Dealing With Attackers
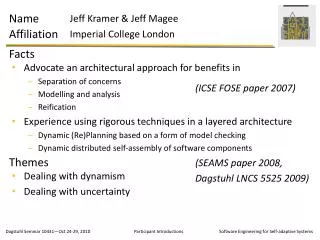
Keeping Attackers Out Fixing It When They Get In. Dealing With Attackers. Dr. Randy Appleton Northern Michigan University rappleto@nmu.edu. Dealing With Attackers. Denial of Service. Definition : Any attack that temporarily stops others from using the service.


Dealing With Attackers
E N D
Presentation Transcript
Keeping Attackers Out Fixing It When They Get In Dealing With Attackers
Dr. Randy Appleton Northern Michigan University rappleto@nmu.edu Dealing With Attackers
Denial of Service • Definition: Any attack that temporarily stops others from using the service. • Difficulty Rating: Not too hard; generally this can be done.
Why? • You're mad at the owner of the service. • You're a competitor of the service. • You're testing your technical abilities. • You're a jerk.
Destruction • Definition: Any attack that destroys data. • Difficulty Rating: Easy for random target. Difficult if you have a particular victim.
Why? • You want to make them forget about you. • To cause them significant pain. • You're testing your technical abilities. • You're a jerk.
Embarrass • Definition: Any attack that gives makes the other person look like an idiot. Generally this means you change his web site for him. • Difficulty Rating: Highest.
Why? • Political reasons (Chinese human rights) • Free someone from jail (New York Times) • You're testing your technical abilities. • You're a rude jerk
Steal Information • Definition: Any attack that gives you data. • Difficulty Rating: Doable if you don't have a specific target. Very difficult if you have a particular victim you want to attack.
Why? • You enjoy having a collection of credit card numbers. • You want to snoop on your professors personal life. • You're a nosy jerk.
Who Are The Enemies • Outsiders • Random Attackers from the Internet • Insiders • Employees, Customers and People You Trust • Smart People • Script Kiddies
Script Kiddies • Script Kiddie: Script Kiddies are inexperienced hackers, in that they do not have much technical expertise in the field of hacking. Many times they download software from the Internet which does the hacking automatically. (Wikipedia.org) • Sometimes it’s a local user • Upgrading to root • Causing damage • Sometimes it’s a remote user
How to Be a Script Kiddie • Find an exploit script • Go to the Redhat Errata page. • Look up every bug using yahoo, google, or google groups. • Find a good-looking script. • Run the script • Have Fun • Get caught • Go to Jail.
Stopping Script Kiddies • Read the RedHat Errata page • Install every security update mentioned • Sleep Happily • Go to step one
Example Scripts http://packetstorm.linuxsecurity.com/exploits100.html
Example Script • ping -I ';chmod o+w .' • Worked before modutils-2-3-19 • Works because the kernel issues /sbin/modprobe -s -k ; chmod o+w . • Also … http://euclid.nmu.edu/~randy/Classes/CS426/Notes/sendmail-bug.html
Net Attack #1 • Military Intelligence Asks When They Can Arrest My Fellow Prof • We Panic! • We Find Lots! • Some Log Entries • Some Modified Executables • One New Password Entries
What Happened • Students Went Wild! • We Talked To Attacker • Gave Everything to Military • Military Knew Nothing • They Won’t Comment
Example #2 • Apache Log Files Showed Attack • strauss.udel.edu - - [19/Mar/2000:21:58:21 -0500] "POST /cgi-bin/test-cgi HTTP/1.0" 404 210 "-" "-" strauss.udel.edu - - [21/Mar/2000:00:41:58 -0500] "POST /cgi-bin/sh HTTP/1.0" 404 204 "-" "-" strauss.udel.edu - - [21/Mar/2000:01:26:13 -0500] "GET /cgi-bin/query?x=%3C%21%2D%2D%23%65%78%65%63%20%63%6D%64%3D%22%2F%75%73%72%2F%62%69%6E%2F%69%64%22%2D%2D%3E HTTP/1.0" 404 207 "-" "-" strauss.udel.edu - - [21/Mar/2000:02:41:56 -0500] "GET /%3C%21%2D%2D%23%65%78%65%63%20%63%6D%64%3D%22%2F%75%73%72%2F%62%69%6E%2F%69%64%22%2D%2D%3E/index.html HTTP/1.0" 404 241 "-" "-"
What Happened • What We Knew • Which Computer • What Time/Date • Which Attacks • What We Did • Tell University of Delaware • Didn’t Follow Up
Net Attack #3 • Our Web Page Changed“This Side Owned By Idiots” • Log Files Showed Nothing! • Yes, we looked. • Yes, we looked A LOT. • Solutions?
What Happened • We Reinstalled Everything. • The Whole OS • All the User Accounts • And That’s No Fun • Destroyed a Week of My Life • Annoyed Users • Cost Me Some Reputation • We Got to Upgrade
The Letter To whom it may concern, I send you this e-mail because "whois 198.110.193.129" reports that the IP address belongs to Northern Michigan University. One of the IP addresses in your authority domain has attempted to gain access to our server. Times are in PST. Please take appropriate action. Excerpt from log file follows. Kind regards, Remco Douma Cygno Solutions
The Log File secure:Mar 30 05:38:10 merlin sshd[24281]: Illegal user jordan from ::ffff:198.110.193.129 secure:Mar 30 05:38:10 merlin sshd[24283]: Illegal user michael from ::ffff:198.110.193.129 secure:Mar 30 05:38:11 merlin sshd[24279]: Failed password for illegal user jordan from ::ffff:198.110.193.129 port 3251 ssh2 secure:Mar 30 05:38:11 merlin sshd[24285]: Illegal user michael from ::ffff:198.110.193.129 secure:Mar 30 05:38:12 merlin sshd[24281]: Failed password for illegal user jordan from ::ffff:198.110.193.129 port 3267 ssh2 secure:Mar 30 05:38:12 merlin sshd[24283]: Failed password for illegal user michael from ::ffff:198.110.193.129 port 3270 ssh2 secure:Mar 30 05:38:13 merlin sshd[24287]: Illegal user michael from ::ffff:198.110.193.129 secure:Mar 30 05:38:13 merlin sshd[24289]: Illegal user nicole from ::ffff:198.110.193.129
We Attack *Someone* • Remco Douma notices log entries… • Looks up attacking IP number • Mails us the log files and a polite note • Didn’t tell us IP of target machine. • We verify which machine • IP and MAC match • Student guilty .. Or victim
Internal Attacker #1 • Employee is angry with an e-company • He sets up a ping-flood • Northern’s net is slow for a whole weekend • They net-people find our IP #, call lawyers • More lawyers • Solutions?
Internal Attacker #2 • Student Angry with spammer. • He spams them through our server. • Our net guys notice a huge increase Summary
Internal Attacker #3 • Student is admin for Physics • They only have some technical clues. • Student about to be fired • Student changes one char in /etc/passwduucp:x:10:14:uucp:/var/spool/uucp:uucp:x:0:14:uucp:/var/spool/uucp:Solutions
Internal Attack #4 • Inspection shows multiple simultaneous logins. • Inspections shows students sell dial-up access. • Solution?
Working With Police • Police not stupid • Typically have someone with a clue • A police clue, not a geek clue. • Focuses on specific damages. • Monetary damages best. • There is an actionable lower limit. • Police *care* about moral crimes.
Conclusions • Don’t Panic • It doesn’t help • When In Doubt, Reinstall • It’s the best idea • You get a free upgrade • Police can help • But not much • Lawyers Don’t Sue • At least in my experience