Understanding HIPAA: Privacy and Security Rules for Protecting Health Information
The Health Insurance Portability and Accountability Act (HIPAA) mandates changes in the legal framework for health benefits and protects the privacy of patients' health information (PHI). This overview focuses on the Privacy and Security Rules, which require covered entities to safeguard PHI, provide patients with rights to access their medical records, and ensure compliance through corrective action in case of incidents. Standards for electronic data interchange and national provider identification are also covered, emphasizing the importance of protecting sensitive health information.

Understanding HIPAA: Privacy and Security Rules for Protecting Health Information
E N D
Presentation Transcript
HIPAA HEALTH INSURANCE PORTABILITY ACOUNTABILITY ACT
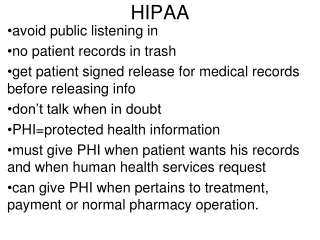
(HIPAA) mandated significant changes in the legal and regulatory environment governing the provision of health benefits, the delivery of and payment for healthcare services, and the security and privacy of individually identifiable, protected health information (PHI) in written, electronic or oral formats. • HIPAA also provides standards for Electronic Date Interchange (EDI) and National Provider Identification (NPI) numbers. This overview covers only the Privacy and Security Rules of HIPAA.
Privacy and Security incident If there is a, the law and federal regulators could require KP to implement corrective action plans that would include the following: • Notification of the federal government if there is an incident involving Medicare member/patients; • Notification of individual member/patients whose PHI was illegally accessed, used or disclosed; and • The individual workforce member(s) responsible for the incident may be subject to corrective action, up to and including termination.
Privacy Rule This rule provides for the privacy of PHI that is received, accessed, used, created or disclosed by a covered entity. HIPAA creates standards that require hospital to protect the privacy of a member/patient’s medical records, health plan payment and claims information and other confidential information. • The Privacy Rule also provides patients with specific rights related to their medical records. • The Privacy Rule also provides member/patients with specific rights related to their medical records. For example, a member/patient has the right to request: • access to and copies of his/her medical record; • an amendment to the medical record; • an accounting of disclosures of PHI; • a limit on information about her/himself that is provided in a hospital directory.
Security Rule • Administrative safeguards – examples: training the entire workforce on security and developing and implementing security policies and procedures • Physical safeguards – examples: making sure computer terminals that may have confidential information are positioned to minimize viewing of the information and not propping open a door that should be locked • Technical safeguards – examples: following good password policies and logging off your computer when stepping away
Pope John XXIII Consult not your fears, but your hopes and dreams.Think not about your frustrations,But about your unfulfilled potential.Concern yourself not with what you tried and failed in, but with what is possible for you to do.
Thank you . . . The Lord bless you and keep you! The Lord let His Face shine upon you, The Lord be Gracious to you! The Lord look upon you kindly and give you PEACE! Numbers 6:24-26