Authentication & Authorisation for JISC and UK e-Science
100 likes | 121 Vues
Explore the challenges and solutions for common services supporting academia in teaching, research, and community engagement. Discussion includes internal resources, institution-to-institution interactions, and national-level authentication and authorization processes. Delve into attribute-based frameworks and potential future developments in middleware standards.

Authentication & Authorisation for JISC and UK e-Science
E N D
Presentation Transcript
Authentication & Authorisation for JISC and UK e-Science Alan Robiette, JISC Development Group <a.robiette@jisc.ac.uk>
Context • Universities and colleges engage to varying degrees in • Teaching and learning (e-Learning) • Research (e-Science) • Community links (business, culture, sport including e-Business) • Information management of their own (e-Administration, e-Libraries) • How far can all be supported by common services? Akenti Workshop, MIMAS
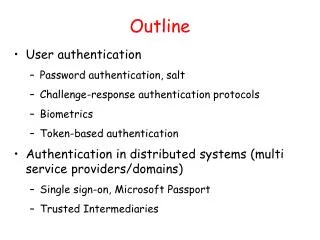
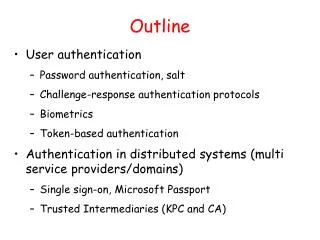
Core middleware • Mostly about identifying and describing people and resources and how they interrelate • The people part is a fairly well understood problem • Staff, students, other categories • Faculties, departments, rôles within these • Groups of various kinds Akenti Workshop, MIMAS
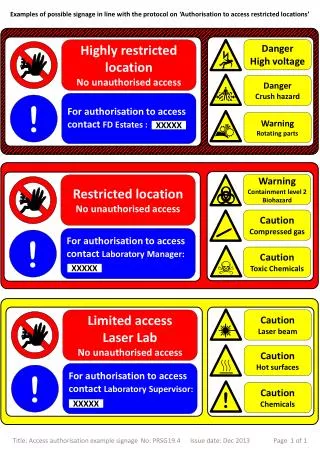
But the resources? • Range of scenarios with widely varying characteristics • Internal resources (very diverse) • Institution to institution (shared courses, research collaborations) • Institution to national-scale service (examples include JISC content, Grid) • Institution to other body (ad hoc business or similar relationship) • The wider Internet Akenti Workshop, MIMAS
Internal resources • Many resources • Every kind of use condition • Institutions have to take their own internal management decisions • Possible advisory rôles for JISC • e.g. Recommended approaches to “single sign-on” • Recommendations on interfacing to national middleware infrastructure Akenti Workshop, MIMAS
Institution to institution • Interestingly the most likely use conditions may be by named group • e.g. Research team, or student class • Attribute-based frameworks like Akenti or Permis well suited to this • Shibboleth also deals with this case, but attribute namespaces are a problem Akenti Workshop, MIMAS
The national level • Access management for JISC content • Authorisation by site (mostly) • Currently Athens – but where next? • The Grid: quite different (for now) • Authentication requires certificates • Authorisation mainly by VO; many competing solutions • Attribute-based frameworks could provide the link (see later) Akenti Workshop, MIMAS
The wider world • Few middleware standards at present • So current solutions are more or less bound to be ad hoc • Will we get standards emerging in time, e.g. via web services? • SAML, XACML, WS-Security, eBXML, XrML/ODRL, etc. • Maybe but it could take a long time Akenti Workshop, MIMAS
What next? • How far could the scope of the attribute certificate approach be extended? Some questions: • Creation and management of attribute certs on a large scale? • Interfaces to local authentication schemes? • Interfaces to service points (including commercial service providers) • Performance? Akenti Workshop, MIMAS