802.11 Enhancements and Applications
530 likes | 884 Vues
802.11 Enhancements and Applications. 802.11n, 802.11p, 802.11r, 802.11s, 802.11y. 802.11n. 802.11. 802.11n. Overview Certification, Products Performance Summary. 802.11n overview. Adds MIMO to WLAN OFDM Operate in either UNII or ISM bands Status: In Ballot May get held up by IP

802.11 Enhancements and Applications
E N D
Presentation Transcript
802.11 Enhancements and Applications 802.11n, 802.11p, 802.11r, 802.11s, 802.11y
802.11n 802.11
802.11n • Overview • Certification, Products • Performance • Summary
802.11n overview • Adds MIMO to WLAN OFDM • Operate in either UNII or ISM bands • Status: • In Ballot • May get held up by IP • http://arstechnica.com/news.ars/post/20070924-dark-australian-patent-cloud-looms-over-802-11n-spec.html • CSIRO (http://www.csiro.au/) holds some key IP, hasn’t signed letter of assurance, has history of WiFi lawsuits and seeking injunctions • Last publicly available draft • Enhanced Wireless Consortium (merger of TGnSync and WWiSE) • http://www.enhancedwirelessconsortium.org/home/EWC_PHY_spec_V127.pdf (PHY) • http://www.enhancedwirelessconsortium.org/home/EWC_MAC_spec_V124.pdf (MAC) Streaming Home Multimedia (HDTV) Source: http://www.tgnsync.org/products
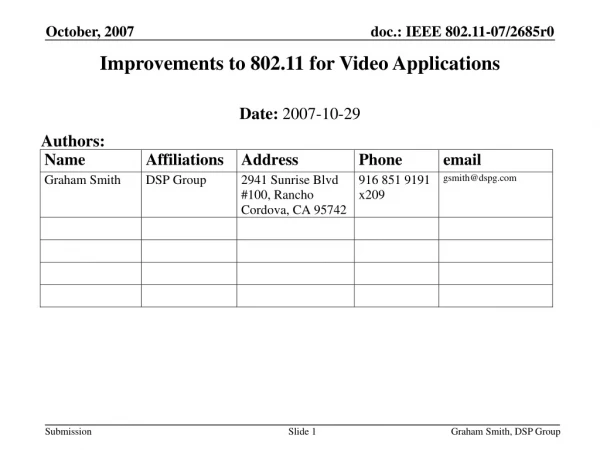
802.11n PHY (in 1 slide) • MIMO evolution of 802.11 OFDM PHY • Up to 4 antennas per device • 20 and 40MHz channels • Fully interoperable with legacy 802.11a/b/g • 288 Mbps in 20MHz and 600 Mbps in 40MHz (64 QAM, 4 spatial streams, 1/2 guard interval) • Claim of 100 Mbps in real throughput • Optional enhancements • Transmit beamforming with negligible overhead at the client • Advanced channel coding techniques (RS) • Space Time Block Coding (Alamouti and others) • 1/2 guard interval (i.e., 400ns instead of 800 ns) • 7/8 rate coding http://www.enhancedwirelessconsortium.org/home/EWC_PHY_spec_V127.pdf
802.11n MAC Features • Supports 802.11e (QoS) • Frame aggregation • Single and multiple destinations • Bi-directional data flow • Link adaptation with explicit feedback and control of channelsounding packets • Protection mechanisms • For seamless interoperability andcoexistence with legacy devices • Channel management • Including management of 20/40MHzoperating modes • Channel estimation and feedback • Power management for MIMO receivers • Data aggregation Broadcom, “802.11n: Next-Generation Wireless LAN Technology,” White Paper, April 06
Distributed coordination function will fail if devices cannot interpret packets Much more spectrum used by 802.11n Three packet modes to support legacy equipment Legacy (all legacy) Mixed (some legacy, some 802.11n) Green Field (all 802.11n) Spectrum usage LM – Legacy Mode – equivalent to 802.11a/g HT-Mode – In HT mode the device operates in either 40MHz bandwidth or 20MHz bandwidth and with one to four spatial streams. Duplicate Legacy Mode – in this mode the device operates in a 40MHz channel composed of two adjacent 20MHz channel. The packets to be sent are in the legacy 11a format in each of the 20MHz channels. To reduce the PAPR the upper channel (higher frequency) is rotated by 90º relative to the lower channel. 40 MHz Upper Mode – used to transmit a legacy or HT packet in the 16 upper 20MHz channel of a 40MHz channel. 40 MHz Lower Mode – used to transmit a legacy or HT packet in the lower 20MHz channel of a 40MHz channelLM is mandatory and HT-Mode for 1 and 2 spatial streams are also mandatory. Legacy Support 802.11n PLCP Format http://www.enhancedwirelessconsortium.org/home/EWC_PHY_spec_V127.pdf
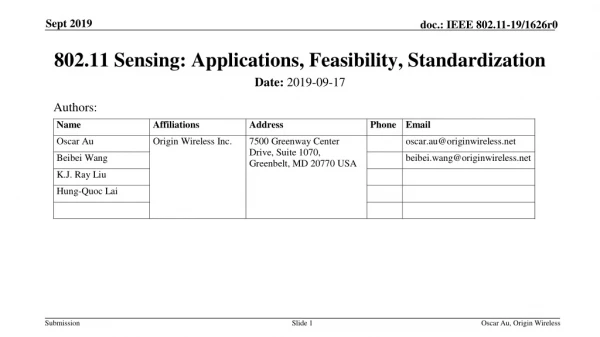
Some 802.11 performance results From IEEE 802.11-04/1369r0
Comparison with 802.11a/g Throughput Enhancements Peak Rates Relative Cost to Implement IEEE 802.11-04/1369r0
PHY Throughput • Link adaptation is based on long term average SNR sub-optimum inferior bound • Finer grid possible with more modes
Simulation results • Diversity gain for 2 streams, but not for 3 streams • 120 Mbps lowers SNR ~ 36dB 26dB doc.: IEEE 802.11-04/1369r0
Capacity usage at MAC-SAP vs. Number of VoIP sessions 1 TCP data flow transmitted using MIMO 3x3_64QAM2/3 (Ns=3) [144Mbit/s] VoIP: 120-byte packets emitted every 10 ms (2x96kbit/s) n VoIP sessions, using either 2x2_64QAM2/3 (Ns=1) [48Mbit/s] or 2x2_16QAM1/2 (Ns=1) [24 Mbit/s] MAC Efficiency between 78% and 55% 30 VoIP sessions + at least 65 Mbit/s of TCP traffic Mixed traffic handling doc.: IEEE 802.11-04/1369r0
IEEE TGn Usage models : Scenario I (Home) Traffic classification based on priority level (VoIP > TCP) Delay comparison for different error rate [cdf(d>D)] Strong QoS constraints of VoIP reached: with a simple centralised scheduling an efficient ARQ Max delay below 20 ms for QoS traffic Delay performances doc.: IEEE 802.11-04/1369r0
802.11n Certification Key Certification Features • Wi-Fi Alliance • Certifying to Draft 2.0 while draft is approved • Certify to Ratified Standard when available • 22 August 2007 - Almost 70 products certified for compliance with Draft 2.0 of the 802.11n • http://www.wi-fiplanet.com/news/article.php/3578886 Wi-Fi CERTIFIED™ 802.11n draft 2.0: Longer-Range, Faster-Throughput, Multimedia-Grade Wi-Fi® Networks
Pre-802.11n deployments • Belkin (pre-802.11n) • 8x coverage, 6x speed of 802.11g • 3 antennas • Netgear (pre-802.11n) • 7 antennas • 43.2 Mbps (measured) http://www.theregister.co.uk/2005/06/07/review_netgear_mimo_router/page2.html • Linksys (Cisco) • 802.11g with Speed and Range eXpansion (802.11g SRX) • 8x speed, 3 times range • 3 antennas • Airgo (chip vendor, “True MIMO”) • SOHOware, Planex • Linksys • Dell • Optional Pre-N with Broadcom adapter • http://biz.yahoo.com/prnews/060717/nym115.html?.v=38
802.11n Summary • By adding antenna arrays to WiFi, significant improvements possible without exponential increases in complexity • Most people using it for range extension • Thin pipe into the house • High SNRs needed for peak rates • Designed to co-exist with 802.11 a/b/g • WiFi Alliance certifying to draft 2.0 now
“Dedicated Short Range Communications” (DSRC) Started in IEEE 1609, spun into 802.11p Aka (WAVE) Wireless Access for Vehicular Environment Goal Telematics (collision avoidance a big driver) Roadside-to-vehicle Vehicle-to-vehicle environments 54 Mbps, <50 ms latency Possible competitor to cellular Operates in 5.850 to 5.925GHz band Draft under ballot Projected for March 2009 802.11p
Broader Context • 802.11p part of several standards which will jointly enable widescale telematics Intelligent Transportation Systems S. Biswas, R. Tatchikou, F. Dion, “Vehicle-to-vehicle wireless communication protocols for enhancing highway traffic safety,” IEEE Comm Mag, Jan 06, pp. 74-82. doc.: IEEE 802.11-07/2045r0
802.11p Applications • Applications • Emergency warning system for vehicles • Cooperative Adaptive Cruise Control • Cooperative Forward Collision Warning • Intersection collision avoidance • Approaching emergency vehicle warning (Blue Waves) • Vehicle safety inspection • Transit or emergency vehicle signal priority • Electronic parking payments • Commercial vehicle clearance and safety inspections • In-vehicle signing • Rollover warning • Probe data collection • Highway-rail intersection warning
In-Vehicle Displays and Annunciations COLLISION COLLISION IMMINENT IMMINENT FRONT LEFT ~ ~ Note 1: The OBU in the vehicle recognizing the threat transmits a WARNING and COLLISION PREPARATION MESSAGE with the location address of the threat vehicle. ~ ~ Note 2: Only the OBU in the threatening vehicle processes the message because only it matches the threat address. up to 100 m (328 ft) ~ ~ Note 3: COLLISION PREPARATION includes seat belt tightening, side air bag deployment, side bumper expansion, etc. Car NOT Stopping Radar Threat Identification Traffic Signal Traffic Signal OBUs on Control Ch Example Application From: IEEE 802.11- 04/ 0121r0 Available:http://www.npstc.org/meetings/Cash%20WAVE%20Information%20for%205.9%20GHz%20061404.pdf
Operation • Spectrum divided into 7 bands • 178 is control (safety) • 2 edge channels are reserved for future • The rest are service channels (not application specific) • IEEE 802.11a adjusted for low overhead operations D. Jiang, V. Taliwal, A. Meier, W. Holfelder, R. Herrtwich, “Design of 5.9 ghz dsrc-based vehicular safety communication,“ IEEE Wireless Comm, Oct 06, pp. 36-43
Control Messaging characteristics Most messages are single hop Some broadcasting (e.g., forwarding hazard warnings) No coordination for channel access Messages targeted based on vehicle location more so than vehicle identity Short and mapped to a single frame Arbitrary distances (100m is a more practical distance) Vehicles in constant communication Dedicated channel Messaging Principles Safety communication is not application-to-application Instead, an intermediate layer is responsible for safety information distribution and aggregation among vehicles and infrastructure. Applications work by continuously analyzing the aggregated information to look out for potential trigger conditions. Simply put, the sender of a safety message cannot dictate how the message should be processed “I-am-braking” vs “You have-to-brake” message. One particular advantage Simplifies future enhancements Safety Messages
Reliability • If cars are being controlled wirelessly, dropping packets could cause accidents • May need to signal a long ways off • Result of studies: • Errors not bursty • Communications up to 1 km feasible Free way conditions F. Bai, H. Krishnan, “Reliability Analysis of DSRC Wireless Communication for Vehicle Safety Applications,” IEEE ITSC 2006 Packet error distribution
Possible Deployments • Good (though dated) schedule at http://www.itsforum.gr.jp/Public/E4Meetings/P03/schnackeTP74.pdf • US DoT planning to deploy as Vehicle Infrastructure Integration project (VII) • http://www.networkworld.com/news/2005/111405-vii.html • Widescale deployment decision in 2008 • First use in intersections • GM possibly going its own route with “Vehicle to Vehicle” which leverages OnStar • http://www.gm.com/company/gmability/safety/news_issues/releases/sixthsense_102405.html • European Effort – Car-to-Car Communication Consortium • http://www.car-to-car.org/
802.11r Support for Faster Roaming
Fast BSS Roaming/Transition within IEEE WLAN networks Preserve security with handovers <50ms Fast BSS Roaming is possible only within a certain area called the mobility domain (MD), inter-MD cases are not covered Mobility Domain (MD): Set of BSS grouped together with the same 48bit MD Identifier FT functionality seeks to provide handover performance for RT services Key Issues Resource Reservations Security Collapsed 5 step process down to 3 Scanning – active or passive for other APs in the area Authentication with a (one or more) target AP Re-association to establish connection at target AP Target 2008 802.11r overview http://www.cs.tut.fi/kurssit/TLT-6556/Slides/Lecture4.pdf
Resource Reservation (optional) • Resource Reservation (RR) is to setup QoS resources in one or more target AP during FT transition mechanism • RR Setup only follows successful PTK derivation • RR is based on one round-trip negotiation • – STA requests certain QoS and t-AP provides as much or less QoS • • Benefits • No delay during re-association for RR (RIC) processing • Better application service quality during FT roaming • Without RR, STA may realize target AP does not have enough resources at the time of reassociation • Drawbacks • STA may reserve at multiple AP but use only one => cost • Increased AP complexity • –Mechanism • AP advertises the capability in the Beacon frame • STA has the choice to initiate the RR procedure
Security • New key hierarchy • New authentication route http://www.cs.tut.fi/kurssit/TLT-6556/Slides/Lecture4.pdf http://www.networkcomputing.com/gallery/2007/0416/0416ttb.jhtml;jsessionid=0CK4ZKR20HC5QQSNDLPCKHSCJUNN2JVN
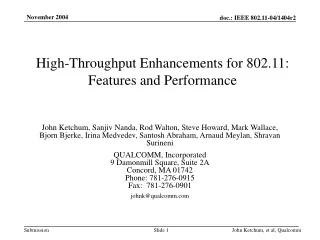
Reduction in Roaming Time S. Bangolae, C. Bell, E.Qi, “Performance study of fast BSS transition using IEEE 802.11r,” International Conference On Communications And Mobile Computing, 2006
802.11s Mesh Networking in WiFi
Objectives1 • Modify 802.11 MAC to create dynamic self-configuring network of access points (AP) called and Extended Service Set (ESS) Mesh • Automatic topology learning, dynamic path selection • Single administrator for 802.11i (authentication) • Support up to 32 AP • Support higher layer connections • Allow alternate path selection metrics • Extend network merely by introducing access point and configuring SSID IP or Ethernet 1. http://standards.ieee.org/board/nes/projects/802-11s.pdf
WLAN Mesh– An IEEE 802.11-based Wireless distribution service consisting of a set of two or more Mesh Points interconnected via IEEE 802.11 links and communicating via the WLAN Mesh Services. Mesh Point - A Mesh Services supporting device (bridge, access point) Mesh AP - Any Mesh Point that is also an Access Point. Mesh Portal - A boundary connection for the Mesh Conceptual Operation of 802.11s http://ieee802.org/802_tutorials/nov06/802.11s_Tutorial_r5.pdf
WiMesh http://www.wi-mesh.org/ Major Partners Nortel InterDigital Phillips Mitre Naval Research Lab Thomson SEEMesh Simple, Efficient and Extensible Mesh No group site Major Partners Intel Motorola (purchased MeshNetworks) Nokia Texas Instruments Major Participants 1. http://grouper.ieee.org/groups/802/11/Reports/tgs_update.htm
Key Technologies • Topology Formation • Internetworking • Routing • Security
Topology Formation • Each Mesh Point may have one or more logical radio interface: • Each logical interface on one (infrequently changing) RF channel, belong to one “Unified Channel Graph” • Each Unified Channel Graph shares a channel precedence value • Channel precedence indicator – used to coalesce disjoint graphs and support channel switching for DFS http://ieee802.org/802_tutorials/nov06/802.11s_Tutorial_r5.pdf
Internetworking • 1. Determine if the destination is inside or outside of the Mesh • Leverage layer-2 mesh path discovery • 2. For a destination inside the Mesh, • a. Use layer-2 mesh path discovery/forwarding • 3. For a destination outside the Mesh, • a. Identify the “right” portal, and deliver packets via unicast • b. If not known, deliver to all mesh portals http://ieee802.org/802_tutorials/nov06/802.11s_Tutorial_r5.pdf
Default Routing: Hybrid Wireless Mesh Protocol (HWMP) • On demand routing is based on Radio Metric AODV (RM-AODV) • Based on basic mandatory features of AODV (RFC 3561) • Extensions to identify best-metric path with arbitrary path metrics • Destinations may be discovered in the mesh on-demand • Pro-active routing is based on tree based routing • If a Root portal is present, a distance vector routing tree is built and maintained • Tree based routing is efficient for hierarchical networks • Tree based routing avoids unnecessary discovery flooding during discovery and recovery http://ieee802.org/802_tutorials/nov06/802.11s_Tutorial_r5.pdf
RA-OLSR – Key Features (Optional Routing) • Multi Point Relays (MPRs) • – A set of 1-hop neighbor nodes covering 2-hop neighborhood • – Only MPRs emit topology information and retransmit packets • • Reduces retransmission overhead in flooding process in space. • (Optional) message exchange frequency control (fish-eye state routing) • – Lower frequency for nodes within larger scope • Reduce message exchange overhead in time. http://ieee802.org/802_tutorials/nov06/802.11s_Tutorial_r5.pdf
Security • The MPs are no longer wired to one another • There is no intrinsic node hierarchy • MPs need to maintain secure links with many other MPs • Transport security • Mutually authenticate neighbor MPs • Generate and manage session keys and broadcast keys • Data confidentiality over a link • Detect message forgeries and replays received on a link • Authentication and Initial Key Management • Basic approach is to re-use 802.11i/802.1X • Re-use of 802.11i facilitates implementation http://ieee802.org/802_tutorials/nov06/802.11s_Tutorial_r5.pdf
Usage Models http://ieee802.org/802_tutorials/nov06/802.11s_Tutorial_r5.pdf
Combat Usage Case • Vehicular mounted APs interconnected via WDS (wide area data services) • Dismounted troops carry client STAs • APs & client STAs are communication endpoints • Occasionally a STA may need to switch roles and become an AP in order to heal a bifurcated mesh • Predominance of multicast applications, e.g., situational awareness, conference mode VoIP, … • Type 1 encryption, e.g., Harris SecNet 11 • Auto configuration • plug and play, or nearly so • Multiple 802.11 ESS Meshes interconnected via JTRS ELOS links • Some JTRS ELOS links may belong to the WDS while others are external to the WDS, i.e., are terminated via IP routers rather than by 802.11 APs. Logical View Mesh AP Links 802.11 MAC/PHY (4-addr data frames) 802.11 ESS Mesh Client-to-AP Links 802.11 MAC/PHY (3-addr data frames) JTRS ELOS Links (Joint Tactical Radio System) (Extended Line-of-Site) Slide from: J. Hauser, D. Shyy, M. Green, MCTSSA802.11sMilitary Usage Case Picture from: IEEE 802.11-04/1006r0
WiFi Mesh Products • Motorola Mesh Networks • www.motorola.com/mesh • Tropos • www.tropos.com • PacketHop Communications • www.packethop.com • MeshDynamics • www.meshdynamics.com • SkyPilot Networks • www.skypiilot.com • Proxim Networks • www.proxim.com/can/ • Nortel Networks • Wave Wireless • www.wavewireless.com • LocustWorld.com • FireTide Network List from: http://www.cs.wustl.edu/~jain/cse574-06/ftp/j_jmesh/sld019.htm
802.11y Dynamic Spectrum Access
Background • FCC issued rules for novel “lite licensing” scheme for 3650-3700 MHz band • Licensees • pay small fee for nation-wide non-exclusive license • Pay additional fee for each high-powered base station (up to 20 W) • No need for license for clients nor operators, but devices must be “enabled” • Devices must be identifiable (to find the culprit) • Support contention based protocol to give opportunity to transmit to multiple licensees • Interference disputes between licensees must be resolved between themselves • Applications • Back haul for Municipal Wi-Fi networks • Industrial automation and controls • Campus and enterprise networking • Last Mile Wireless Broadband Access • Fixed Point to point links • Fixed point to mobile links • Public safety and security networks
Ports 802.11a to 3.65 GHz – 3.7 GHz (US Only) FCC opened up band in July 2005 Conditionally approved Summer 2007, to sponsor ballot, ready 2008 Intended to provide rural broadband access (distances up to 5 km) Incumbents Band previously reserved for fixed satellite service (FSS) and radar installations – including offshore Must protect 3650 MHz (radar) Not permitted within 80km of inband government radar Specialized requirements near Mexico/Canada and other incumbent users Leverages other amendments Adds 5,10 MHz channelization (802.11j) DFS for signaling for radar avoidance (802.11h) Database of existing devices Access nodes register at http://wireless.fcc.gov/uls Must check for existing devices at same site 802.11y Source: IEEE 802.11-06/0YYYr0
Key 802.11y technologies • DFS (802.11h) • Channelization (802.11j) • Contention based protocol (CBP) • geographic protection of the grandfathered satellite stations • database for users to research other users in their area • Location information • Extended channel switch announcement (ECSA) • Dependent notification of DFS • Continuous adaptation • Dependant station enablement (DSE)
Dependant station enablement DSE Enabling Process • DSE controls when a dependant is allowed to transmit in licensed spectrum • enabling station need not be an access point, may be elsewhere • Need not be completed via a direct link https://edge.arubanetworks.com/article/standards-corner-august-2007-ieee-802-11y-3650-3700-mhz-operation-usa
Summary • 802.11 is expanding into lots of applications • VOIP roaming (802.11r) • Cellular like ranges with dynamic spectrum access (802.11y) • Telematics (802.11p) • Mesh networks (802.11s) • Leverage and enhance previous amendments • Expect to see cross-pollination of technologies later.