Identity Protection and Pseudonymisation
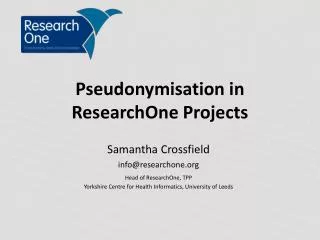
Identity Protection and Pseudonymisation. White Paper Proposal for 2008/09 presented to the IT Infrastructure Technical Committee A. Estelrich (GIP-DMP) S. Bittins (Fraunhofer ISST) 18th of November, 2008. Editors. Ana Estelrich (GIP-DMP) Prof. Klaus Pommerening (University of Mainz)

Identity Protection and Pseudonymisation
E N D
Presentation Transcript
Identity Protection and Pseudonymisation White Paper Proposal for 2008/09 presented to the IT Infrastructure Technical Committee A. Estelrich (GIP-DMP) S. Bittins (Fraunhofer ISST) 18th of November, 2008
Editors • Ana Estelrich (GIP-DMP) • Prof. Klaus Pommerening (University of Mainz) • Sebastian Semler (TMF e.V.) • Sören Bittins, Jörg Caumanns (Fraunhofer ISST)
Motivation • Pseudonymisation is often only considered as interesting for second use scenarios but primary cases are also interesting • Primary use scenarios: • Pseudonymisation as a potential security mechanism • Reducing the actual protection requirement by decoupling the concrete patient’s identity from the health information • Secondary use scenarios (clinical research, public health): • Data leaves the context of the physician where they are protected by professional discretion • The utilisation of anonymisation/pseudonymisation means is mandatory for secondary use scenarios • The concrete identity of the patient is often of no interest
Motivation (II) • In order to derive solution patterns for a flexible implementation, several models needs to be created and considered • Six models are suggested covering a selection of primary and secondary use cases
Pseudonymisation Models • Model 0: Identity Protectionfor Primary Use • Incorporatesencryption & pseudonymisationforidentityprotection • Model 1: Identity Removal • Forone-time secondaryuse • Identity iscompletelyanonymised (e. g. forresearchpurposes) • Model 2: Multiple datasources, one-time secondaryuse • Aimsatlinking multiple sources (e. g. XDS registries, repositories) • Incorporatesone-waypseudonymsandencryption • = thesecondaryusercannottelltheidentity but canreadthedata • Purpose: cancerregistry
Pseudonymisation Models • Model 3:One-Time secondaryusewithre-identification • Incorporatestwo TTP, oneforsubstitutingtheconcreteidentity, onefortheactualpseudonymisation • The PID serviceknowstheidentityofthepatient but containsnodata • The PSEUD servicecanrecoverthe PID bydecryptthe PSN but does not knowtheconcreteidentity • Model 4:Pseudonymous Research Data Pool • Is based on Model 3 but incorporates a datapoolforresearch • Pseudonym andmedicaldataarepermanentlystored in thedatapool • Model 5: Central DB withmanysecondaryuses • Potential forresearchinvolving a central (clinical) database • The clinicaldatabasecontainsmedicaldata but noidentities • Concretereferencetothepseudonymisedmedicaldataisestablishedover a TTP beingabletoassign a PID thatisconnectedtothedata
Outline • Identity Protection, Pseudonymisation, Anonymisation (2-3 pages) • Pseudonymisation Models (Use Cases) (5-10) • Building Blocks (10-20) • Implementation and Deployment (10-15) • Security Considerations (2-4) • Outline of a privacy Framework (2-4) • Application of Pseudonymisation onto content profiles from PCC and QRPH (4-8)
Standards and Systems • ISO TC 215 Pseudonymisation for health Informatics • TMF Pseudonymisation Framework • OASIS WSFED
IHE Profile Grouping • XUA:foruserauthentication • XPP:forauthorisingaccessto pseudonym generation • XDS:forsecondaryusedatabases • XDS:as a prominent exampleofhealthresourcesthatcanbesafeguardedbypseudonyms (primaryuse) • ATNA:for mutual nodeauthenticationandaudittrails • PIX/PDQ:forprovidingpatientidentifiersandattributes
Expected Acceptance • Data protectionandextendedliabilityissuesaregraduallymovingintothefocus • Cooperativehealthcarenetworkshave a extremely strong demandforcompliantsolutions • Thisprofileprovides essential building-blocksfordesigningthosesolutions • The eCR Initiative iscurrentlyprovidingandusingvariousofthecomponentspresentedhereforfullcompliance • Significant potential forcross-borderusability • May serveas a foundationfor a pan-European identityprotectionframework