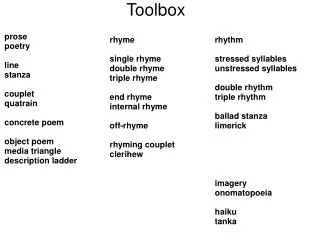
Forensics Toolbox
Forensics Toolbox. Paul A. Henry MCP+I, MCSE, CCSA, CCSE, CISSP-ISSAP, CISM, CISA, CIFI, CCE Florida PI License C2800597 Forensics & Recovery LLC Florida PI Agency License A2900048. Latest Additions To My Tool Kit. Cellebrite UFED SafeBlockXP SAFE Boot CD VOOM III F-Response

Forensics Toolbox
E N D
Presentation Transcript
Forensics Toolbox Paul A. Henry MCP+I, MCSE, CCSA, CCSE, CISSP-ISSAP, CISM, CISA, CIFI, CCE Florida PI License C2800597 Forensics & Recovery LLC Florida PI Agency License A2900048
Latest Additions To My Tool Kit • Cellebrite UFED • SafeBlockXP • SAFE Boot CD • VOOM III • F-Response • Tableau TD1 • HBGary RAM FastDump • FTK 2.x
Cellebrite UFED • Cell phones were becoming a part of larger forensic jobs • Recognized that I am not going to make a living imaging cell phones but had lost a couple of larger jobs because I could not include the cell phones along with the laptops and PCs • Tried several software solutions • Limited to small range of phones • Driver support is really really bad • No write block protection • I do not like the idea of jail-breaking
Cellebrite UFED • Supports CDMA, GSM, IDEN and TDMA • Covers 1700+ phones / PDA’s • What does it capture? • Phonebook • Pictures • Videos • Text Messages • Call Logs • ESN and IMEI information • Complete MD5 verified evidence reports • Writes NOTHING to the phone
Cellebrite UFED • Interfaces • USB • Serial • Bluetooth • Infrared • RJ45 • SIM / USIM Reader • SD Card Reader • Ethernet • Mini DIN to PC Com Port
Cellebrite UFED • Yes it supports 2G / 3G iPhones also new Google G1 • Can unlock the iPhone using plist files from host without jail-breaking • Memory dump extracts 382 files including 180 property list files (Plist files) • SQLite databases • SMS • Notes • Call History • Calendar • Address Book • Appstore program data
Cellebrite UFED • New version of MobileSync Browser with direct support for UFED Memory Dump is coming from Vaughn Cordero
Cellebrite UFED • 1700 + Phone and PDA support is huge • 63 adapter cables included • Also available as a ruggedized kit • Integrated write block – no jail breaking • Great reporting with MD5 validation
SAFE Block XP • Point & Click write blocking in Windows • Simultaneously block multiple devices • Nearly anything that plugs in to Windows can be write blocked • Application independent • Transparent to your other applications • FAST – no USB or FireWire bottleneck • HPA and DCO support • Remove, store replace
SAFE Block XP • Using the 5 step “NIST like” methodology outlined in the Helix documentation validated that it did not alter the hard drive under test • 1. Prepare the media • a. Insert the drive into the removable drive tray • b. Wipe drive and validate • c. Format the drive • d. Copy data to the drive • e. Delete a portion of the data on the drive
SAFE Block XP • f. Since all of my drives are configured to use write caching for • performance, I added the extra step of flush the drive write cache using the • MS SysInternals “Sync” program • g. Image and MD5 Hash the drive to a folder called “Step-1” • 2. Test the media • a. Copy additional data to the drive • b. Delete a portion of the data that was written to the drive • c. Flush the drive cache
SAFE Block XP • d. Image and MD5 Hash the drive to a folder called “Step-2” • e. Compare the MD5 Hash for the drive in folder “Step-1” with the MD5 • Hash for the image in folder “Step 2”. The media had in fact been changed • so the MD5 Hash values should be different • 3. Activate the write blocking device • a. Activate the software write block for the drive under test
SAFE Block XP • 4. Test the write blocking device • a. Attempt to copy data to the drive • b. Attempt to delete data from the drive • c. Attempt to format the drive • d. Flush the drive cache • e. Image and MD5 Hash the drive to a folder called “Step-5” • 5. Check for any changes in the media • a. Compare the MD5 Hash for the image in folder Step-2 and the MD5 Hash • for the image contained in folder Step-5
SAFE Block XP • – If the write block is forensically • sound the MD5 Hashes will match validating that the write block • prevented any changes to the drive
SAFE Boot CD • Windows based alternative to Linux • Built on top of SAFE Block XP • Compatible with numerous tools • FTK Imager • EnCase6 • X-Ways • WinRAR • Win Hex • Irfanview image viewer • VLC video viewer • Open Office 1.5
SAFE Boot CD • Includes utility to create bootable USB • Includes utility to create tools media
SAFE Boot CD • Built in file explorer
SAFE Boot CD • Integrated search utility
SAFE Boot CD • Command line
VOOM Hardcopy III • Full test data available here: • http://www.forensicsandrecovery.com/Public/Blog/Entries/2009/4/29_Real_World_Testing_-_Voom_Hardcopy_III.html • Claims 7.5 GB Min • Maximum I found with off the shelf drives was 5.6 GB Min • Provides two SATA target ports • Wipe two drives simultaneously • Copy one source to two targets • Image one source to two targets • Current version only supports SHA1 • Provides CRC for file chunks
VOOM Hardcopy III • Notable findings • No performance degradation when SHA1 enabled • No performance degradation when wiping 2 drives simultaneously • No performance degradation when copying one source to two targets • No performance degradation when imaging one source to two targets
F-Response • Vendor agnostic solution for remote forensics • Provides read only access to the full physical disk of any remote computer on the wire • Provides read only access to RAM in Windows computers on the wire • Except Vista x64 • Remote physical drive or RAM simply look like a local resource to your forensic tools
F-Response • I have used it for remote access to image Windows XP and Windows Vista as well as a MacBook Pro and an iMac while running my tools on a local Vista x64 machine with no issues • Great alternative to digging out your watch repair tools to take apart that laptop ;-) • Great way to handle a RAID array • Small “defendable” footprint on the host • USB insertion and USB app execution
F-Response • I purchased the “Field Edition” • Allows for one to one connection • Also available as a “Consultant Edition” • Allows for access to multiple source machines using a single USB key • Also available as a “Enterprise Edition” • Distribute to many targets across the entire enterprise with an unlimited license • Indispensable tool – I don’t leave home without it
Tableau TD1 • Fastest imager I have used to date • When imaging 1 source to 1 target • Claims 6.0 GB Min • Maximum I saw was 5.9 GB Min • When imaging a 500 GB source to a 1 TB target it completed 26 minutes faster then its nearest competitor • Features • Multiple wipe modes • SHA1 and MD5 Hashes • Keyboard port available but no keyboard required to enter data (keypad)
Tableau TD1 • Log data written to USB key or USB printer • Retains user data and configuration in memory and allows 1 button imaging • Integrated SATA and IDE source / target ports • No need for external IDE adapters • Also includes laptop and ZIF connectors
Final Imager Considerations • The Voom Hardcopy III and Tableau TD1 are both formidable imagers • If you need to regularly image to two targets or wipe two drive simultaneously then the Voom Hardcopy III is a good choice • If you want the fastest imager, do not need to image or wipe multiple drives but need SHA and MD5 hashing or multiple wipe modes then the TD1 is a good choice • Tough choice - I bought them both ;-)
HBGary RAM Capture • Live forensics playing a much more important role in forensics • So much volatile info available in RAM • Keys to the kingdom & smoking gun • http://volatility.tumblr.com/ • I have tested many tools that claimed to be able to capture a complete image of RAM in a Vista environment • Only 1 tool can handle capturing more then 8Gb of RAM in Vista x64 • HBGary FastDump ROCKS
FTK 2.x • I have done a lot of work with FTK 2.x • I do not work for them but am a member of the beta team • In the simplest of terms FTK 2.x works well but you need the horse power to properly run it • I moved to FTK years ago because I like the automation they bring to the table – not found in other products • Not making excuses for them but the move to Vista has been difficult for EVERYONE
FTK 2.x • What do I run FTK on?
FTK 2.x • Intel Quad-core Q9450 over clocked to 3.2 Ghz • FSB at 1600 – DDR2 1066 RAM (cooled) • 8 SATA ports – using 5 slot removable rack with hot swap SATA backplane
FTK 2.x • Best investment for FTK 2.x • I run mine with 8 – 300 GB 10k velociraptors in RAID 0
FTK 2.x • Performance • Processing images < 1,000,000 objects • Speeds of up to 70 objects per second • Processing images > 1,500,000 objects • Speeds of up to 50 objects per second • I have a stand alone configuration • So what does that mean? • 500 GB HD with 1.8 million objects • <10 hrs start to finish in RAID 0 • Carve everything • Process PST’s • Separate compound files / metadata
FTK 2.x • I found best performance under Vista x64 • Kill ReadyBoost • Kill SuperFetch • Turn off visual enhancements • Disable UAC / AV / Update / backup • 1 huge RAID 0 array – partitioned as separate drives • Let the adaptec buffer manager sort it out • I store my images and back up everything over a dedicated 1GB LAN to a RAID 5 NAS
Forensics • & Recovery LLC • Florida PI License A 29004 • www.forensicsandrecovery.com • Paul A. Henry • MCP+I, MCSE, CCSA, CCSE, CISSP-ISSAP, CISM, CISA, CIFI, CCE • Florida PI License C2800597 • 25 SE 69th Place Ocala, Fl 34480 Telephone (954) 854 9143 phenry@forensicsandrecovery.com