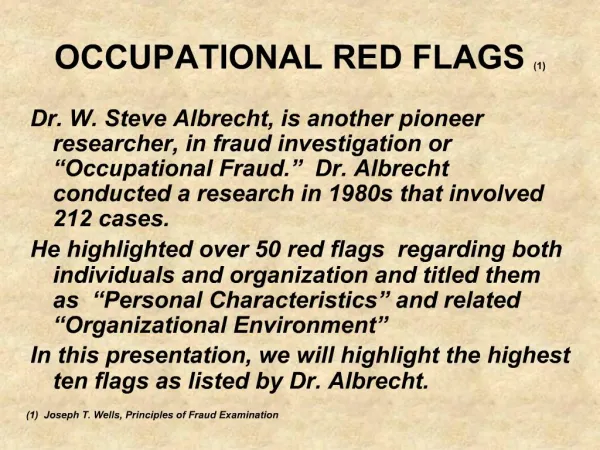
Phishing Attack Red Flags: Discover the Common Indicators
0 likes | 16 Vues
Protect yourself from phishing attacks! In this PPT, you will uncover common indicators of phishing attacks and learn how to protect yourself and your confidential information. Learn the secrets behind detecting these malicious attempts at stealing data and arm yourself with the knowledge needed to stay safe online. Watch now!<br>Click to know more: https://jettbt.com/news/uncovering-common-indicators-of-phishing-attacks/

Phishing Attack Red Flags: Discover the Common Indicators
E N D
Presentation Transcript
In the digital age, phishing attacks have become increasingly prevalent and can pose a significant threat. Let's explore the common indicators of phishing attacks. JETTBT.com
Sense of Urgency Requests for Personal Information Be wary of emails that create a false sense of urgency, pressuring you to act quickly. Red flags include emails requesting sensitive information such as login credentials, bank account details, or social security numbers. JETTBT.com
Spelling and Grammar Errors Mismatched URLs Phishing emails often have noticeable mistakes, indicating that they are not from a professional source. Hovering over links provided in the email can reveal if the URL matches the link's anchor text or sender's claimed identity. JETTBT.com
Unexpected Attachments Too Good to Be True Offers Unsolicited emails with attachments may contain malware and should be treated with caution. Offers that seem overly beneficial or too good to be true are often signs of a phishing attack. JETTBT.com
Stay vigilant and outsmart phishing attacks with our IT service in Atlanta at JETT Business Technology. From cybersecurity to managed services, we have the solutions to protect your business! JETTBT.com
Reach Us At JETT Business Technology 1060 Windward Ridge Pkwy, Suite 150, Alpharetta, GA 30005 678 387 5717 jmartin@jettbt.com JETTBT.com