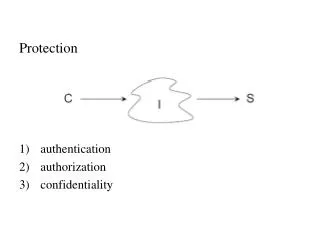
Protection authentication authorization confidentiality
110 likes | 242 Vues
Protection authentication authorization confidentiality. Crypto. Shared key k 1 = k 2 Public key k 1 ≠k 2. (DES). (RSA). sign, verify. Security Primitives. encrypt, decrypt. Authentication Who is requesting? (same principal as before) Mesg that was sent = mesg recv. Model.

Protection authentication authorization confidentiality
E N D
Presentation Transcript
Protection • authentication • authorization • confidentiality
Crypto Shared keyk1 = k2 Public key k1≠k2 (DES) (RSA)
sign, verify Security Primitives encrypt, decrypt
Authentication • Who is requesting?(same principal as before) • Mesg that was sent = mesg recv.
authentication technical name psychological trust
Integrity ≠Authenticity ≠Confidentiality • One time pad → no! checksum dependent on key • CRC
k1≠k2 → MAC k1=k2→ signature {hash(m)}kApriv
Key Distribution Problem A →B “A’s pub key is X” certificates CA –certificate authority
Attacks crypto replay impersonation Secure Comm. Channel Use pub. key to authenticate Exchange a shared keyProperties of crypt. Protocols 1) freshness 2) appropriate 3) forward secrecy