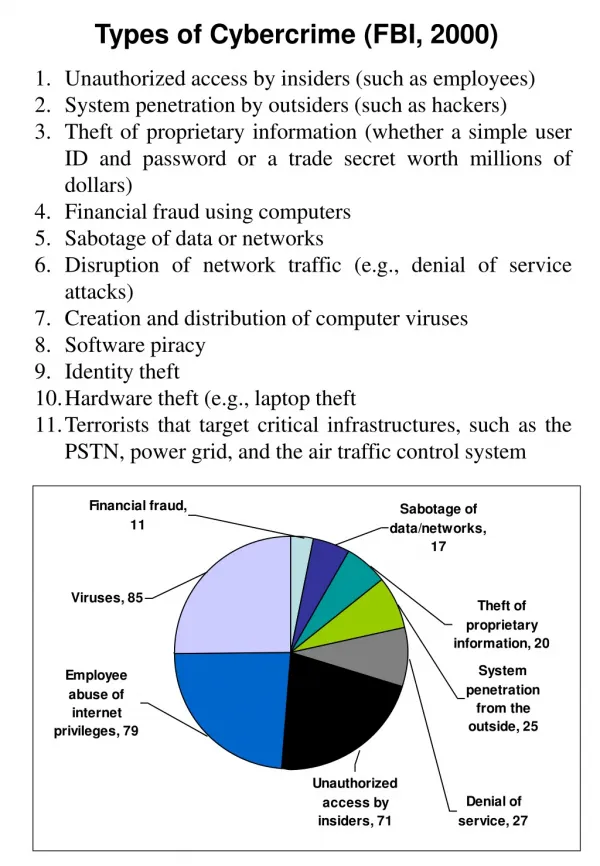
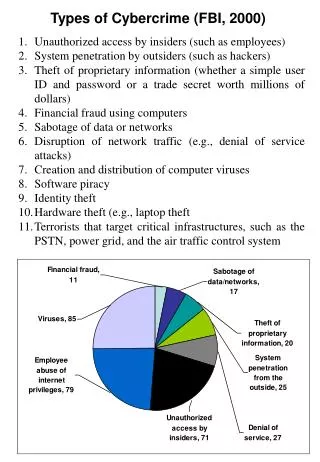
Types of Cybercrime (FBI, 2000)
Types of Cybercrime (FBI, 2000). Unauthorized access by insiders (such as employees) System penetration by outsiders (such as hackers) Theft of proprietary information (whether a simple user ID and password or a trade secret worth millions of dollars) Financial fraud using computers

Types of Cybercrime (FBI, 2000)
E N D
Presentation Transcript
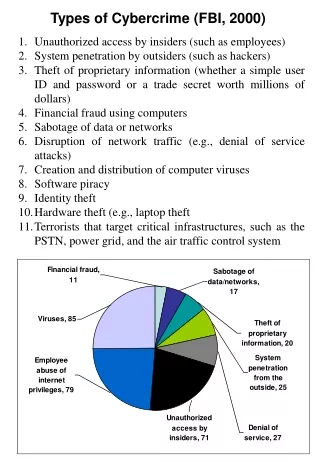
Types of Cybercrime (FBI, 2000) • Unauthorized access by insiders (such as employees) • System penetration by outsiders (such as hackers) • Theft of proprietary information (whether a simple user ID and password or a trade secret worth millions of dollars) • Financial fraud using computers • Sabotage of data or networks • Disruption of network traffic (e.g., denial of service attacks) • Creation and distribution of computer viruses • Software piracy • Identity theft • Hardware theft (e.g., laptop theft • Terrorists that target critical infrastructures, such as the PSTN, power grid, and the air traffic control system
Financial Loss (FBI, 2004) How to Prevent Cyber Crime
Computer used to commit a crime Child porn, threatening email, assuming someone’s identity, sexual harassment, defamation, spam, phishing Computer as a target of a crime Viruses, worms, industrial espionage, software piracy, hacking Top Cyber Crimes that Attack Business (www.suzannemello.com) Spam Viruses/Worms Industrial Espionage and Hackers Wi-Fi High Jacking Cyber Crime – “Is the Internet the new “Wild Wild West?” Computer Forensics • What is it? • an autopsy of a computer or network to uncover digital evidence of a crime • Evidence must be preserved and hold up in a court of law
What is cyberethics? Ethics: a set of principals of right conduct. The American Heritage Dictionary 2000Ethics:Motivation based on ideas of right and wrong . Wordnet 1.6 Princeton University 1997 • General conception of right/wrong that transcend religion and law • (Webster’s Dictionary, 2001) • Ethical or Unethical? • A student downloads a sexually explicit picture from the Internet on a computer in the school library. Other students are able to see the picture • A student finds the teacher’s password to the school’s information system and uses it to change his grades and vi the grades of other students. • A student uses the copy and paste commands to place large parts of an electronic article into an assigned paper. She turns the paper in as her own work • A student makes a copy of a software program borrowed from another student to use on his computer at home. • A student downloads a graphic file from the web to place on his own webpage. However, he does provide a link to the author’s site. • A student uses another student’s project website as a guideline. • A student copies a previous published story in his own handwriting and submits it as his own work. (Sherri Shade)
What is cyberethics? • The study of moral, legal, ethical issues involving the use of use of information and communication technologies • (Tavani di dalam Yu-Che Chen- Iowa State University) • Cyber Ethics: • application of ethics into the online environment (Ethics Connection, 2000) Computer ethics is the analysis of the nature andsocial impact of computer technology and the corresponding formulation and justification of policies for the ethical use of such technology (Gordana Dodig-Crnkovic, 2004) Codes of Conduct • Association of Computing Machinery (ACM) • American Information Technology Professionals • Software Engineering • IEEE