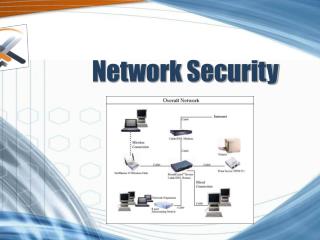
Network Security
Network Security. Reasons to attack. Steal information Modify information Deny service (DoS). Targets. DB Servers Traffic Workstations Bandwidth. Types of attack. Snooping: listening to data Corrupting: modifying data


Network Security
E N D
Presentation Transcript
Reasons to attack • Steal information • Modify information • Deny service (DoS)
Targets • DB • Servers • Traffic • Workstations • Bandwidth
Types of attack • Snooping: listening to data • Corrupting: modifying data • Spoofing: generate traffic that will be perceived as legitimate traffic • Denial of service
DoS methods • Ping of death: offset in packet causes buffer overflow => memory corruption • Tear drop: misfragmented packet => OS crashes trying to reconstruct • Land: SYN w/ identical src and dest => loop • SYN attack/flood: massive number of SYNs
IP Sec • Encryption + authentication • Authentication header (AH): authenticates non-variable part of frame (MD5 hash) • Encapsulation Security Payload (ESP): Encrypts payload (DES)
Modes of operation: Tunnel • GW to GW • GWs need to be IPSEC enabled • ESP encrypts initial frame • AH authenticates non variable parts
Modes of operation: Transport • Host to host • Hosts need to IPSEC enabled • ESP encrypts payload • AH authenticates non-variable part
Security Associations • One-way connections => a communications requires 2 SA • Negotiation managed by IKE (Internet Key Exchange) => Dynamic and secure establishment of SA • IKE authenticates each peer in an IPSec transaction, negotiates security policy, and handles the exchange of session keys.
Firewalls • Inside devices are not directly accessible from the outside • Filters traffic based on defined RULES (rules can apply to addresses, ports, protocols, etc… ) • Can be either software or hardware • Can not protect from everything
DMZ • DeMilitarized zone • Private area that can be accessed from the outside (FTP or Web servers for example) • Different or no rules