Enhancing Security in Ultra-Large Scale Systems Through Domain-Specific Modeling Techniques
10 likes | 145 Vues
This paper addresses trustworthiness challenges in Ultra-Large Scale (ULS) systems by employing a novel Security Quality of Service (QoS) Modeling Language (SQML) and a Data Distribution Service (DQML). By using model-driven engineering, the approach modularizes trustworthiness concerns such as security and resiliency, facilitating fine-grained access control while eliminating runtime inefficiencies. The integration allows for a tailored security framework, enabling better configuration analysis and ensuring QoS compliance during both design and runtime. Ongoing research focuses on enhancing DDS services with robust security specifications.

Enhancing Security in Ultra-Large Scale Systems Through Domain-Specific Modeling Techniques
E N D
Presentation Transcript
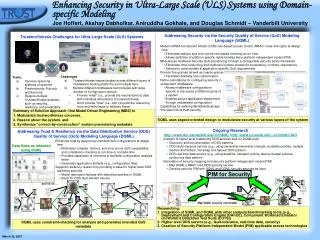
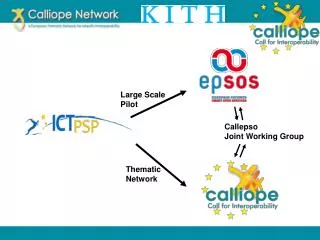
Enhancing Security in Ultra-Large Scale (ULS) Systems using Domain-specific Modeling Durability- Transient Durability- Volatile Durability- Transient Deadline- 10ms Deadline- 10ms Deadline- 20ms Deadline- 15ms Deadline- 10ms Deadline- 10ms Deadline- 20ms Deadline- 10ms Deadline- 15ms Timebased- 5ms Timebased- 5ms Liveliness- Manual By Topic Liveliness- Manual By Topic Liveliness- Automatic Liveliness- Automatic Reliability- Reliable Reliability- Reliable Reliability- Reliable Reliability- Reliable Reliability- Reliable Interface Security QoS National/International Power Grid Conforms to Policy Component Security QoS Domain-Specific Security Policy Constellations of Satellites Homeland Defense Air Traffic Management SQML input DQML input Joe Hoffert, Akshay Dabholkar, Aniruddha Gokhale, and Douglas Schmidt – Vanderbilt University Addressing Security via the Security Quality of Service (QoS) Modeling Language (SQML) Trustworthiness Challenges for Ultra-Large Scale (ULS) Systems • Model CORBA Component Model (CCM) role-based access control (RBAC) rules and rights at design time • Eliminates tedious and error-prone role-based checking at run-time • Allows definition of platform-specific rights families like a platform independent model (PIM) • Modularizes multilevel Security QoS provisioning through a configurable security policy framework • Eliminates time consuming and inefficient runtime checks for consistency, conflicts, redundancy. • Tailored to meet domain & application specific QoS requirements • Provide fine-grained as well as coarse-grained access control and security guarantees • Facilitates flexibility and customization • Challenges: • Trustworthiness issues tangled across different layers of middleware hosting platforms and multiple tiers • Multiple different middleware technologies with large number of configuration options • Provide "what" (i.e., provide the mechanisms to deal with individual dimensions of trustworthiness) • Don’t provide "how" (i.e., don’t provide the reasoning tools and techniques to address these) • Traits: • Services spanning systems of systems • Predominantly Pub-sub architectures • Require multiple Trustworthiness qualities, such as security, resiliency, and predictably • Define annotations for configuring security in component middleware • Allows middleware configurations specific to the needs of different parts of a system • Enables secure application deployment through middleware configuration • Capabilities for defining Workflow/Business Process/Critical Path security • Summary of Solution Approach: Use Model Driven Engineering (MDE) to • Modularize trustworthiness concerns, • Reason about the system, and • Synthesize “correct-by-construction” system provisioning metadata SQML uses aspect-oriented design to modularize security at various layers of the system Ongoing Research http://www.dre.vanderbilt.edu/CoSMIC, http://www.cs.wustl.edu/~schmidt/CIAO Addressing Trust & Resiliency via the Data Distribution Service (DDS) Quality of Service (QoS) Modeling Language (DQML) • Creation of higher level trustworthy DDS services built on DQML work • Discovery and documentation of DDS patterns • DDS fault-tolerance service (e.g., using ownership/ownership strength, durability policies, multiple readers and writers, hot-swap and failover DDS pattern) • DDS real-time data service (e.g., using deadline, transport priority, latency budget policies, continuous data pattern) • Generation of security mapping and security platform independent model (PIM) • Map SQML’s RBAC onto DDS security service • Develop security PIM with SQML and DQML security services as input • Enhances trust by supporting intended QoS configurations at design time • Eliminates complex, tedious, and error-prone QoS compatibility and consistency checking at run-time or compile-time • Provides separation of concerns to facilitate configuration analysis better • Generates application artifacts (e.g., configuration files) • Supports resiliency research by providing a base for higher level DDS resiliency services • Model redundant replicas with desired properties in DQML • Basis for DDS fault-tolerant service Data flows as intended using DQML PIM for Security and so on … DataReader 2 DataReader 2 DataWriter 2 DataWriter 3 Map SQML security onto DQML DataReader 1 Topic A DataWriter 1 • Researching: • Integration of SQML and DQML with other analysis/benchmarking tools (e.g., Deployment and Configuration Engine (DAnCE), Component Workload Emulator (CoWorkEr) Utilization Test Suite (CUTS)) • Higher level DDS service (e.g., fault-tolerance, real-time data, security) • Creation of Security Platform Independent Model (PIM) applicable across technologies Topic A DataWriter 1 Topic B DataReader 3 DataWriter 4 DataReader 1 DQML uses constraint-checking for analysis and generates intended QoS metadata March 20, 2007