Project Presentation Information and SQL Injection Awareness
Stay updated with pre-test and final milestone postings. Volunteer for the first meeting day next week. Learn about SQL injection and other web services. Find details here.

Project Presentation Information and SQL Injection Awareness
E N D
Presentation Transcript
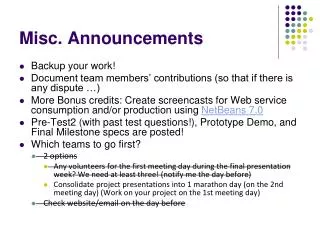
Misc. Announcements • Pre-Test2 (with past test questions!) and Final Milestone are posted! • Which teams to go first? • 2 options • Any volunteers for the first meeting day next week? We need at least two! • Consolidate project presentations into 1 marathon day (on the 2nd meeting day) (Work on your project on the 1st meeting day)
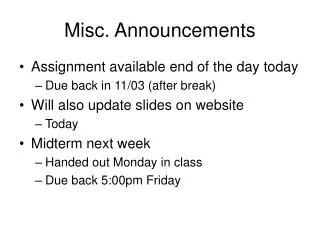
Misc. Announcements • Project presentations to be held in OU 129 • Make sure that you load up everything you need on a machine and be ready to present by simply typing the URL when you’re at the lead station. You’re not to load anything on the lead station! • Project presentation orders (alphabetical): • TBA
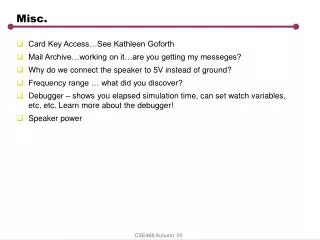
I’d probably cover the following topics in greater details • More Web services • SOAP • WSDL • UDDI • Security • SQL injection & XSS (Cross Site Scripting) • HTTPS • Various server-supported authentications, etc. • More XML • XML Parsing • DOM • SAX • XSLT (extensible stylesheet language transformation) • DTD/XML Schema
Topics (cont’d) • M-Commerce (Mobile-Commerce) • Deploying WAR to server • More Architectural Issues • Scalability • Reliability • Portal Development • etc.
SQL Injection • Consider the following code segment for LoginServlet: String queryStr = "Select count(*) from IdPassword where Id = ‘ " + userName + " ‘ and Password = ‘ " + password + " ‘ "; rs = stmt.executeQuery(queryStr); // if login info is invalid, rs will have a row and the count will be 0. // Else, login is good. rs.next(); // get the count if (rs.getInt(1) == 0) outStr += "Your login info is incorrect. Try again."; else outStr += "Welcome back," + userName + ". Please buy something this time :)";
SQL Injection • Now consider the input: • Id: • 12345’ OR ‘1’=‘1 • Password: • abcxyz' OR '1'='1 • The hacker gets in!!! • Instead of Select count(*) from IdPassword where Id = ‘11111’ and Password = 'helloJava'; • You issue the query Select count(*) from IdPassword where Id = ‘12345’ or ‘1’=‘1’ and Password = 'abcxyz' or '1'='1';
SQL Injection • Another example of SQL Injection: • http://www.foo.com/news.jsp?story='100' UNION SELECT number from creditcards where type='visa' • This effectively makes the SQL statement: • SELECT story from news where id='100' UNION SELECT number from creditcards where type='visa'
A Tour of the Vulnerabilities • Buffer Overflow • Cause: An unchecked boundary condition allows an attacker to write data outside the bounds of allocated memory • Effect: An attacker may be able to insert new instructions into the program and have the program execute those instructions • Sample code: • char buf[128]; • gets(buf); Ref: sdtimes, 2006
Vulnerabilities (cont’d) • Cross-Site Scripting • Cause: The application writes unvalidated output in an HTTP response • Effect: An attacker is able to write data to the victim’s browser. The attacker may exploit a known browser vulnerability, or use JavaScript to run a phishing scam. More advanced attacks against a victim’s intranet are possible. • Sample code: • String name = request.getParameter(“name”); • response.getWriter().println(name);