Computing Equilibria in Security Games via Linear Integer Programming
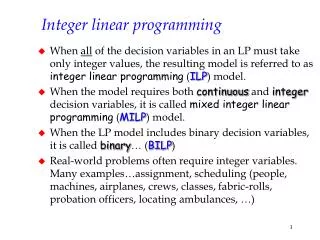
This work presents methods for computing equilibria in security games utilizing linear integer programming techniques. We explore mixed strategies in a Stackelberg framework, where a defender commits to a strategy, and the attacker responds optimally. Several formulations are proposed, including the handling of binary and continuous variables along with implications. We apply innovative techniques such as the Either-Or Trick to simplify constraints. Our Mixed Integer Programming (MIP) approach offers a straightforward solution to achieve a Stackelberg-Nash equilibrium, ultimately enhancing strategic security game deployment.


Computing Equilibria in Security Games via Linear Integer Programming
E N D
Presentation Transcript
Computing equilibria of security games using linear integer programming DimaKorzhyk dima@cs.duke.edu
Problem Description • Targets t • Utilities • Resources nd, na
Mixed strategies • Defender strategy: probability of defending target t is dt, s.t. • Attacker strategy: similarly, the probability of attacking t is at, s.t.
Stackelberg strategy • The defender commits to a mixed strategy d • The attacker observes d and plays a best response a • Note that the attacker’s best response doesn’t need to be randomized, so we can assume a is binary
Trick – fixing an implication with a binary right-hand side Suppose b is binary and we have implication if g(x) > 0 then b=1 Fix this as follows: b >= g(x) / M Here M is a sufficiently large number
Fixed conditions We can rewrite the implication As
Fixing the objective Note that the objective contains a product of two variables at and dt
Trick – fixing a product of a binary and a continuous variable in the objective Suppose the objective is Maximize bx Where b is binary, and x>=0 is a continuous variable. Replace this with Maximize v v <= x v <= bM Where M is a sufficiently large number
Nash equilibrium Find a pair of mixed strategies d,a such that both players are best-responding. d,a are not binary.
Trick – fixing the implications [aimms.com] Suppose we have an implication IF [g(x) > 0] THEN [h(x) > 0] This is equivalent to [g(x) <= 0] OR [h(x) > 0] Now, we can use the either-or trick (next slide)
Either-Or Trick Suppose we have a constraint [g(x)>0] OR [h(x)>0] We need to change this to AND Replace with the following: g(x) + M b > 0 h(x) + M (1-b) > 0 where M is a sufficiently large number b is binary
Conclusion • NE MIP is simpler than a specialized algorithm, but may take longer to execute • A benefit is that we can combine the two MIPs in this presentation to find a defender strategy that is both a Stackelberg and a Nash strategy
Thank you! I thank Vince Conitzer, Ron Parr for detailed discussions.
References Security games (with a single attacker resource) were introduced in: Christopher Kiekintveld, Manish Jain, Jason Tsai, James Pita, Fernando Ordóñez, and MilindTambe. Computing Optimal Randomized Resource Allocations for Massive Security Games. AAMAS-2009. Computing a Stackelberg strategy in a security game with multiple attacker resources s is NP-hard: Zhengyu Yin, DmytroKorzhyk, Christopher Kiekintveld, Vincent Conitzer, and MilindTambe. Stackelbergvs. Nash in security games: interchangeability, equivalence, and uniqueness. AAMAS-2010. Computing a Nash equilibrium in security games with multiple attacker resources can be done in polynomial time. The algorithm by DmytroKorzhyk, Vincent Conitzer, Ronald Parr is currently unpublished and is under submission. Some of the integer programming tricks in this presentation were taken from AIMMS Modeling Guide http://www.aimms.com/aimms/download/manuals/aimms3om_integerprogrammingtricks.pdf