ECE579S Computer & Network Security
ECE579S Computer & Network Security. Professor Richard A. Stanley, P.E. Overview of Tonight’s Class. Administration Is computer security a problem, or just an interesting topic? What is different between computer security and network security? Computer security objectives and approaches.


ECE579S Computer & Network Security
E N D
Presentation Transcript
ECE579S Computer & Network Security Professor Richard A. Stanley, P.E. WPI
Overview of Tonight’s Class • Administration • Is computer security a problem, or just an interesting topic? • What is different between computer security and network security? • Computer security objectives and approaches WPI
Organizational Details • Prof. Stanley contact information • Office: Atwater-Kent 303, but rarely there • Hours: by appointment, preferably after class • Phone: (508) 269-6482 • Email: rstanley@ece.wpi.edu WPI
Administrivia • Class will normally meet 8:00 AM – 1:00 PM every Friday here. Please be on time. • We will hold 8 classes; cancellations will be announced in advance (except weather) • Breaks as needed • If class is cancelled for bad weather, you should receive notice. Double-check with ECE Dept. (5231) or with me if in doubt. WPI
Recall • We need to set up a way for notification of cancelled/late classes • Please put the following information on the sheet going around: • Name • Email • Telephone • Volunteer to be at the top of the list? WPI
Course Text • Computer Security Handbook, 5th Edition, by Bosworth, et al. ISBN is 978-0471716525. To be published 09 Feb 09 by Wiley. • Additional material will be in the form of handouts WPI
Course Web Page • http://ece.wpi.edu//courses/ee579sw/ECE579S/ • Slides will be posted to the page before class, barring any unfortunate problems WPI
Policies • Homework is due at the class following the one in which it is assigned. It will be accepted--with a one grade penalty--up to the second class after that in which it is assigned, but not after that, except in truly emergency situations. By definition, emergencies do not occur regularly. • There is a difference between working in teams and submitting the same work. If work is a team product, it must be clearly labeled as such. WPI
Elements of the Course • Assignments:There will be weekly assignments, which will be graded • Presentation:At the end of the course, student teams will present a report prepared on a cryptography-related subject. The presentation should be well-prepared and should give an overview of a special topic in cryptography (e.g. eCash, wireless security, SSL, biometric authentication systems etc.). • Examinations:There will be a two written examinations that will cover all topics discussed in class. The questions will range from mild to hard. WPI
Research Projects • Teams of 3-5 individuals per project • Research an information assurance-related topic • Prepare a report on the research • Present findings • Note: a presentation is not the report copied into PowerPoint WPI
Grading • Grade components • Course exams (35%) • Homework (20%) • Class participation (10%) • Course project (35%) WPI
My Peculiarities • I am not a word-counter. When given, word counts are for general guidance only. • Bad news doesn’t improve with age. If there are problems, let’s deal with them as soon as they arise. • Expect to find ties to historical events in class – not a bad idea to use those for hints as to how some problems develop and expand. WPI
Getting to Know You • My interest and experience in this area • Your interests and expertise in this area • Cryptography? • Networking? • Where we might go with this course • What you would like from the course WPI
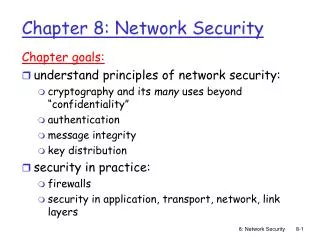
Computer security involves preventing, detecting, and responding to unauthorized actions on a computer system. Network security means the same thing for a group of networked computers Information Assurance covers all the things we do to protect information from unauthorized disclosure and exploitation WPI
Chicken vs. Egg? To understand network security, you must first understand computer security. There is no “easy” way around this. To practice information assurance, you need to know both computer and network security, as well as quite a lot of other topics, which we will cover. We are going to find that this subject crosses many boundaries of skills and “jurisdiction.” This can be both an opportunity and a curse. WPI
One View Network Security Computer Security WWW Security IA WPI
Computer Security: What’s the Big Deal? • Not a new problem • Not just a creation of the press • Not just for rocket scientists • As professionals, failure to understand and implement appropriate security can come back to haunt you in terms of liability and reputation WPI
Points to Ponder • Majority of businesses reported attacks against their networks in 2007 • Almost 20% of these were targeted • Average financial losses over $350,000 per organization, highest in last five years • Financial fraud displaced viruses as the first place problem Source: "Issues and Trends: 2007 CSI/FBI Computer Crime and Security Survey" WPI
Recent Events • WikiLeaks • Is this a computer security problem? • Denial of Service attacks • Both from WikiLeaks supporters and totally unrelated • …and? WPI
Virtual Warfare “Cyberspace is another domain in which the U.S. military may face rapidly growing risk. Information technology (IT) permeates every aspect of its operations, from logistics and command and control to targeting and guidance. As the dependence on IT has grown, so, too, has vulnerability to disruptions, especially dirsuptions of battle networks linking U.S. forces.” Andrew J. Krepinevich, Jr, “The Pentagon’s Wasting Assets,” Foreign Affairs Vol 88, No. 4 (July/August 2009), pg. 25. WPI
It Isn’t Getting Better • Security surveys show a clear trend in security problems: UPWARDS • Nature of attacks constantly changing • Evidence of nation-state participation • Who among you has not seen or heard at least one computer security news story in the past month? WPI
An Object Lesson Willie Sutton, 1901-1980. Bank Robber. Q: “Why do you rob banks, Willie?” A: “Because that’s where the money is!” This quote is probably the best-known criminal quote around. One problem: Willie never said it. BUT... He said “I probably would have said it if anyone had asked me.” WPI
Where’s The Money? • Historically, money was something held to have intrinsic value (e.g., gold, silver) • Paper money, until recently, was merely a promise to pay in gold or silver • So, money really was in the banks • Money today is merely a unit of information • ... And it is kept in computers! WPI
The “Willie Factor” • Computer crime exists because computers are the repositories of things of value • Money • This is a common target in industrial attacks • Information that is valuable or can be made so • This is especially true in government networks, most particularly in defense-related networks • Thieves look for low-hanging fruit WPI
A Dilemma • Security is something most users want, but that most know little about • Security gets in the way of using the computer system • The tighter the security, the harder the system is to use, and the more likely it is that the users will bypass security measures WPI
The Totally Secure System • Is relatively simple to build • Is useless for any practical purposes Our job is to learn how to design computer systems to provide the necessary level of security without going overboard. WPI
Why Isn’t This Topic More Theoretical? In theory, there is no difference between theory and practice. In practice, there is. Yogi Berra WPI
Why Is A Proof Elusive? • A secure system must be secure under all conditions of operation • This, in turn, demands proof that there is no condition under which it could operate that is insecure, i.e. the negative proposition. • But, formal logic teaches us it is impossible to prove a negative • Q.E.D. WPI
That Said... • We will define a secure computer • We will learn how to create a secure computer • If it is useless, why? • If it can’t exist, we will never know how close we are to achieving security • It is a goal towards which we must work WPI
Consider the Automobile • A perfectly safe automobile does not exist, and cannot exist • However, we still strive to build safer autos • This is a legitimate engineering pursuit • It is socially irresponsible to do otherwise • Much of the efforts are based on approaching an unachievable goal WPI
Responsibilities • Customers expect “reasonably secure” handling of their sensitive data • The Devil is in the details • What is “reasonable?” • What is “secure?” • What data is “sensitive?” • When is it your responsibility? WPI
What’s the Problem? • Financial liability • Due diligence • Simple negligence • Gross negligence • Goodwill • One bad press release cancels 1000 attaboys This is a “you bet your business” issue WPI
A Curious Property of Information • Information is the only thing that can be stolen and still leave the owner in possession of it • This poses some serious problems, which the course will address WPI
Security Aspects • Confidentiality • Integrity • Availability • Accountability • Nonrepudiation • Risk management • Reliability and safety Security is a multidisciplinary problem WPI
Problem is Multidisciplinary • Engineering • Computer science • Sociology • Economics • Law and ethics • Management • and ... WPI
Role of Technology • Technology is a useful tool, not a panacea. • A clear policy, evenly enforced, is the most critical element of success. • Don’t ignore the fundamentals. • Many computers have been compromised by not revoking a former employee’s password • Most of the threat comes from within • The problem is not just maliciousness WPI
Security Objectives Integrity A – I - C Availability Confidentiality Protect, detect and recover from insecurities WPI
Data vs. Information • Data represents information • Information is the interpretation of data This is not as obvious as it appears on the surface! WPI
So What? • Protecting the data may not protect the information • It is possible to create information from a wide variety of data sources • e.g. Wehrmacht order of battle pre-1939 • The problem is more complex than just putting an armed guard at the door WPI
One View:Security = Asset protection Risk Analysis Protect Detect Correct Manage WPI
Another View:Focus of Control Applications User (Subject) Resource (Object) Policy Protection Hardware Should protection focus on data, operations, or users? WPI
Man-Machine Scale Applications Services OS OS kernel Hardware In which layer(s) should security be implemented? WPI
Controls • Centralized • Simple to conceive and implement • Bottleneck • Decentralized • May be more efficient • Difficult to implement and maintain Where to put security tasks and enforcement? WPI