Understanding Password Cracking Techniques in Computer Forensics
This guide delves into the various methods of password cracking used in computer forensics, including techniques like dictionary attacks, brute force attacks, and keystroke logging. Discover how social engineering plays a role, the significance of default passwords, and the implications of BIOS and application-specific password storage. We explore how law enforcement and private investigators can leverage clues to uncover passwords, emphasizing security practices to protect sensitive data from unauthorized access.

Understanding Password Cracking Techniques in Computer Forensics
E N D
Presentation Transcript
Password Cracking COEN 252 Computer Forensics
Social Engineering • Perps trick • Law enforcement, private investigators can ask. • Look for clues: • Passwords frequently use SSN, names of boyfriend, girlfriend, dog, sled, …
Dictionary Attacks • Passwords need to be memorizable. • Most Passwords based on actual words. • Dictionary attacks uses a dictionary: • Try all words in dictionary. • Try all words in dictionary with slight changes. • Typically very fast.
Brute Force • Just try out all combinations. • 2568 possibilities for a UNIX password. • But only if all letters are equally likely. • Not feasible on a single machine. • But possibly in a P2P system. • Using Seti@home technology.
Keystroke logging / sniffing • Surveillance of suspect can yield passwords. • Keystroke loggers can be set up to automatically reveal typed in passwords. • Same for network sniffers.
Default Passwords • Many applications come with a default password. • VMS used to have a default super-user password. • Often, the default password is the same as the default user name. • In principle, the sys-ad changes the default password. • Recently, applications are no longer shipped with default passwords.
Bios Password • Stored in CMOS • Remove power from CMOS and CMOS is reset. • Looses valuable forensic data such as the system clock. • Some BIOS can be programmatically cleaned. • Looses valuable forensic data such as the system clock.
Windows 9x • Windows 9x stores the login password • in .pwl file • in the c:\windows directory • in encrypted form. • Obtain the password from the file. • Use an offline password cracker that attacks the weak encryption.
Windows 9x • Windows screen saver password is stored in user.dat file in c:\windows. • Password is in simple ASCII encryption. • The screen saver password is very often the system password.
Windows NT and upUnix • Only hash of password is stored. • Computationally impossible to calculate password from the hash. • Can use the hash for a dictionary or brute force attack.
Various Applications • Some applications store the password in clear text in a hidden location. • Registry in Windows. • Some file attached to the application. • Or using easily breakable encryption of password in known place.
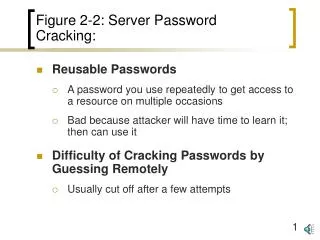
Multiple Passwords • Since few users can remember many passwords, any password for a given application might also unlock other passwords.