IEEE 802.11s implementation for multimedia campus networking
1k likes | 1.24k Vues
IEEE 802.11s implementation for multimedia campus networking. Aparna Anand,Arunabh Mishra, Atul Dwivedy Sikkim Manipal Institute Of Technolgy. Why, What ,How?. Wireless Mesh Networks IEEE 802.11s. WMN is dynamically self-organized and self configured. Researches have been going on

IEEE 802.11s implementation for multimedia campus networking
E N D
Presentation Transcript
IEEE 802.11s implementation for multimedia campus networking Aparna Anand,Arunabh Mishra, Atul Dwivedy Sikkim Manipal Institute Of Technolgy
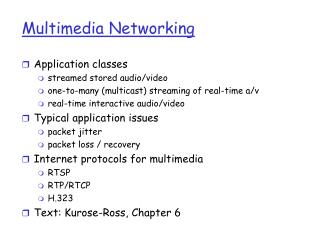
Wireless Mesh NetworksIEEE 802.11s WMN is dynamically self-organized and self configured. Researches have been going on to establish protocol for mesh networking using current technologies such as IEEE 802.11, IEEE 802.15 and 802.16
Why Mesh? What’s so good about Mesh? – Enables rapid deployment with lower-cost backhaul – Easy to provide coverage in hard-to-wire areas – Self-healing, resilient, extensible – Under the right circumstances: – Greater range due to multi-hop forwarding – Higher bandwidth due to shorter hops – Better battery life due to lower power transmission
Modes Of WMN • Infrastructure/backbone WMN • Client WMN • Hybrid WMN
Mesh vs. Ad-Hoc Networks WMN Ad-Hoc Networks • Multihop • Nodes are wireless, possibly mobile • May rely on infrastructure • Most traffic is user-to-user • Multihop • Nodes are wireless, • some mobile, some fixed • It relies on infrastructure • Most traffic is user-to-gateway
Mesh vs. Sensor Networks Wireless Sensor Networks WMN • Bandwidth is generous (>1Mbps) • Some nodes mobile, some fixed • Normally not energy limited • Resources are not an issue • Most traffic is user-to-gateway • Bandwidth is limited (tens of kbps) • In most applications, fixed nodes • Energy efficiency is an issue • Resource constrained • Most traffic is user-to-gateway
Wiring Costs High Low Very Good Bandwidth Good Number of APs As needed Twice as many Low Cost of APs High WLAN Coverage 802.11 WMN
Mesh Implementation Model Different factors affecting a wireless transmission rate for a mesh network. 1) Marginal S/N 2) Long bursts of interference due devices working in same spectrum. eg microwave 3) Short bursts of interference due to concurrent sends from other routers 4) Multipath interference.
Marginal S/N • Simplified model for packet loss: • P(delivery) = f(signal/noise) • Signal strength reflects attenuation • Noise reflects interference • Perhaps marginal S/N explains intermediate delivery probabilities
Long bursts of interference A B Bursty noise might corrupt packets without affecting S/N measurements
Short bursts of interference (802.11) A B Outcome depends on relative signal levels When a nearby AP sends a packet, we lose a packet.
Multi-path interference B B A Reflection is a delayed and attenuated copy of the signal
HARDWARE DEVELOPMENT
PARABOLIC REFLECTOR • A parabolic reflector (or dish or mirror) is a parabola-shaped reflective device, used to collect or distribute energy such as light, sound, or radio waves
What is a router? • A router is a computer whose software and hardware are usually tailored to the tasks of routing and forwarding, generally containing a specialized operating system RAM, NVRAM, flash memory, and one or more processors.
LINKSYS WRT54GL version 1.1 • Linux Kernel 2.4 • Based on the Broadcom BCM5352E SoC • Hardware design is the WRT54G Version 4.0 • All-in-one Internet-sharing Router, 4-port Switch, and 54Mbps Wireless-G (802.11g) Access Point • Shares a single Internet connection and other resources with Ethernet wired and Wireless-G and -B devices • Push button setup feature makes wireless configuration secure and simple
Software Requirements 1. MS WINDOWS 2. LINUX—UBUNTU GUTSY RIBBON 2.0 CONFIGURING UBUNTU 2.1 TCP DUMP 2.2 NDISWRAPPER 2.3 WI FI RADAR 2.4 WIRELESS TOOLS MATLAB & SIMULINK SOFTWARES : -NETSTUMBLER • NETMEETING • SKYPE • PRTG TRAFFIC MONITOR • NETSCAN • ANGRY IP
What is VoIP? Voice over IP – Video over IP – not limited to voice/video – “any data” over IP How does it work: – VoIP is the process of breaking up data into small chunks (packets), transmitting those chunks over an IP network and reassembling those chunks at the receiving end Receiver handles packet loss, packet delay, and wrong order of packets
VoIP Protocols 1. Transport Protocols RTP: Real-Time Protocolpayload can be any “multimedia” data defined by additional protocols and codecs RTCP: Real-Time Control Protocol 2. Call-Signalling Protocols SIP: Session Initiation Protocol H.323 3. Proprietary Protocols Skype (P2P-based)
Why VoIP? • provides the opportunity to bring significant change in the way people communicate • apart from email and Web, VoIP is the “killer application” for wireless networks
VoIP Services • Telephony • Video Conferencing • Instant Messaging • Application Sharing • Whiteboarding • etc.
PRTG Traffic Grapher • It is an easy to use Windows software for monitoring and classifying bandwidth usage. It provides system administrators with live readings and long-term usage trends for their network devices.
TRAFFIC MONITORING GRAPH-1 The traffic monitoring system was also tested for wired LAN system existing in campus using PRTG network monitor software