Point-to-Point Protocol (PPP)
Explore the features, components, and operations of PPP for router-to-router and host-to-network connections. Learn about Transmission Synchronization, PPP Layer Functions, and PPP Authentication methods like PAP and CHAP.

Point-to-Point Protocol (PPP)
E N D
Presentation Transcript
PPP Overview • Link Control Protocol (LCP) • Network Control Program (NCP) • Configure and verify the configuration of PPP • PPP authentication
PPP OverviewPPP provides router-to-router and host-to-network connections over both synchronous and asynchronous circuits
Transmission Synchronization • Asynchronous Transmission: • Transmitting & Receiving devices maintain their own internal clocks. They do not synchronize their clocks. • Each frame is sent separately. • Each frame begins with a start bit & ends with a stop bit. A extra bit called parity bit maybe added for error detection • Synchronous Transmission: • Transmitting device provides clocking • May use separate channel that is dedicated to the clock • Resists timing errors better than Asynchronous because the transmitter & receiver use the same clock • Can transmit large blocks of data
PPP Features • Control of data link setup • Provides for dynamic assignment of IP addresses • Network protocol multiplexing • Link configuration and link quality testing • Error detection • Negotiation options for capabilities such as network-layer address negotiation and data compression negotiations
PPP Layer Function In order to move data between any two nodes or routers, a data path must be established, and flow control procedures must be in place to ensure delivery of data. This is also true in the WAN environment and is accomplished by using WAN protocols such as Point-to-Point Protocol
PPP Components 1. Encapsulating datagrams over serial links. (Point-to-point links) 2. A Link Control Protocol (LCP) for establishing, configuring, and testing the data-link connection. 3. A family of Network Control Protocols (NCPs) for establishing and configuring different network-layer protocols. (TCP/IP, IPX AND APPLETALK
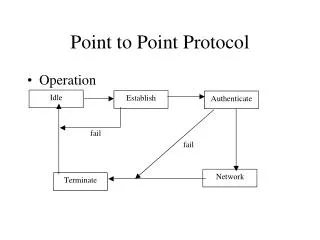
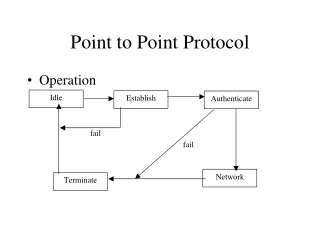
PPPGeneral Operations Establishing communications over a point-to-point link: 1.The originating PPP first sends LCP frames to configure and (optionally) test the data-link.
PPPGeneral Operations 2. After the link has been established and optional facilities have been negotiated as needed by the LCP, the originating PPP sends NCP frames to choose and configure one or more network-layer protocols. When each of the chosen network-layer protocols has been configured, packets from each network-layer protocol can be sent over the link
PPPGeneral Operations 3. The link will remain configured for communications until explicit LCP or NCP frames close the link, or until some external event occurs (for example, an inactivity timer expires or a user intervenes).
PPPLink Control Protocol 1. First, link establishment and configuration negotiation occurs. This is done before any network-layer datagrams can be exchanged. 2. Second, LCP allows an optional link-quality determination phase following the link-establishment and configuration-negotiation phase. In this phase, the link is tested to determine whether the link quality is sufficient to bring up network-layer protocols. (This phase is optional)
PPPLink Control Protocol 3. Third, Network-layer protocols can be configured separately by the appropriate NCP. 4. Finally, link termination occurs. LCP can terminate the link at any time. This usually will be done at the request of a user but can happen because of a physical event, such as the loss of carrier or the expiration of an idle-period timer.
PPP Authentication Authentication phase of a PPP session is optional After the link has been established, and the authentication protocol chosen, the peer can be authenticated. If it is used, authentication takes place before the network-layer protocol configuration phase begins • Password Authentication Protocol (PAP) • Challenge Handshake Authentication Protocol (CHAP)
PPP Authentication • Password Authentication Protocol (PAP) PAP is not a strong authentication protocol. Passwords are sent across the link in clear text. Also known as 2-way handshake
PPP Authentication • Challenge Handshake Authentication Protocol (CHAP) • CHAP is used to periodically verify the identity of the remote node, using a three-way handshake • CHAP provides protection against playback attacks through the use of a variable challenge value that is unique and unpredictable • CHAP does not allow a caller to attempt authentication without a challenge