Slammer Worm
Slammer Worm. By : Varsha Gupta.P 08QR1A1216. What is slammer worm?. The slammer worm is a computer virus that caused a denial of service on some Internet hosts and dramatically slowed down general Internet traffic. Why Slammer Was So Fast?. Bandwidth constraint vs. delay constraint


Slammer Worm
E N D
Presentation Transcript
Slammer Worm By : Varsha Gupta.P 08QR1A1216
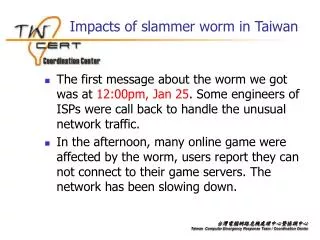
What is slammer worm? • The slammer worm is a computer virus that caused a denial of service on some Internet hosts and dramatically slowed down general Internet traffic.
Why Slammer Was So Fast? • Bandwidth constraint vs. delay constraint • Slammer 404 bytes (376 payload) UDP based-- bandwidth constraint • Code Red 4K bytes TCP based – delay constraint • UDP vs. TCP
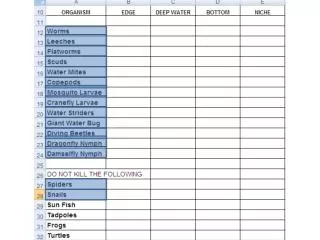
How the Slammer Worm Spreads? • Slammer targets computers running Microsoft SQL Server 2000, and computers running Microsoft Desktop Engine (MSDE) 2000. • The worm sends 376 bytes to UDP port 1434, the SQL Server Resolution Service Port.
Overview • Slammer worm is also known as : • -SQLSlammer,Saphire, W32.SQLExp.Worm,Worm.SQL.Helkern, DDOS_SQLP1434.A. • Released: • -January25,2003,at about 5:30 a.m (GMT).
Overview • How ? -Exploit Buffer-overflow with MS SQL/MS SQL Server Desktop Engine (known vulnerability, July 2002). • Fastest worm in history. • Spread world-wide in under 10 minutes. • Doubled infections every 8.5 seconds. • 376 bytes long.
Overview • Platform : Microsoft SQL Server 2000 • Vulnerability: Buffer overflow. • Propagation : Single UDP packet. • Features: Memory resident , handcoded in assembly.
Worm History • What is worm? • Self-propagating malicious code. • History • Morris worm was one of the first worms distributed over Internet. • Timeline of notable worms. • http://en.wikipedia.org/wiki/Timeline_of_notable_computer_viruses_and_worms • Two examples , • Code Red – 2001, MS IIS. • Slammer – 2003, MS SQL.
Worm Composition • 376 bytes long • Less than 300 bytes of executable code • 404 byte UDP packets,including headers • Composed of 4 functional sections
Worm Functions • Reconstruction session from buffer overflow. • Obtains(and verifies!) windows API functions addresses. • Initializes pseudo-random number generator and socket structures. • Continuously generates random IP addresses and sends UDP data-grams of itself.
Affected Operating System: Since SQL server 2000 and MSDE 2000 can be installed on top of almost all the Microsoft Windows operating system, almost all Windows system,from windows 95 to Windows 2000 DataCenter, are affected.
Direct Damage • Infected between 75,000 and 1,60,000 systems. • Disabled SQl server databases on infected machines. • Saturated world networks with traffic. • Disrupted internet connectivity worldwide.
Effective damage • South korea was off-line • Disrupted financial institutions • Airline delays and cancellations • Affedted many U.S. government and commercial websites
Specific damage • 13,000 bank of America ATMs stopped working • Continental airlines flights were cancelled and delayed ; ticketing system was inundated with traffic .Airport self-check-in kiosks stopped working
Propagation technique • Single UDP packet. • Target port 1434(Microsoft-SQL-Monitor). • Causes buffer overflow. • Continuously sends itself via UDP packets to pseudo-random IP addresses , including broadcast and multicast addresses. • Does not check weather target machines exist.
Propagation Analysis • Rapid spread made timely defense impossible. • Rapid spread caused worm copies to compete. • Bandwidth limited ,not latency limited(doesn’t wait to establish connection). • Easy to stop at firewall.
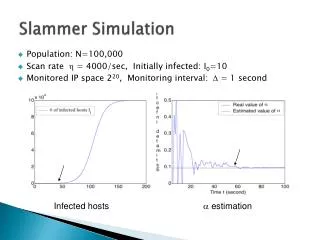
Propagation speed • infected more than 90 percent of vulnerable hosts within 10 minutes • Achieved more than 55 million scans per second • Doubled infections every 8.5 seconds • Teo orders of magnitude faster than code Red
Propagation Model • Random Scanning • Initially spread exponentially, slows as the worms retry infected or immune addresses • Probes of Slammer worm from Dshield data set • Initially matched random scanning worm • Soon slowed down due to bw saturation and network failures Probe rate of Code red worm (a typical random-scanning worm)
Possible Variations • Could have attacked HTTP or DNS servers. • Could have gone dormant. • Could have forged source port to DNS resolution.
RECOVERY • Disconnection from network. • Reboot the machine,or restart SQL server. • Block port 1434 at external firewall • Install patch.
Patching and Protecting Your Systems • Patch: • MS has released the patch before the worm attack happens • Protecting : • To protect your computers run SQL Server 2000 with the SQL Server 2000 Security Tools. • The SQL Server 2000 Security Tools are used to scan instances of SQL Server 2000 and detect security vulnerabilities, and then apply updates to the affected files.
What ISA Server Can Do To Help Stop Slammer? • Wecan take the following steps to configure ISA Server to help you protect your network against further infiltration by Slammer. • Note that the steps detailed below assume the following: • ISA Server is installed in Firewall or Integrated mode • ISA Server is the only route between the Internet and the internal network • IP Packet Filtering is enabled • No Server Publishing rule allows UDP-1434 to the internal network
To help prevent outbound attacks: Create a protocol definition Create a protocol rule
Create a protocol definition with the following parameters: • Set Name to SQL Enumeration • Set Protocol to UDP. • Set Direction to Send. • Set Local Port to Any. • Set Remote port to 1434
Create a protocol rule with the following parameters: • Set Action = Deny • Set Protocol to SQL Enumeration. • Set Schedule to Always. • Set Applies totoAll requests.
Reference • Worm • A Taxonomy of Computer Worms • en.wikipedia.org/wiki/Computer _ worm • Slammer Worm • http://www.microsoft.com/sql/prodinfo/previousversions/letter.mspx • http://www.cert.org/advisories/CA-2003-04.html • Inside the Slammer Worm, IEEE S&P 2003