_Jones_State_Web_Exploits_Slides.pdf