Middleware Planning and Deployment 101: Setting the Stage
600 likes | 844 Vues
Middleware Planning and Deployment 101: Setting the Stage. Keith Hazelton, University of Wisconsin-Madison/Internet2 Renee Woodten Frost, Internet2/University of Michigan. Agenda. Introductions Middleware: What and Why? Concepts and Architectures Discussion Break

Middleware Planning and Deployment 101: Setting the Stage
E N D
Presentation Transcript
Middleware Planning and Deployment 101: Setting the Stage Keith Hazelton, University of Wisconsin-Madison/Internet2 Renee Woodten Frost, Internet2/University of Michigan
Agenda • Introductions • Middleware: What and Why? • Concepts and Architectures • Discussion • Break • Building a Business Case • Discussion • Research and Resources Middleware Planning and Deployment 101 2
MW 101 Outcomes • Understand what middleware is • Recognize the value of a common middleware architecture • Begin planning for your own business case Middleware Planning and Deployment 101 3
Middleware in Action Middleware Planning and Deployment 101 4
Dr. Alice Agnew has just been hired to Chair the Dept. of Physiology and is very anxious to get access to campus IT resources such as e-mail, calendar, web services and the mainframe and cannot wait for the requisite 3-5 business days it takes to get the accounts setup. Since IT already knows of her through the HR system, she can use a self-service interface to accomplish this goal. And because her new institution has her new credentials, she does not need to give her research consortium new credentials. Middleware Planning and Deployment 101 5
Dr. Alice Agnew • Self-registration • Minimal time delay for enabling services • Administrative data flows to research applications • Administrative and security services integration • Privacy trust • Inter-organizational impact • University vouches for and acts on behalf of Alice Middleware Planning and Deployment 101 6
Mary has been reported to the Dean of Students for plagiarism. Through the campus portal, the Dean with authorization, accesses the Student Information System, where he searches for Mary’s record. He places an electronic “hold” on it and sends an e-mail to Mary requesting her presence at a preliminary discipline hearing. Minutes later, Mary cannot check out library books, enter restricted labs, use the student health facilities, or access her computer files. After reviewing Mary’s case, the Dean finds the accusation in error and removes the “hold,” restoring Mary’s access within minutes. Middleware Planning and Deployment 101 7
Mary • Decision maker performs action • Integration of services • Increased security • Status change affects service offerings • Short-time to disable and enable services • Suite of services Middleware Planning and Deployment 101 8
Sam is taking a class in geneticsat Alpha U and needs to do some research for a paper. At lunch, he goes online to access a restricted EBSCO database AU shares with Beta U. A window pops up in the browser asking if it’s okay for AU to give EBSCO information about his status --- only students from subscribing institutions can access the database. He clicks ok, knowing that only his status is passed, not his name or contact information. The browser then loads the restricted website. Middleware Planning and Deployment 101 9
Sam • Privacy trust • Sam controls personal information flow • Administrative and security services integration • Inter-campus access • University vouches for and acts on behalf of Sam Middleware Planning and Deployment 101 10
What is IT being asked to do? • One stop for university services (portal) integrated with course management systems • Email-for-life • Automatic creation and deletion of computer accounts • Submission and/or maintenance of information online • Privacy protection Middleware Planning and Deployment 101 11
More on the “to do” list • Multi-campus scanning electron microscopes • Integrated voicemail, email, and faxmail for Advancement staff • Secure PDA and wireless support • All-campus email announcements (spam) • Expensive library databases shared with other schools by joint agreement • Browser or desktop preferences follow you Middleware Planning and Deployment 101 12
What questions are common to these scenarios? • Are the people using these services who they claim to be? • Are they a member of our campus community? • Have they been given permission? • Is their privacy being protected? What is the answer…? Middleware Planning and Deployment 101 13
Enterprise Middleware Definitions Middleware Planning and Deployment 101 14
Middleware • Specialized networked services that are shared by applications and users • A set of core software components that permit scaling of applications and networks • Tools that take complexity out of application integration • A second layer of the IT infrastructure, sitting above the network • A land where technology meets policy • The intersection of what networks designers and applications developers each do not want to do Middleware Planning and Deployment 101 15
Map of Middleware Land Middleware Planning and Deployment 101 16
What is middleware? • Suite of campus-wide security, access, and information services • Integrates data sources and manages information about people and their contact locations • Establishes electronic identity of users • Uses administrative data to assign affiliation and gives permission to use services based on that role Middleware Planning and Deployment 101 17
Definitions: Identifiers Identifiers– your electronic identification • Multiple names and corresponding information in multiple places • Single unique identifier for each authorized user • Names and information in other systems can be cross-linked to it • Admin systems, library systems, building systems Middleware Planning and Deployment 101 18
Definitions: Authentication Authentication – maps the physical you to an electronic identifier • Password authentication most common • Security need should drive authentication method • Distance learning and inter-campus applications Middleware Planning and Deployment 101 19
Definitions: Authorization Authorization services – allowing you access to data and services • Affiliated with the school (role) • Permitted to use the services based on that role Middleware Planning and Deployment 101 20
Definitions: Enterprise Directory Services Enterprise Directory services - where your electronic identifiers are reconciled and basic characteristics are kept • Very quick lookup function • Machine address, voice mail box, email box location, address, campus identifiers Middleware Planning and Deployment 101 21
What IT needs to do Determine who you are Determine what resources you can use Middleware Planning and Deployment 101 23
What IT needs to do Possible ways it might do that • Ask you to login and look up info in its own database. • Ask you to login in and look up info in a common database. • Trust some other source to assert needed info (and other source might ask you to login). Examples • Videoconference: current network address • Video for course: enrolled in the course • Email or calendar: University username • Library resource: current member of the set of licensees Middleware Planning and Deployment 101 24
Pause for some terminology • Identity: set of attributes. • Attributes: specific information stored about you. • Authentication: process used to prove your identity. Often a login process. • Authorization: process of determining if policy permits an intended action to proceed. • Customization: presentation of user interface (UI) tailored to user’s identity. Middleware Planning and Deployment 101 25
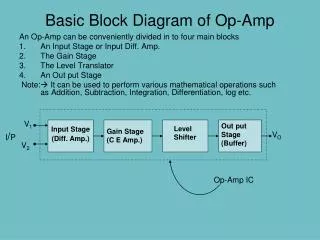
Three service architectures:#1 Stovepipe (or Silo) Service performs its own authentication. Consults own database for authorization and customization attributes. service authN attrs Middleware Planning and Deployment 101 26
#1 Stovepipe (or Silo) Architecture Characteristics Stovepipes authentication and attribute services are run by separate offices. • Environment is more challenging to users, who may need to contact each office to arrange for service. • No automated life cycle management of resources. • Per-service identifiers and security practices make it more difficult to achieve a given level of security across the enterprise. Middleware Planning and Deployment 101 27
Three service architectures:#2 Integrated Service refers authentication to and obtains attributes for authorization and customization from enterprise infrastructure services. authentication service service1 service2 attribute service An Organization Middleware Planning and Deployment 101 28
#2 Integrated Architecture Characteristics Enterprise authentication and attribute services are run by a central office. • All attributes known by the organization about a member can be integrated and made available to services. • Automated life cycle resource management is possible across the enterprise. • Common identifiers across integrated services make an easier and more secure user environment. Middleware Planning and Deployment 101 29
Three service architectures:#3 Federated Service refers authentication to and obtains attributes for authorization and customization from possibly external infrastructure services. authentication service service attribute service Organization 1 Organization 2 Middleware Planning and Deployment 101 30
#3 Federated Architecture Characteristics • Federated authentication and attribute services rely on participating organization’s enterprise services. • Inter-organizational applications such as Grids and digital-library content provision are integrated with and facilitated by enterprise services. Middleware Planning and Deployment 101 31
Middleware Initiative Objective Help prepare campuses to implement core middleware for an integrated and ultimately a federated architecture. authentication service service1 service2 attribute service An Organization Middleware Planning and Deployment 101 32
Core middleware for an integrated architecture Middleware Planning and Deployment 101 33
Vignettes Revisited Middleware Planning and Deployment 101 34
Vignette analysis Set of vignettes portray: • Seamlessness of transitions between services • Independence of location of service or user • Suites of services designed to support activities of different constituencies • Absence of need to make prior arrangement for resources required to enable services • Services rendered in airport waiting areas remotely Middleware Planning and Deployment 101 35
Provisioning Vignette: Dr. Alice Agnew begins as department chair<to model> authN Metadirectory HRS attrs Acct Init Service Middleware Planning and Deployment 101 36
Integrated Services Vignette: Mary accused of plagiarism<to model> Mailbox Lib Proxy authN Files attrs Building access Health Facilities Middleware Planning and Deployment 101 37
Federated/Restricted Resources Vignette: Sam using remote, online database <to architectures> Content Provider Database1 Federation University Database 2 University Middleware Planning and Deployment 101 38
Refreshment Break Middleware Planning and Deployment 101 39
Business Case Components By definition, middleware cannot be effective unless it maps closely to an institution’s business policies and practices. In this context, a strong business case will… • Outline the Institution-specific Drivers • Articulate the Opportunities & Challenges • Define the Benefits • Enumerate the Costs Middleware Planning and Deployment 101 41
Groups to Consider • Business case audience • Select stakeholders and possible champions • Stakeholders • Executive Leadership • Business and Finance VPs • HR Directors and Registrars • CIOs • IT staff • Program Directors and Data Stewards • Auditors and Risk Managers • Faculty • Staff • Students Middleware Planning and Deployment 101 42
Institution-specific Drivers • Internal Drivers • Specific application(s) • Financial • User expectations • External Drivers • Federal/state legislation • E-enterprise functions • Inter-institutional collaboration Middleware Planning and Deployment 101 43
Opportunities • Legislative pressure to reduce paperwork, secure information, and deploy electronic services (grants, financial aid, HIPAA, etc.) • Interdisciplinary and inter-institutional research and collaboration • Changing needs of teaching and learning • User expectations of access to technology • Budgetary pressures Middleware Planning and Deployment 101 44
Benefits to the Institution • Economies for central IT - reduced account management, tighter network security… • Economies for distributed IT - reduced administration, access to better information, easier integration of depart. applications... • Improved services for students and faculty - access to scholarly information, control of personal data, reduced legal exposures... • Participation in future shared environments - Grids, videoconferencing, digital libraries, etc. • Participation in new collaborative initiatives - Shibboleth, Inter-institutional resource sharing… Middleware Planning and Deployment 101 45
Benefits: Specifically . . • Achieves Economies for Central and Distributed IT organizations • Access to primary user identity sources such as HR, Payroll, SIS, and secondary sources such as library, parking, alumni assoc., etc. can be more effectively managed by fewer people saving time and money • Access to any one of these services can be enabled or disabled more readily • Access to a range of services can be accomplished more quickly and in a more coordinated manner • Deployment time for new applications is reduced Middleware Planning and Deployment 101 46
Benefits: Specifically . . • Enhanced Security • A secure enterprise directory can: • Be used to manage access to multiple apps/services (web, remote access, etc.) to the entire institutional community • Facilitate differential access to wireless ports, restricted content, restricted listservs, etc. • Allow identity management to be administered by fewer staff • Simplified Network and on-line service access • A common middleware infrastructure can enable single sign-on access to a larger range of customized and personalized services Middleware Planning and Deployment 101 47
Challenges • Investing the time and effort for planning, review and negotiation • Surviving the politics of reviewing/revising data stewardship policies and procedures • Resource reallocation – People and $$! • Covering up-front costs • Finding $$ to build/maintain data feeds from authoritative data sources to central directory • Potential legal risk WRT publishing personal data in white pages Middleware Planning and Deployment 101 48
Expected Costs to the Institution • Modest increases in capital equipment and staffing requirements for central IT • Considerable time and effort to conduct campus wide planning and vetting processes • One-time costs to retrofit some applications to new central infrastructure • One-time costs to build feeds from legacy source systems to central directory services • The political wounds from the reduction of duchies in data and policies Middleware Planning and Deployment 101 49
Enterprise Directory Costs • Phase 1: Building the Enterprise Directory • Hire new staff vs. Repurpose current staff • New equipment/software vs. Use of existing resources • Phase 2: Deploying Applications • Application dependent, but ROI is high considering: • Cost Savings • Lost Productivity • Increased Opportunity • Increased Security Middleware Planning and Deployment 101 50