Automatic Teller Machines
E N D
Presentation Transcript
Automatic Teller Machines Chapter 10 ATM 1
Automatic Teller Machines • “…one of the most influential technological innovations of the 20th century” • Began in 1968, more than 500,000 today • One of the first commercial use of crypto (block ciphers), tamper resistant hardware, security protocols, etc. • The “killer app” for commercial crypto Chapter 10 ATM 2
ATMs • An interesting case study • What was done correctly • What was done incorrectly Chapter 10 ATM 3
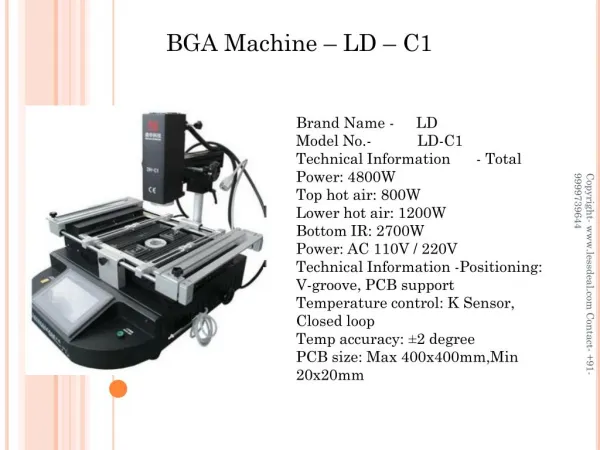
ATM Security Module • Security module implemented in tamper-resistant hardware • IBM 4758 crypto processor • Security module is at bank • All crypto computations done in security module, such as PIN verification Chapter 10 ATM 4
ATM Security Module • IBM PIN generation • Acct number N on magnetic stripe • PIN key K (in tamper-resistant hardware) • “Natural PIN” is F(E(N, K)), where encryption E is DES, and F is a function • PIN = natural PIN + offset (so customers can choose their own PIN) • Note: PIN verification relies on N and secret K, and is done in security module Chapter 10 ATM 5
Account number: PIN key K: DES encrypt E(N,K): Decimalize: Natural PIN: Offset: Customer PIN: 8807012345691715 FEFEFEFEFEFEFEFE A2CE126C69AEC82D 0224126269042823 0224 6565 6789 IBM PIN Gen Example Chapter 10 ATM 6
More ATM Security • PIN encrypted with “terminal master key” and sent to security module • ‘Dual controls” --- terminal master key entered in 2 parts (2 people) • PIN “translation” (from one ATM network to another) done in security module Chapter 10 ATM 7
Problems • Early on, encryption done in software • Not feasible for all pairs of banks to share keys, so KDC used (VISA) • Large number of trans, so corners cut • “Optimization is the process of taking something that works and replacing it with something that doesn’t quite, but is cheaper” • Most ATMs use 56-bit DES Chapter 10 ATM 8
What goes wrong • ATM system designed to stop sophisticated attacks • In practice, the real issues are • Processing errors --- e.g., computer crashes • Only 0.001% probability, but 5 billion ATM trans • Card theft from mail • Fraud by bank staff • Laptop inside ATM to record PIN’s • Key for test system used for real system Chapter 10 ATM 9
Unexpected Attacks • Shoulder surfing to get PIN, copy acct number from receipt • One system --- telephone calling card, ATM thought previous card inserted • One system --- output 10 bills when 14-digit test sequence entered • One bank issued same PIN to everybody • Fake ATM to collect PINs • Steal the ATM (camera is inside ATM) Chapter 10 ATM 10
ATMs • Biggest mistake in design of ATM system: “… worried to much about criminals being clever instead of worrying about customers and banks being stupid” Chapter 10 ATM 11
ATM legal issues • In US, banks carry risk of ATM technology • must refund most disputed transaction • costs average bank $15K/year in fraud • In much of Europe, customer bore cost • Banks claimed ATMs infallible • John Munden case • British policeman, found his acct $700 short • Bank: no bugs in code since written in assembler • Munden convicted and fired • Overturned on appeal: bank would not release its code Chapter 10 ATM 12
ATM legal issues • If Munden case had occurred in California, “he would have won enormous punitive damages” • Lessons • Non-repudiation is critical --- camera in ATM would have solved Munden case immediately • In general, security system must be able to withstand examination by hostile experts Chapter 10 ATM 13