VMWare patent
This document explores VMM challenges related to segmentation, memory tracing, and address space management in virtual machines. It discusses how VMWare utilizes techniques like shadow descriptor tables for protection, binary translation for emulation, and memory tracing to manage hardware interactions efficiently. The text also delves into the complexities of privileged and unprivileged instructions, the significance of the GDTR, and the implications of cached segment descriptors. It emphasizes the need for correct execution while maintaining performance and provides insights into the relationship between the guest OS, VMM, and memory protection.


VMWare patent
E N D
Presentation Transcript
VMWare patent 1/25/2007
Segmentation • First level translation • 6 segment desc in CPU • Tables in mem • Desc regs. cache Selector Offset Base + Limit … Log. addr
Segmentation • Why are there descriptors in mem and CPU? • Loading GDTR is PRIVILEGED • Loaded using UNPRIVILEGED inst. • VMM can control the GDT, software selects which entries
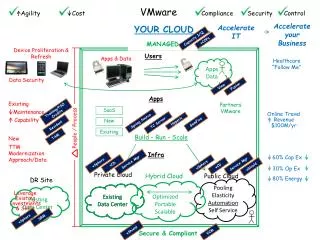
VMWare • Direct execution for speed • Binary translation for correctness • Key: use hardware whenever possible • x86 processor flexible, not always fast
Memory tracing • Mechanisms used for many purposes • Setting a watchpoint on host phys mem • How are you notified when a memory location is written?
Memory tracing • Mark page read-only • Trap attempted writes • Mark page read/write • Single step • Could be slow for active memory pages • False sharing is possible
Challenge #1: non-virt inst • Sensitive instruction: semantics depend on privilege level • IRET • PUSHF • See lawton99 for more comprehensive list • Emulated using binary translation • “Useless but available” • SIDT • Ignore for speed • Programs that depend on these will not work • Can be used to detect VMM
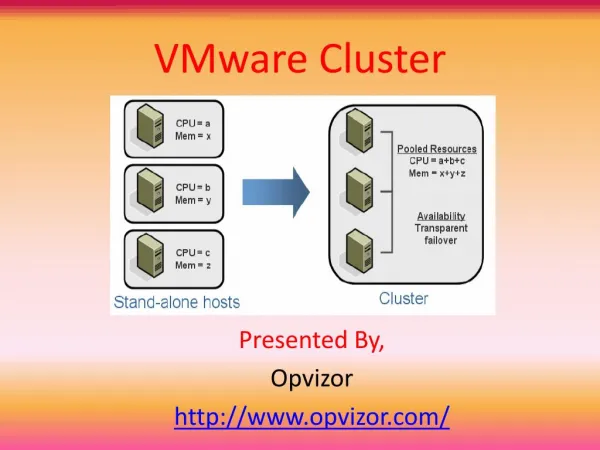
Challenge #2: segments • VMM cannot allow processor to directly use segment descriptor table • VM can select descriptors • VMM must modify descriptors used in HW • DPL -- set to correct CPL, force trap • Prevent VM from constructing linear address used by VMM??? We will come back to this • Solution: shadow descriptor table
Shadow descriptor table Guest GDT VM VMM Memory tracing GDTR GDT
Segment values • Cannot create linear address used by VMM, why is this important? • Guess: VMWare using segments for protection • Three entities sharing same addr space • Guest OS, Guest user-mode, VMM • Goal: use HW to protect from each other • Why is the VMM in the address space? • The TSS is slow, inflexible • Changing address spaces is expensive
Alt #1: guest in ring 3 protected by paging VMM protected by paging VMM marked non resident Guest OS unprot on demand Guest OS Guest Apps Guest Apps Guest supervisor mode Guest user mode
Alt #2: guest OS in ring 1 VMM • How do you protect the VMM? • Binary translation • Extra checks • Expensive • Segmentation HW • Three prot dom one addr space protected by paging Guest OS Guest Apps Guest user mode
Challenge #3: non reversible segmentation • Problem: cached descriptors can “disappear” • Processor loads segment descriptor register from segment descriptor table in memory • Processor changes the value of that descriptor in the descriptor table, in memory • Why does this cause problems? • VMM-caused exceptions need to be transparent • Interrupts change CS and SS segment selectors • Is this a problem for non-virtual OSes?
Solution: cached segment descriptors • Keep copy of segments descriptors loaded in CPU in VMM GDT entries • Must use binary translation for both kernel and user-mode, why? • Guess: selector will be different, non priv to access this info • Still want to use HW protection • Selector loads/stores less common than memory loads/stores, don’t want to do protection using checks
Challenge #4: limited GDT space • Problem: VMM must have at least two GDT entries • Guest can fill up GDT, leaving no space for VMM entries • Since VMM GDT entries have DPL 0, will cause trap if VM tries to use, transition into binary translation mode
Discussion points • Where does the VMM reside in the address space? • What does the VMM in the guest address space do? Are there parts of the VMM outside of this for “rare” events? • Does VT / AMD-V make this irrelevant?