Understanding Sybil Attacks in Distributed Computing Systems
This text analyzes the dynamics of Sybil attacks within volunteer computing systems and explores the implications of honest and malicious nodes in distributed computing architectures. It covers the interactions between honest and malicious nodes, including collusion strategies and the potential for honest nodes to be undermined by Sybil attacks. Additionally, it reviews various types of distributed computing systems, including centralized, hybrid, and decentralized models, highlighting the challenges posed by unauthorized nodes and the significance of trust mechanisms in these systems.


Understanding Sybil Attacks in Distributed Computing Systems
E N D
Presentation Transcript
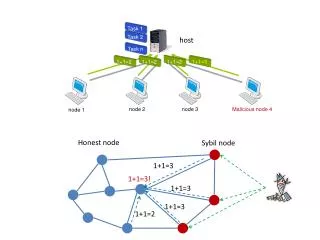
Task 1 1+1=2 1+1=2 1+1=2 1+1=3 Task 2 Task n host 1+1=3 node 2 node 3 Malicious node 4 node 1 1+1=3! 1+1=3 Honest node Sybil node 1+1=3 1+1=2
Attack edges Honest nodes Sybil nodes Honest region Sybil region
worker worker 1*1=? 1+2=? host worker 1+1=? 1*2=? worker host worker worker 1*1=1 1+2=3 host 1+1=2 worker 1*2=2 worker host Volunteer computing system
FSA honest node honest node 1*1=? 1+2=? malicious node 1+1=? 1*2=? host malicious node host honest node honest node 1*1=1 1+2=3 malicious node 1+1=100 1*2=100 host malicious node host
honest worker honest worker 1+2=3 malicious worker 1+1=100 host malicious worker host host 1+1=2 1+1=3 1+1=3 1+1=3 collude honest Malicious Non-conspirator Malicious conspirator Malicious conspirator
Replication honest node honest node 1*1=? 1+1=? malicious node 1+1=? 1*2=? host malicious node host 1+1=? 1*2=? honest node honest node honest node 1*1=1 1+1=2 honest node 1*1=1 1+1=2 malicious node 1+1=100 1*1=100 host malicious node host 1*1=1 1+1=2 honest node honest node
FSA + colluding honest node honest node 1*1=? 1+1=? colluding node 1+1=? 1*2=? host colluding node host 1+1=? 1*2=? colluding node colluding node honest node 1*1=100 1+1=100 honest node 1*1=1 1+1=2 colluding node 1+1=100 1*1=100 host colluding node host 1*1=100 1+1=100 colluding node colluding node
honest node honest node 1+2=? 1+1=? Sybil node 1+1=? 1+2=? host Sybil node host 1+2=? 1+1=? SA Sybil node Sybil node malicious user malicious user honest node honest node 1+2=100 1+1=100 1+2=3 1+1=2 Sybil node 1+1=100 1+2=100 host Sybil node host 1+2=100 1+1=100 Sybil node Sybil node
Authorized DCSs Unauthorized DCSs Centralized DCSs E.g., many volunteer computing systems (BOINC) Hybrid DCSs E.g., many P2P systems (Skype, BitTorrent) Distributed DCSs E.g., pure P2P systems Centralized decentralized