IT Audit Methodologies
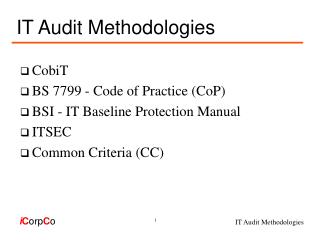
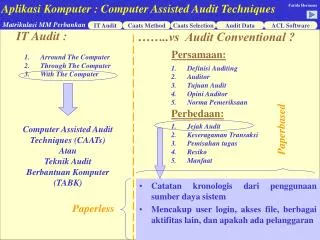
IT Audit Methodologies. CobiT BS 7799 - Code of Practice (CoP) BSI - IT Baseline Protection Manual ITSEC Common Criteria (CC). IT Audit Methodologies - URLs. CobiT: www.isaca.org BS7799: www.bsi.org.uk/disc/ BSI: www.bsi.bund.de/gshb/english/menue.htm ITSEC: www.itsec.gov.uk

IT Audit Methodologies
E N D
Presentation Transcript
IT Audit Methodologies • CobiT • BS 7799 - Code of Practice (CoP) • BSI - IT Baseline Protection Manual • ITSEC • Common Criteria (CC)
IT Audit Methodologies - URLs • CobiT: www.isaca.org • BS7799: www.bsi.org.uk/disc/ • BSI: www.bsi.bund.de/gshb/english/menue.htm • ITSEC: www.itsec.gov.uk • CC: csrc.nist.gov/cc/
Main Areas of Use • IT Audits • Risk Analysis • Health Checks (Security Benchmarking) • Security Concepts • Security Manuals / Handbooks
Security Definition • Confidentiality • Integrity • Correctness • Completeness • Availability
CobiT • Governance, Control & Audit for IT • Developed by ISACA • Releases • CobiT 1: 1996 • 32 Processes • 271 Control Objectives • CobiT 2: 1998 • 34 Processes • 302 Control Objectives
CobiT - Model for IT Governance • 36 Control models used as basis: • Business control models (e.g. COSO) • IT control models (e.g. DTI‘s CoP) • CobiT control model covers: • Security (Confidentiality, Integrity, Availability) • Fiduciary (Effectiveness, Efficiency, Compliance, Reliability of Information) • IT Resources (Data, Application Systems, Technology, Facilities, People)
CobiT - Structure • 4 Domains • PO - Planning & Organisation • 11 processes (high-level control objectives) • AI - Acquisition & Implementation • 6 processes (high-level control objectives) • DS - Delivery & Support • 13 processes (high-level control objectives) • M - Monitoring • 4 processes (high-level control objectives)
PO - Planning and Organisation • PO 1 Define a Strategic IT Plan • PO 2 Define the Information Architecture • PO 3 Determine the Technological Direction • PO 4 Define the IT Organisation and Relationships • PO 5 Manage the IT Investment • PO 6 Communicate Management Aims and Direction • PO 7 Manage Human Resources • PO 8 Ensure Compliance with External Requirements • PO 9 Assess Risks • PO 10 Manage Projects • PO 11 Manage Quality
AI - Acquisition and Implementation • AI 1 Identify Solutions • AI 2 Acquire and Maintain Application Software • AI 3 Acquire and Maintain Technology Architecture • AI 4 Develop and Maintain IT Procedures • AI 5 Install and Accredit Systems • AI 6 Manage Changes
DS - Delivery and Support • DS 1 Define Service Levels • DS 2 Manage Third-Party Services • DS 3 Manage Performance and Capacity • DS 4 Ensure Continuous Service • DS 5 Ensure Systems Security • DS 6 Identify and Attribute Costs • DS 7 Educate and Train Users • DS 8 Assist and Advise IT Customers • DS 9 Manage the Configuration • DS 10 Manage Problems and Incidents • DS 11 Manage Data • DS 12 Manage Facilities • DS 13 Manage Operations
M - Monitoring • M 1 Monitor the Processes • M 2 Assess Internal Control Adequacy • M 3 Obtain Independent Assurance • M 4 Provide for Independent Audit
Information Criteria Effectiveness Efficiency Confidentiality Integrity Availability Compliance Reliability IT Resources People Applications Technology Facilities Data CobiT - IT Process Matrix IT Processes
CobiT - Summary • Mainly used for IT audits, incl. security aspects • No detailed evaluation methodology described • Developed by international organisation (ISACA) • Up-to-date: Version 2 released in 1998 • Only high-level control objectives described • Detailed IT control measures are not documented • Not very user friendly - learning curve! • Evaluation results not shown in graphic form
CobiT - Summary • May be used for self assessments • Useful aid in implementing IT control systems • No suitable basis to write security handbooks • CobiT package from ISACA: $ 100.-- • 3 parts freely downloadable from ISACA site • Software available from Methodware Ltd., NZ (www.methodware.co.nz) • CobiT Advisor 2nd edition: US$ 600.--
BS 7799 - CoP • Code of Practice for Inform. Security Manag. • Developed by UK DTI, BSI: British Standard • Releases • CoP: 1993 • BS 7799: Part 1: 1995 • BS 7799: Part 2: 1998 • Certification & Accreditation scheme (c:cure)
BS 7799 - Security Baseline Controls • 10 control categories • 32 control groups • 109 security controls • 10 security key controls
BS 7799 - Control Categories • Information security policy • Security organisation • Assets classification & control • Personnel security • Physical & environmental security • Computer & network management
BS 7799 - Control Categories • System access control • Systems development & maintenance • Business continuity planning • Compliance
BS7799 - 10 Key Controls • Information security policy document • Allocation of information security responsibilities • Information security education and training • Reporting of security incidents • Virus controls
BS7799 - 10 Key Controls • Business continuity planning process • Control of proprietary software copying • Safeguarding of organizational records • Data protection • Compliance with security policy
BS7799 - Summary • Main use: Security Concepts & Health Checks • No evaluation methodology described • British Standard, developed by UK DTI • Certification scheme in place (c:cure) • BS7799, Part1, 1995 is being revised in 1999 • Lists 109 ready-to-use security controls • No detailed security measures described • Very user friendly - easy to learn
BS7799 - Summary • Evaluation results not shown in graphic form • May be used for self assessments • BS7799, Part1: £ 94.-- • BS7799, Part2: £ 36.-- • BSI Electronic book of Part 1: £ 190.-- + VAT • Several BS7799 c:cure publications from BSI • CoP-iT software from SMH, UK: £349+VAT (www.smhplc.com)
BSI (Bundesamt für Sicherheit in der Informationstechnik) • IT Baseline Protection Manual(IT- Grundschutzhandbuch ) • Developed by German BSI (GISA: German Information Security Agency) • Releases: • IT security manual: 1992 • IT baseline protection manual: 1995 • New versions (paper and CD-ROM): each year
BSI - Approach • Used to determine IT security measures for medium-level protection requirements • Straight forward approach since detailed risk analysis is not performed • Based on generic & platform specific security requirements detailed protection measures are constructed using given building blocks • List of assembled security measures may be used to establish or enhance baseline protection
BSI - Structure • IT security measures • 7 areas • 34 modules (building blocks) • Safeguards catalogue • 6 categories of security measures • Threats catalogue • 5 categories of threats
BSI - Security Measures (Modules) • Protection for generic components • Infrastructure • Non-networked systems • LANs • Data transfer systems • Telecommunications • Other IT components
BSI - Generic Components • 3.1 Organisation • 3.2 Personnel • 3.3 Contingency Planning • 3.4 Data Protection
BSI - Infrastructure • 4.1 Buildings • 4.2 Cabling • 4.3 Rooms • 4.3.1 Office • 4.3.2 Server Room • 4.3.3 Storage Media Archives • 4.3.4 Technical Infrastructure Room • 4.4 Protective cabinets • 4.5 Home working place
BSI - Non-Networked Systems • 5.1 DOS PC (Single User) • 5.2 UNIX System • 5.3 Laptop • 5.4 DOS PC (multiuser) • 5.5 Non-networked Windows NT computer • 5.6 PC with Windows 95 • 5.99 Stand-alone IT systems
BSI - LANs • 6.1 Server-Based Network • 6.2 Networked Unix Systems • 6.3 Peer-to-Peer Network • 6.4 Windows NT network • 6.5 Novell Netware 3.x • 6.6 Novell Netware version 4.x • 6.7 Heterogeneous networks
BSI - Data Transfer Systems • 7.1 Data Carrier Exchange • 7.2 Modem • 7.3 Firewall • 7.4 E-mail
BSI - Telecommunications • 8.1 Telecommunication system • 8.2 Fax Machine • 8.3 Telephone Answering Machine • 8.4 LAN integration of an IT system via ISDN
BSI - Other IT Components • 9.1 Standard Software • 9.2 Databases • 9.3 Telecommuting
BSI - Module „Data Protection“ (3.4) • Threats - Technical failure: • T 4.13 Loss of stored data • Security Measures - Contingency planning: • S 6.36 Stipulating a minimum data protection concept • S 6.37 Documenting data protection procedures • S 6.33 Development of a data protection concept (optional) • S 6.34 Determining the factors influencing data protection (optional) • S 6.35 Stipulating data protection procedures (optional) • S 6.41 Training data reconstruction • Security Measures - Organisation: • S 2.41 Employees' commitment to data protection • S 2.137 Procurement of a suitable data backup system
BSI - Safeguards (420 safeguards) • S1 - Infrastructure ( 45 safeguards) • S2 - Organisation (153 safeguards) • S3 - Personnel ( 22 safeguards) • S4 - Hardware & Software ( 83 safeguards) • S5 - Communications ( 62 safeguards) • S6 - Contingency Planning ( 55 safeguards)
BSI - S1-Infrastructure (45 safeguards) • S 1.7 Hand-held fire extinguishers • S 1.10 Use of safety doors • S 1.17 Entrance control service • S 1.18 Intruder and fire detection devices • S 1.27 Air conditioning • S 1.28 Local uninterruptible power supply [UPS] • S 1.36 Safekeeping of data carriers before and after dispatch
BSI - Security Threats (209 threats) • T1 - Force Majeure (10 threats) • T2 - Organisational Shortcomings (58 threats) • T3 - Human Errors (31 threats) • T4 - Technical Failure (32 threats) • T5 - Deliberate acts (78 threats)
BSI - T3-Human Errors (31 threats) • T 3.1 Loss of data confidentiality/integrity as a result of IT user error • T 3.3 Non-compliance with IT security measures • T 3.6 Threat posed by cleaning staff or outside staff • T 3.9 Incorrect management of the IT system • T 3.12 Loss of storage media during transfer • T 3.16 Incorrect administration of site and data access rights • T 3.24 Inadvertent manipulation of data • T 3.25 Negligent deletion of objects
BSI - Summary • Main use: Security concepts & manuals • No evaluation methodology described • Developed by German BSI (GISA) • Updated version released each year • Lists 209 threats & 420 security measures • 34 modules cover generic & platform specific security requirements
BSI - Summary • User friendly with a lot of security details • Not suitable for security risk analysis • Results of security coverage not shown in graphic form • Manual in HTML format on BSI web server • Manual in Winword format on CD-ROM (first CD free, additional CDs cost DM 50.-- each) • Paper copy of manual: DM 118.-- • Software ‚BSI Tool‘ (only in German): DM 515.--
ITSEC, Common Criteria • ITSEC: IT Security Evaluation Criteria • Developed by UK, Germany, France, Netherl. and based primarily on USA TCSEC (Orange Book) • Releases • ITSEC: 1991 • ITSEM: 1993 (IT Security Evaluation Manual) • UK IT Security Evaluation & Certification scheme: 1994
ITSEC, Common Criteria • Common Criteria (CC) • Developed by USA, EC: based on ITSEC • ISO International Standard • Releases • CC 1.0: 1996 • CC 2.0: 1998 • ISO IS 15408: 1999
ITSEC - Methodology • Based on systematic, documented approach for security evaluations of systems & products • Open ended with regard to defined set of security objectives • ITSEC Functionality classes; e.g. FC-C2 • CC protection profiles • Evaluation steps: • Definition of functionality • Assurance: confidence in functionality
ITSEC - Functionality • Security objectives (Why) • Risk analysis (Threats, Countermeasures) • Security policy • Security enforcing functions (What) • technical & non-technical • Security mechanisms (How) • Evaluation levels
ITSEC - Assurance • Goal: Confidence in functions & mechanisms • Correctness • Construction (development process & environment) • Operation (process & environment) • Effectiveness • Suitability analysis • Strength of mechanism analysis • Vulnerabilities (construction & operation)
CC - Documentation CC Part 3 Assurance Requirements CC Part 2 * Assurance Classes * Assurance Families * Assurance Components * Detailed Requirements * Evaluation Assurance Levels (EAL) Functional Requirements * Functional Classes * Functional Families * Functional Components * Detailed Requirements CC Part 1 Introduction and Model * Introduction to Approach * Terms and Model * Requirements for Protection Profiles (PP) and Security Targets (ST)