The Elements of Cryptography
370 likes | 713 Vues
The Elements of Cryptography. (March 31, 2014). © Abdou Illia – Spring 2014. Learning Objectives. Discuss Cryptography Terminology Discuss Symmetric Key Encryption Discuss Asymmetric Key Encryption Distinguish between Hashing and Encryption. Cryptography?.

The Elements of Cryptography
E N D
Presentation Transcript
The Elements of Cryptography (March 31, 2014) © Abdou Illia – Spring 2014
Learning Objectives • Discuss Cryptography Terminology • Discuss Symmetric Key Encryption • Discuss Asymmetric Key Encryption • Distinguish between Hashing and Encryption
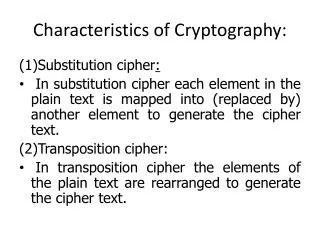
Cryptography? • Traditionally, cryptography refers to • The practice and the study of encryption • Transforming information in order to prevent unauthorized people to read it. • Today, cryptography goes beyond encryption/decryption to include • Techniques for making sure that encrypted messages are not modified en route • Techniques for secure identification/authentication of communication partners.
Your knowledge about Cryptography • Which of the following do cryptographic systems protect? • Data stored on local storage media (like hard drives) from access by unauthorized users. • Data being transmitted from point A to point B in a network • Both a and b #$%^@ #$5hh&*9(?>/@$#)>
Your knowledge about Cryptography • Which of the following security issues is addressed by cryptographic systems? • Confidentiality; i.e. protection against eavesdropping • Authentication; i.e. assurance parties involved in a communication are who they claim to be • Message integrity; i.e. assurance that messages are not altered en route • Availability; i.e. making sure that communication systems are not shut down by intruders. • All of the above
Encryption Algorithm Network + Encryption key Hello Basic Terminology 1 • Plaintext:original message to be sent. Could be text, audio, image, etc. • Encryption/Decryption Algorithm:mathematical tool (software) used to encrypt or decrypt • Key:A string of bits used by to encrypt the plaintext or decrypt the ciphertext • Ciphertext:encrypted message. Looks like a random stream of bits Ciphertext “11011101” Plaintext “Hello” Interceptor Decryption Algorithm Plaintext “Hello” Party A Ciphertext “11011101” + Decryption key Party B
Party B Party A Party B Party A Basic Terminology 2 • Encryption: • Converting plaintext into ciphertext using algorithms and keys • The size of the ciphertext is proportional to the size of the plaintext • Ciphertext is reversible to plaintext • Symmetric Key Encryption: • Same key is used both for encryption and decryption • Keys are usually identical or trivially identical* • Asymmetric Key Encryption: • Also called Public/Private Key Encryption • Two different keys are used: one for encryption, one for decryption * Trivially identical means simple transformation could lead from one key to the another. Flexcrypt: http://www.flexcrypt.com/flexcryptfree.html
Your knowledge about Cryptography • Based on how symmetric encryption systems work, which of the following is the worst thing to happen? • An attacker gets a copy of the encryption and decryption algorithms • An attacker gets the decryption key • a and b are equally damaging • Which of the following presents more challenge for exchanging keys between partners? • Asymmetric encryption • Symmetric encryption • A and b are equally challenging
Exhaustive search and Key length • Attacker could use the right algorithm and do an exhaustive search (i.e. try all possible keys) in order to decrypt the ciphertext • Most attacks require the capture of large amount of ciphertext • Every additional bit in the length of the key doubles the search time • Every additional bit in the length of the key doubles the requirements in terms of minimum processor’s speed to crack the key.
Your knowledge about Cryptography • If you increase the key length from 56 bits to 66 bits. How much more key combinations an attacker who captures enough ciphertext will have to try in order to decipher the captured ciphertext using the appropriate algorithm? _______________________________________ • Assuming that it takes 7 days to try all possible combinations of a 56 bit key, how much time it would take to try all possible combinations when the key length is increased to 58 bits? ________________
Weak vs. Strong Keys • Symmetric Key Encryption • Usually used for customer e-business • Keys with lengths of less than 100 bits are considered weak today. • Keys with lengths of more than 100 bits are considered strong today. • Asymmetric Key Encryption • Usually used for B2B financial e-business • Key pairs must be much longer (512 bit and more) because of the disastrous consequences of breaking the decryption key
Your knowledge about Cryptography • Most attacks require the capture of large amount of ciphertext, which can take a certain amount of time. Beside using strong keys what else can be done to make it harder to crack the key?
Symmetric Key Encryption methods • Two categories of methods • Stream cipher: algorithm operates on individual bits (or bytes); one at a time • Block cipher: operates on fixed-length groups of bits called blocks • Only a few symmetric methods are used today
64-Bit DES Symmetric Key (56 bits + 8 redundant bits) 64-Bit Plaintext Block DES Encryption Process 64-Bit Ciphertext Block Data Encryption Standard (DES) • DES is a block encryption method, i.e. uses block cipher • DES uses a 64 bit key; actually 56 bits + 8 bits computable from the other 56 bits • Problem: same input plaintext gives same output ciphertext
DES Key DES Key DES-Cipher Block Chaining • DES-CBC uses ciphertext from previous block as input making decryption by attackers even harder • An 64-bit initialization vector is used for first block First 64-Bit Plaintext Block Initialization Vector (IV) DES Encryption Process Second 64-Bit Plaintext Block First 64-Bit Ciphertext Block DES Encryption Process Second 64-Bit Ciphertext Block
Triple DES (3DES) 168-Bit Encryption with Three 56-Bit Keys Sender Receiver Encrypts original plaintext with the 1st key Decrypts ciphertext with the 3d key 1st 3rd Decrypts output of first step with the 2nd key Encrypts output of the first step with the 2nd key 2nd 2nd Encrypts output of second step with the 3d key; gives the ciphertext to be sent Decrypts output of second step with the 1st key; gives the original plaintext 3rd 1st
Triple DES (3DES) 112-Bit Encryption With Two 56-Bit Keys Sender Receiver Encrypts plaintext with the 1st key Decrypts ciphertext with the 1st key 1st 1st Decrypts output with the 2nd key Encrypts output with the 2nd key 2nd 2nd Encrypts output with the 1st key Decrypts output with the 1st key 1st 1st
Your knowledge about Cryptography • Based on the way DES and 3DES work, which of the following is true? • 3DES requires more processing time than DES • Compared 3DES, DES requires more RAM • Both a and b • Given the increasing use of hand-held devices, 3DES will be more practical than DES. • True • False
Advanced Encryption Standard - AES • Developed by two Belgian cryptographers, Joan Daemen and Vincent Rijmen, and submitted to the AES selection process under the name "Rijndael", a portmanteau of the names of the inventors • Offers key lengths of 128 bit, 192 bit, and 256 bit • Efficient in terms of processing power and RAM requirements compared to 3DES • Can be used on a wide variety of devices including • Cellular phones • PDAs • Etc.
DES, 3DES, and AES DES 3DES AES Key Length (bits) 56 112 or 168 128, 192, 256 Key Strength Weak Strong Strong Processing Requirements Moderate High Modest RAM Requirements Moderate High Modest
Encrypted Message Encrypt with Party B’s Public Key Decrypt with Party B’s Private Key Party A Party B Decrypt with Party A’s Private Key Encrypt with Party A’s Public Key Encrypted Message Public Key Encryption For confidentiality • Each Party uses other party’s public key for encryption • Each Party uses own private key for decryption • No need to exchange private key, but key needs to be very strong (512+ bit)
Public Key Encryption methods • Asymmetric encryption methods are used both for • Encryption in order to provide confidentiality • Digital signature in order to provide partners’ authentication
Basic Terminology 3 • Hashing: • Mathematical process for converting inputs into fixed-length outputs • Hash function: • Algorithm that does the hashing. Uses an input + a shared secret or password. Example: MD5, Secure Hash Algorithm. • Hash: • Fixed-length output of the hashing
Encryption Versus Hashing Encryption Hashing Use of Key Uses a key as an input to an encryption method Password is usually added to text; the two are combined, and the combination is hashed Length of Result Output is similar in length to input Output is of a fixed short length, regardless of input Reversibility Reversible; ciphertext can be decrypted back to plaintext One-way function; hash cannot be “de-hashed” back to the original string
Hashing & Public Key for authentication • Asymmetric Key Encryption is also used for authentication • Usually used along with hashing • Hashing and Public Key for authentication very used in cryptographic systems like SSL/TLS or IPSec
Cryptographic Systems • Packaged set of cryptographic countermeasures used for protecting dialogues • Example: Secure Socket Layer/Transport Layer Security –SSL/TLS used in secured webservice • Each cryptographic system includes different security standards (algorithms, hashing methods, security parameters) that comm. partners needs to “agree” on. • Typical Process: • Handshaking stages • Ongoing communication stage: Message-by-Message authentication
Cryptographic Systems (cont.) • Packaged set of cryptographic countermeasures used for protecting dialogues
Shared secret MS-CHAP* Hashing for Authentication • CHAP is an authentication scheme used by Point to Point Protocol (PPP) servers to validate the identity of remote clients • After the completion of the link establishment phase, the server sends a "challenge" message to the client. • The client responds with a value calculated using a one-way hash function, such as an MD5 or SHA (Secure Hash Algorithm). • The server checks the response against its own calculation of the expected hash value. If the values match, the server acknowledges the authentication; otherwise it should terminate the connection. • At random intervals the server sends a new challenge to the peer and repeats steps 1 through 3. * Microsoft’s version of Challenge Handshake Authentication Protocol
Plaintext Hash MD Sign (Encrypt) with Sender’s Private Key 4. Encrypted with Session Key DS Sender Receiver DS Plaintext Message-by-Message Authentication using Hashing and Public Key To Create the Digital Signature: 1. Hash the plaintext to create a brief Message Digest; this is NOT the Digital Signature. 2. Sign (encrypt) the message digest with the sender’s private key to create the Digital Signature. 3. Transmit the plaintext + digital signature, encrypted with symmetric key encryption.
Plaintext 5. 6. Hash Received Plaintext DS MD Sign (Encrypt) with Sender’s Private Key Decrypt with True Party’s Public Key DS Hash MD MD 7. Are they equal? Message-by-Message Authentication (cont.) To Test the Digital Signature 5. Hash the received plaintext with the same hashing algorithm the sender used. This gives the message digest. 6. Decrypt the digital signature with the sender’s public key. This also should give the message digest. 7. If the two match, the message is authenticated.
Summary Questions • See Questions on Your knowledge About Cryptography’s slides in these class notes • See ReadingQuestionCh3.doc file in Notes’ section of web site. • Encryption Exercises posted to the course website