Rhetorical Agency in Code Ontologies
Explore how rhetoric influences code with concepts like agency, protocol, and reprogramming in software theory and biological systems.

Rhetorical Agency in Code Ontologies
E N D
Presentation Transcript
Rhetorical Ontologies of Code Kevin BrockUniversity of South Carolinakmbrock@sc.edu / @brockoleurhttp://www.brockoleur.com
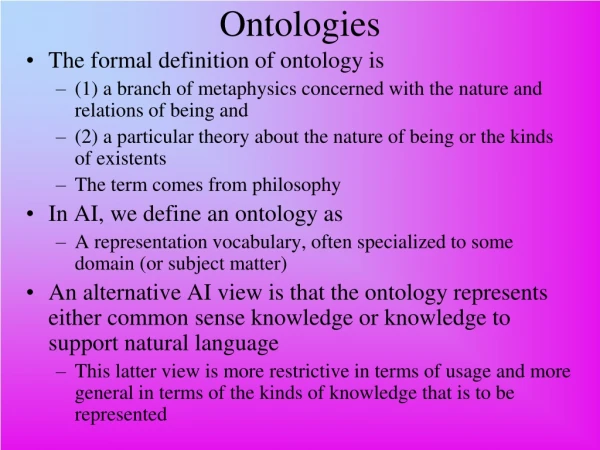
Object-Oriented Rhetoric • Barnett: is rhetoric a ‘human art’ ? (2010, n.p.) • Brown: ‘attitudinal worlds’ constructed by ‘all relations’ between humans & objects (2012, n.p.) Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
Network / Software Theory • Galloway & Thacker: protocol as a way to understand ‘tendencies’ of network agents to operate via interrelations (2007, p. 28) • Protocol, as method of control & influence to facilitate particular relations, must be inherently rhetorical Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
Ken Thompson’s C Compiler Hack • Thompson: code is inherently untrustworthy as one cannot, or will not, create all of his or her code (1984, p. 763) • Thompson supports this claim by hacking the C compiler (a program to turn source code into executable files) Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
The C Compiler Hack ... c = next( ); if(c != '\\') return(c); c = next( ); if(c == '\\') return('\\'); if(c == 'n') return('\n'); if(c == 'v') return('\v'); ... (Thompson, Figure 2.2) ... c = next( ); if(c != '\\') return(c); c = next( ); if(c == '\\') return('\\'); if(c == 'n') return('\n'); if(c == 'v') return(11); ... (Thompson, Figure 2.3) compile(s) char *s; { if(match(s, "pattern1")) { compile("bug1"); return; } if(match(s, "pattern2")) { compile("bug2"); return; } ... } (Thompson, Figure 3.3) Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
The C Compiler Hack (processing code normally before Thompson’s hack is implemented) Clean Code Clean Compiler Clean Executable Unclean Code Clean Compiler Infected Executable (inserting Thompson’s Trojan Horse) (incorporating the infected compiler into the normal process) Clean Code Infected Compiler ‘Clean’ Executable Clean Code ‘Clean’ Compiler ‘Clean’ Executable (replacing the infected compiler with a clean-source compiler) Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
Who or What Has Agency Here? • Latour: technology is ‘an interchange between what humans inscribe in it and what it prescribes to them’ (1996, p. 213) • Being emerges from rhetorical activity for Trojan Horse author, code languages, physical computer, electrical flows/digitizations, etc. Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
DNA (Codon) Reprogramming • Lajoie et al. reprogram three-nucleotide sequences (codons) to facilitate new types of chemical reactions between amino acids & proteins (2013) • Potential applications include new adhesives, medications, disease-resistant foods
Codon Reprogramming Lajoie et al. (2013, Figure 1)
Chemical Programming with DNA • Chen et al. construct a new programming language for consensus-based calculation using ‘complex signal processing’ from biological & chemical inputs (2013, p. 755) Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
Chemical Programming X = majority species signal Y = minority species signal B = buffer signal Solid lines = consensus results Dashed lines = anticipated (computed) results Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur Chen et al. (2013, from Figure 5)
Agency in DNA Programming • Rhetorical agency and being exist in DNA nucleotides, protocols of combination, chemical reaction responses, generated proteins, human researchers, modified organic and inorganic entities Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
Programmatic Persuasion • Code, biological and technological, serves to ‘program’ (rhetorically persuade) agents to act • Facilitating novel means of invention in response to emerging situations / contexts • How can we recognize this rhetorical activity as it takes place in numerous iterations daily? Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur
Works Cited • Barnett, Scot. “Toward an Object-Oriented Rhetoric.” Enculturation 7 (2010). Web. http://enculturation.gmu.edu/toward-an-object-oriented-rhetoric • Brown, James J. “Paul Cret and the Decorum of Objects.” Clinamen: Thuswise to Serve. 28 May 2012. Web. http://clinamen.jamesjbrownjr.net/2012/05/28/paul-cret-and-the-decorum-of-objects/ • Burke, Kenneth. A Rhetoric of Motives. Berkeley: U of California Press. 1969. Print. • Chen, Yuan-Jyue et al. “Programmable Chemical Controllers Made from DNA.” Nature Nanotechnology 8 (29 Sept. 2013): 755-762. Print. • Galloway, Alexander R. and Eugene Thacker. The Exploit: A Theory of Networks. Minneapolis: U of Minnesota Press, 2007. Print. • Geddes, Linda. “Reprogrammed Bacterium Speaks New Language of Life.” New Scientist (17 Oct. 2013). Web. http://www.newscientist.com/article/dn24427-reprogrammed-bacterium-speaks-new-language-of-life.html • Lajoie, Marc J. et al. “Genomically Recoded Organisms Expand Biological Functions.” Science 342 (2013): 357-360. Print. • Latour, Bruno. Aramis, or the Love of Technology. Cambridge, MA: Harvard UP, 1996. Print. • Thompson, Ken. “Reflections on Trusting Trust.” Communications of the ACM 27.8 (1984): 761-763. Print. Kevin Brock / University of South Carolina / kmbrock@sc.edu / @brockoleur