CPS 214 Computer Networks and Distributed Systems
410 likes | 627 Vues
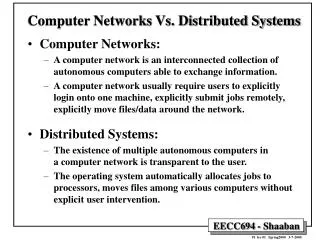
CPS 214 Computer Networks and Distributed Systems. Cryptography Basics RSA SSL SSH Kerberos. Plaintext. E key1 (M) = C. Encryption. Key 1. Cyphertext. Decryption. D key2 (C) = M. Key 2. Original Plaintext. Basic Definitions. Private Key or Symmetric : Key 1 = Key 2

CPS 214 Computer Networks and Distributed Systems
E N D
Presentation Transcript
CPS 214 Computer Networks and Distributed Systems Cryptography Basics RSA SSL SSH Kerberos 15-853
Plaintext Ekey1(M) = C Encryption Key1 Cyphertext Decryption Dkey2(C) = M Key2 Original Plaintext Basic Definitions • Private Key or Symmetric: Key1 = Key2 • Public Key or Asymmetric: Key1 Key2Key1 or Key2 is public depending on the protocol 15-853
What does it mean to be secure? • Unconditionally Secure: Encrypted message cannot be decoded without the key • Shannon showed in 1943 that key must be as long as the message to be unconditionally secure – this is based on information theory • A one time pad – xor a random key with a message (Used in 2nd world war) • Security based on computational cost: it is computationally “infeasible” to decode a message without the key. • No (probabilistic) polynomial time algorithm can decode the message. 15-853
Primitives: One-Way Functions • (Informally): A function • Y = f(x) • is one-way if it is easy to compute y from x but “hard” to compute x from y • Building block of most cryptographic protocols • And, the security of most protocols rely on their existence. • Unfortunately, not known to exist. This is true even if we assume P NP. 15-853
One-way functions: possible definition • F(x) is polynomial time • F-1(x) is NP-hard • What is wrong with this definition? 15-853
One-way functions:better definition • For most y no single PPT (probabilistic polynomial time) algorithm can compute x • Roughly: at most a fraction 1/|x|k instances x are easy for any k and as |x| -> • This definition can be used to make the probability of hitting an easy instance arbitrarily small. 15-853
Some examples (conjectures) • Factoring:x = (u,v)y = f(u,v) = u*v If u and v are prime it is hard to generate them from y. • Discrete Log:y = gx mod p where p is prime and g is a “generator” (i.e., g1, g2, g3, … generates all values < p). • DES with fixed message:y = DESx(m) This would assume a family of DES functions of increasing key size (for asymptotics) 15-853
One-way functions in private-key protocols • y = ciphertext m = plaintext k= key • Is • y = Ek(m) (i.e. f = Ek) • a one-way function with respect to y and m? • What do one-way functions have to do with private-key protocols? 15-853
One-way functions in private-key protocols • y = ciphertext m = plaintext k= key • How about • y = Ek(m) = E(k,m) = Em(k) (i.e. f = Em) • should this be a one-way function? • In a known-plaintext attack we know a (y,m) pair. • The m along with E defines f • Em(k) needs to be easy • Em-1(y) should be hard • Otherwise we could extract the key k. 15-853
One-way functions in public-key protocols • y = ciphertext m = plaintext k = public key • Consider: y = Ek(m) (i.e., f = Ek) • We know k and thus f • Ek(m) needs to be easy • Ek-1(y) should be hard • Otherwise we could decrypt y. • But what about the intended recipient, who should be able to decrypt y? 15-853
One-Way Trapdoor Functions • A one-way function with a “trapdoor” • The trapdoor is a key that makes it easy to invert the function y = f(x) • Example: RSA (conjecture) y = xe mod n Where n = pq (p, q are prime) p or q or d (where ed = 1 mod (p-1)(q-1)) can be used as trapdoors • In public-key algorithms f(x) = public key (e.g., e and n in RSA) Trapdoor = private key (e.g., d in RSA) 15-853
One-way Hash Functions • Y = h(x) where • y is a fixed length independent of the size of x. In general this means h is not invertible since it is many to one. • Calculating y from x is easy • Calculating any x such that y = h(x) give y is hard • Used in digital signatures and other protocols. 15-853
Protocols: Digital Signatures • Goals: • Convince recipient that message was actually sent by a trusted source • Do not allow repudiation, i.e., that’s not my signature. • Do not allow tampering with the message without invalidating the signature • Item 2 turns out to be really hard to do 15-853
Dk1(m) Alice Bob Using Public Keys K1 = Alice’s private key Bob decrypts it with her public key More Efficiently Dk1(h(m)) + m Alice Bob h(m) is a one-way hash of m 15-853
Key Exchange Private Key method Trent Eka(k) Ekb(k) Generates k Alice Bob Public Key method Ek1(k) Alice Bob Generates k k1 = Bob’s public key Or we can use a direct protocol, such as Diffie-Hellman (discussed later) 15-853
Plaintext Ek(M) = C Encryption Key1 Cyphertext Decryption Dk(C) = M Key1 Original Plaintext Private Key Algorithms What granularity of the message does Ek encrypt? 15-853
Private Key Algorithms • Block Ciphers: blocks of bits at a time • DES (Data Encryption Standard)Banks, linux passwords (almost), SSL, kerberos, … • Blowfish (SSL as option) • IDEA (used in PGP, SSL as option) • Rijndael (AES) – the new standard • Stream Ciphers: one bit (or a few bits) at a time • RC4 (SSL as option) • PKZip • Sober, Leviathan, Panama, … 15-853
Private Key: Block Ciphers • Encrypt one block at a time (e.g. 64 bits) • ci = f(k,mi) mi = f’(k,ci) • Keys and blocks are often about the same size. • Equal message blocks will encrypt to equal codeblocks • Why is this a problem? • Various ways to avoid this: • E.g. ci = f(k,ci-1 mi) “Cipher block chaining” (CBC) • Why could this still be a problem? Solution: attach random block to the front of the message 15-853
Iterated Block Ciphers m key • Consists of n rounds • R = the “round” function • si = state after round i • ki = the ith round key k1 R s1 k2 R s2 . . . . . . kn R c 15-853
Iterated Block Ciphers: Decryption m key • Run the rounds in reverse. • Requires that R has an inverse. k1 R-1 s1 k2 R-1 s2 . . . . . . kn R-1 c 15-853
Feistel Networks • If function is not invertible rounds can still be made invertible. Requires 2 rounds to mix all bits. high bits low bits R R-1 ki ki F F XOR XOR Forwards Backwards • Used by DES (the Data Encryption Standard) 15-853
Product Ciphers • Each round has two components: • Substitution on smaller blocksDecorrelate input and output: “confusion” • Permutation across the smaller blocksMix the bits: “diffusion” • Substitution-Permutation Product Cipher • Avalanche Effect: 1 bit of input should affect all output bits, ideally evenly, and for all settings of other in bits 15-853
Rijndael • Selected by AES (Advanced Encryption Standard, part of NIST) as the new private-key encryption standard. • Based on an open “competition”. • Competition started Sept. 1997. • Narrowed to 5 Sept. 1999 • MARS by IBM, RC6 by RSA, Twofish by Counterplane, Serpent, and Rijndael • Rijndael selected Oct. 2000. • Official Oct. 2001? (AES page on Rijndael) • Designed by Rijmen and Daemen (Dutch) 15-853
Public Key Cryptosystems • Introduced by Diffie and Hellman in 1976. Plaintext • Public Key systems • K1 = public key • K2 = private key Ek(M) = C Encryption K1 Cyphertext • Digital signatures • K1 = private key • K2 = public key Decryption Dk(C) = M K2 Original Plaintext Typically used as part of a more complicated protocol. 15-853
One-way trapdoor functions • Both Public-Key and Digital signatures make use of one-way trapdoor functions. • Public Key: • Encode: c = f(m) • Decode: m = f-1(c) using trapdoor • Digital Signatures: • Sign: c = f-1(m) using trapdoor • Verify: m = f(c) 15-853
Example of SSL (3.0) • SSL (Secure Socket Layer) is the standard for the web (https). • Protocol (somewhat simplified): Bob -> amazon.com • B->A: clienthello: protocol version, acceptable ciphers • A->B: serverhello: cipher, session ID, |amazon.com|verisign • B->A: key exchange, {masterkey}amazon’s public key • A->B: server finish: ([amazon,prev-messages,masterkey])key1 • B->A: client finish: ([bob,prev-messages,masterkey])key2 • A->B: server message: (message1,[message1])key1 • B->A: client message: (message2,[message2])key2 • |h|issuer = Certificate • = Issuer, <h,h’s public key, time stamp>issuer’s private key • <…>private key= Digital signature {…}public key= Public-key encryption • [..] = Secure Hash (…)key = Private-key encryption • key1 and key2 are derived frommasterkeyand session ID hand-shake data 15-853
Diffie-Hellman Key Exchange • A group (G,*) and a primitive element (generator) g is made public. • Alice picks a, and sends ga to Bob • Bob picks b and sends gb to Alice • The shared key is gab • Note this is easy for Alice or Bob to compute, but assuming discrete logs are hard is hard for anyone else to compute. • Can someone see a problem with this protocol? 15-853
ga gc Alice Mallory Bob gd gb Key1 = gad Key1 = gcb Person-in-the-middle attack Mallory gets to listen to everything. 15-853
RSA • Invented by Rivest, Shamir and Adleman in 1978 • Based on difficulty of factoring. • Used to hide the size of a group Zn* since: • . • Factoring has not been reduced to RSA • an algorithm that generates m from c does not give an efficient algorithm for factoring • On the other hand, factoring has been reduced to finding the private-key. • there is an efficient algorithm for factoring given one that can find the private key. 15-853
RSA Public-key Cryptosystem • What we need: • p and q, primes of approximately the same size • n = pq(n) = (p-1)(q-1) • e Z (n)* • d = inv. of e in Z (n)* i.e., d = e-1 mod (n) Public Key: (e,n) Private Key: d Encode: m Zn E(m) = me mod n Decode: D(c) = cd mod n 15-853
RSA continued • Why it works: • D(c) = cd mod n • = med mod n • = m1 + k(p-1)(q-1) mod n • = m1 + k (n) mod n • = m(m (n))k mod n • = m (because (n) = 0 mod (n)) • Why is this argument not quite sound? What if m Zn* then m(n) 1 mod n Answer 1: Not hard to show that it still works. Answer 2: jackpot – you’ve factored n 15-853
RSA computations • To generate the keys, we need to • Find two primes p and q. Generate candidates and use primality testing to filter them. • Find e-1 mod (p-1)(q-1). Use Euclid’s algorithm. Takes time log2(n) • To encode and decode • Take me or cd. Use the power method.Takes time log(e) log2(n) and log(d) log2(n) . • In practice e is selected to be small so that encoding is fast. 15-853
Security of RSA • Warning: • Do not use this or any other algorithm naively! • Possible security holes: • Need to use “safe” primes p and q. In particular p-1 and q-1 should have large prime factors. • p and q should not have the same number of digits. Can use a middle attack starting at sqrt(n). • e cannot be too small • Don’t use same n for different e’s. • You should always “pad” 15-853
RSA Performance • Performance: (600Mhz PIII) (from: ssh toolkit): 15-853
RSA in the “Real World” • Part of many standards: PKCS, ITU X.509, ANSI X9.31, IEEE P1363 • Used by: SSL, PEM, PGP, Entrust, … • The standards specify many details on the implementation, e.g. • e should be selected to be small, but not too small • “multi prime” versions make use of n = pqr…this makes it cheaper to decode especially in parallel (uses Chinese remainder theorem). 15-853
Factoring in the Real World • Quadratic Sieve (QS): • Used in 1994 to factor a 129 digit (428-bit) number. 1600 Machines, 8 months. • Number field Sieve (NFS): • Used in 1999 to factor 155 digit (512-bit) number. 35 CPU years. At least 4x faster than QS • Used in 2003-2005 to factor 200 digits (663 bits) 75 CPU years ($20K prize) 15-853
SSH v2 • Server has a permanent “host” public-private key pair (RSA or DSA) . Client warns if public host key changes. • Diffie-Hellman used to exchange session key. • Server selects g and p and sends to client. • Client and server create DH private keys. Client sends public DH key. • Server sends public DH key and signs hash of DH shared secret and other 12 other values with its private “host” key. • Symmetric encryption using 3DES, Blowfish, AES, or Arcfour begins. • User can authenticate by sending password or using public-private key pair. • If using keys, server sends “challenge” signed with users public key for user to decode with private key. 15-853
Kerberos • A key-serving system based on Private-Keys (DES). • Assumptions • Built on top of TCP/IP networks • Many “clients” (typically users, but perhaps software) • Many “servers” (e.g. file servers, compute servers, print servers, …) • User machines and servers are potentially insecure without compromising the whole system • A kerberos server must be secure. 15-853
Kerberos (kinit) Kerberos Authentication Server • Request ticket-granting-ticket (TGT) • <TGT> • Request server-ticket (ST) • <ST> • Request service Ticket Granting Server (TGS) 2 1 3 4 Service Server Client 5 15-853
Kerberos V Message Formats • C = client S = server K = key or session key • T = timestamp V = time range • TGS = Ticket Granting Service A = Net Address Ticket Granting Ticket: TC,TGS = TGS,{C,A,V,KC,TGS}KTGS Server Ticket: TC,S = S, {C,A,V,KC,S}KS Authenticator: AC,S = {C,T}KC,S • Client to Kerberos: C,TGS • Kerberos to Client: {KC,TGS}KC,TC,TGS • Client to TGS: {TC,TGS , S},AC,TGS • TGS to Client: {KC,S}KC,TGS, TC,S • Client to Server: AC,S, TC,S Possibly repeat 15-853
Kerberos Notes • All machines have to have synchronized clocks • Must not be able to reuse authenticators • Servers should store all previous and valid tickets • Help prevent replays • Client keys are typically a one-way hash of the password. Clients do not keep these keys. • Kerberos 5 uses CBC mode for encryption Kerberos 4 was insecure because it used a nonstandard mode. 15-853