Using Cryptography
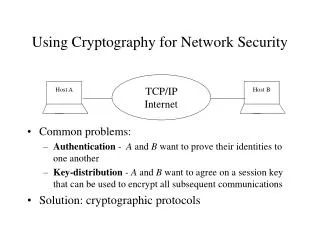
This comprehensive guide delves into key cryptographic concepts, including symmetric ciphers, hash functions, and digital signatures. Learn about block and stream ciphers, exploring modes like ECB and CBC, and uncover their benefits and weaknesses. Understand the purpose of cryptographic hash functions, their properties, and collision resistance. Explore digital signatures and how public key cryptography ensures message authenticity. By the end, you'll grasp critical principles of cryptographic protocols, paving the way for secure communications in various applications.

Using Cryptography
E N D
Presentation Transcript
Using Cryptography More on Symmetric Ciphers, Signatures, Hash functions, and Certificates
More on Symmetric Ciphers Block Cipher Modes and Stream Ciphers
Using a Block Cipher • ECB Mode • Problem? P1 P2 … AES AES Key Key C1 C2
Using a Block Cipher • CBC Mode • What is the benefit? P1 P2 IV C1 … AES AES Key Key C1 C2
How bad is ECB? • An image representation
Stream Ciphers • OTP • Good, but impractical • Can encrypt one letter at a time • A computerized approximation 10100101010010101001101001… PT CT
Randomness • Algorithm • Not random (by definition!) • [example] • Something better • RC4 • Key used to “seed” • Better randomness properties
Signatures • Suppose … • Alice could encrypt with her private key • And Bob could decrypt it with her public key • Why? • Sign (given private key) S = EKRa(M) • Verify (given public key) M = EKUa(S)
More for your Metaphor • A special lockbox KRa KUa
Test Protocols • What security properties do you get? 1. A to B: E[KRB,M] 2. B to A: E[KRB,Ks], E[Ks,M] 3. A to B: E[KUB,E[KRA,M]] 4. B to A: E[KRB,Ks||E[Ks,M]] 5. A to B: E[KRA,M]
Hash Functions • Purpose • pack data into a fixed size container • Random-looking • Reproducible • Does NOT provide integrity • Benefits • Fixed size • typically smaller than the data • Can keep data in clear text
0 0 1 Example • A simple hash • Bitwise XOR of all blocks
A More Complex Hash • Using a block cipher • Use known IV for the key (e.g. all 0’s) • XOR all ciphertexts together • CBC Mode • Take the last ciphertext P1 P2 0 C1 … AES AES Key Key C1 C2
What is a Hash Function? • Basic Requirements: • take input of any size • produce a fixed-length output • easy to compute • Collision Resistance • given x, hard to find y s.t. H(y) = H(x)
Signatures • PKC is expensive • Sign a large message M • Sign the hash • Verify by doing what? • Nobody can modify M • Unless …
Collision (non-)Resistance Alice sends this message M: To LocalBank: I have enclosed $10,000 to be deposited in my beloved son Anthony’s money market account (#12345) so that I may help him pay for graduate school. • -Alice She signs a 16-bit hash h = H(M) and sends this signature
An Evilsmith Production To LocalBank: I have enclosed a check for $10,000 to be deposited in my beloved friend Mallory Evilsmith’s money market account (#98765) so that I may help him pay for graduate school. He’s such a hard-working, honest student, and he always follows the code of conduct for his classes in information security. • -Alice
Many Equivalent Letters { - || To} LocalBank { - || , Inc.} : I {have enclosed || am including} { - || a check for} {$10,000 || ten thousand dollars} to {be deposited || deposit} in my {beloved || favorite} {friend || pal} {- || Mr.} {Mallory || M.} Evilsmith’s money market account {(#98765) || (no. 98765)} so that I {may || can} help him {pay for || afford} {attending || - } graduate school { - || at UTA}. {He’s || he is} such a {hard-working || diligent}, {honest || responsible} {student || person}, and he always follows the code of conduct for his {classes || courses} in {computer || information} security. • - Alice • 221 possibilities
Collision Non-Resistance • Alternately • “space-space-backspace” • Replace some with “space-backspace-space” • Images • Small low-order bit changes in a bitmap • Re-compress into JPEG • Cost to the attacker • How much?
MAC • “Keyed hash” • Provides authentication and integrity • MAC algorithms • CBC-MAC (Uses key in the hashing) • HMAC (Hash with a secret)
Fix These Protocols • Authentication For 2. and 3. Assume both know Ks • Conf. and Auth. 1. A to B: M|E[KUB,H(M)] 2. B to A: H(Ks),M 3. A to B: E[Ks,H(M)] 4. B to A: E[KUA,Ks|E[KRB,H(M)]], E[Ks,M]
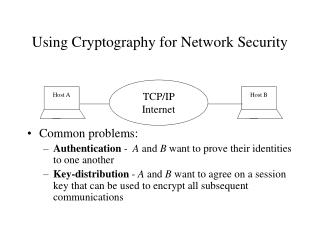
Public Keys for All! • Why not always use PKC? • Slow • About 10K times slower than symmetric • Large • 1024-bit+ keys • Block size = key size
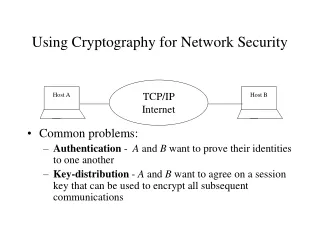
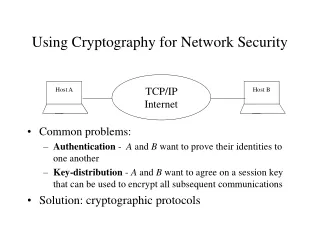
Using Public Keys • New York Times • expensive • out-of-band broadcast is difficult • hard to validate • Email • Easy to spoof • No standard way to check
Certificates • CA • Signs a hash of the certificate • Collision resistance is critical! • Users • Can see certificate (in plaintext) • Verify signature on the hash • Verify once, then store
Certificates • Simple Certificates • Set of info • ID (“Alice”, etc.) • Public Key (KUa) • Timestamp • Linked together • Authenticated • Ca = EKRt[IDa, KUa, Time1]
Requirements • Certificate Authority • Known and trusted • Public key known by all • Individuals • In person or • Other secure communication
Using Certificates • User may distribute • Anyone can check the authorities’ signature • Anyone can read the information • Can still use a DB • DB can verify the signature before insertion
Certificates and the Web • SSL/TLS • X.509 Certificates • Major CAs • How many do you trust? • The little lock • Just some certificate • Signed by a CA in the list • That CA matched the cert. name to the owner (hopefully)
CAs that I trust • A sampling • Autoridad de Certificacion Firmaprofesional • ABA.ECOM, Inc. • AC Camerfirma SA CIF A82743287 • AOL Time Warner • AddTrust AB • America Online, Inc. • 42 more …