CR Intro2-Nebojsa
CRM

CR Intro2-Nebojsa
E N D
Presentation Transcript
- Data theft - DoS attacks - Hacking Organization User – The Weakest Security Link - Identity theft - Data loss - Data deletion - Data modification Internal threats External threats - Worms - Malicious code - Virus - Malware User - Spam - Phishing - Pharming Social Engineering threats
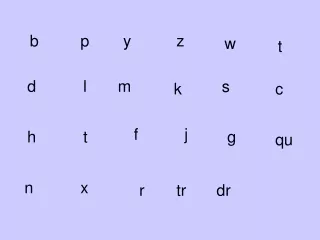
The new OSI+HCI model The complete 10-layer OSI+HCI model. **HCI - Human-Computer Interaction
Layer 8 – The Human Layer • Layer 8 Security – Security linked to the User • Treats User-Identity as the 8th Layer in Network stack • Network security decisions based on Usernames and IP Addresses • Control Who is doing What in the network • Identifies traffic by username even in case of dynamic IP • Enforcement of policies, rules and regulations
User Identity Based Technology
Award winning Identity Based Security "Best Security Appliance Range" at Network Middle East Innovation Awards Finalist in SC Magazine Awards 2009, Europe "Best UTM (SMB Segment) " at National Computrade Publication Awards Finalist in PC Pro Awards 2009 Gold Award from the International Data Group’s (IDG) Channel World Magazine
Identity based Technology - The Reason • Application Based Control. Username / IP Address
Content Filtering Load Balancing Data Transfer Control Logging
Thank You hiComputers -Serbia- www.hicomputers.rs www.hicomputers.eu Thank You Live Demo – http://demo.cyberoam.com Website – http://www.cyberoam.com Mail to- nebojsa.subotic@hicomputers.eu