Verifying Cipher Key Using Shift Modulo Technique
20 likes | 144 Vues
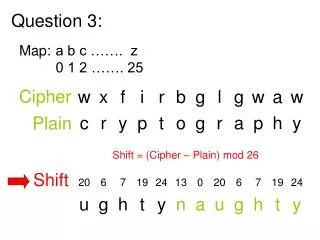
This document explores the process of verifying a cipher key through a shift-modulus technique. By analyzing the relationship between the deciphered text and a presumed key, "naughty," we attempt a decryption methodology that shifts the plain text to Position 0. Position 0 serves as the starting point for any key. The confirmation that "naughty" commences at this position solidifies its validity as the encryption key. This provides insight into cryptographic methods and their application in validating hypotheses on cipher keys.

Verifying Cipher Key Using Shift Modulo Technique
E N D
Presentation Transcript
Shift Question 3: Map: a b c ……. z 0 1 2 ……. 25 Cipher Plain Shift = (Cipher – Plain) mod 26
We guess that the Key is: naughty • To verify that “naughty” is indeed the Key, we attempt to shift the decrypted text to Position 0. • Position 0 is where a Key should start. • We note that “naughty” starts at Position 0. • Hence “naughty” is the Key.