Using Crypto in RDBMS
E N D
Presentation Transcript
Using Crypto in RDBMS PgDay.ru – 2016 Saint-Petersburg July 7-8, 2016 Dmitry Belyavskiy, Technical Centre of Internet
You have data! 2 ways of attack – 2 ways of protection: • The attacker may steal data • The attacker may modify data You want to protect data Rule 1: Do not invent your own crypto!
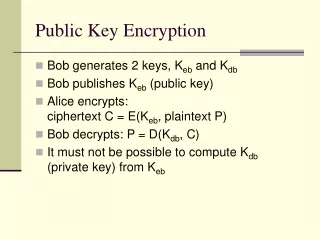
Crypto ops: Classification Main crypto primitives: • Hash (message digest) • Cipher • Digital signature • MAC • Helper algorithms: KDF, PRF… Datastealing Data modifying
Hash • Any data => fixed-length data • Non-revertible • Hard to find pre-image • Hard to find collision • Algorithms: MD5, SHA1, SHA2, SHA3… • Length: 128-512 bits
Ciphers • Any data => Any data • Revertible • Algorithms: AES, Camellia, 3DES, ChaCha… • Many modes: • ECB: the same input => the same output • All other: IV to make result different Source: https://blog.filippo.io/the-ecb-penguin/
Passwords: Hash vs Cipher Hash • Same input => same output • Rainbow tables • Need extra data to make values unique • HMAC = HASH (salt, data). • Salt to be stored in DB • Bcrypt/scrypt Cipher • Where is my key? • Password length is known (padding helps) => Dictionary attack
Digital signature • Any data => (hash) => (private key) => signature • Algorithms: ECDSA, RSA, Ed25519… • Data is untouched • Signature may be stored aside • Signature keys expire from time to time
What do we protect? • Threat model • Protect traffic to database? Enable TLS! • Protect data in DB? Think about encrypted FS. • PostgreSQL: patches to encipher the DB itself. • Long ago: http://archives.postgresql.org/pgsql-hackers/2011-10/msg01213.php • New: http://www.cybertec.at/2016/06/postgresql-instance-level-encryption/ • Some parts of data? • Where is the key? • No search. • No ORDER BY. At least now… • Encryption for the DB owner – S/MIME, CMS… • Replication && backups! • http://evol-monkey.blogspot.ru/2015/10/postgresql-94-streaming-replication.html
Crypto implementation in PostgreSQL • Pgcryptohttps://www.postgresql.org/docs/current/static/pgcrypto.html • Can use OpenSSL or not • PGP operations • crypt/gen_salt for storing passwords • Low-level operations • Some low-level crypto primitives (MD5, SHA1) are built-in.
To be done • Property-preserving encryption • Homomorphic encryption • Format-preserving encryption
Property-preserving encryption A B => Encrypt(A) Encrypt(B) • Description: • https://css.csail.mit.edu/cryptdb/ • http://research.microsoft.com/en-us/projects/cipherbase/ • Analysis: • http://bristolcrypto.blogspot.co.at/2015/10/inference-attacks-on-property.html • http://outsourcedbits.org/2015/09/07/attacking-encrypted-database-systems/
Homomorphic encryption Encrypt (AVG(A, B, C…)) = AVG(Encrypt(A), Encrypt(B), Encrypt(C)…) • Privacy to rule them all! • http://research.microsoft.com/apps/pubs/default.aspx?id=148825 • http://research.microsoft.com/apps/pubs/default.aspx?id=258435 • http://research.microsoft.com/pubs/258435/ManualHEv2.pdf
Format-preserving encryption Is the phone, SSN, or credit card encrypted or not? No changes to database schema! • NIST:Recommendation for Block Cipher Modes of Operation: Methods for Format-Preserving Encryptionhttp://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-38G.pdfhttps://app.box.com/shared/static/tvc6cgfyswdocghv3cnffu32w3jndiu9.pdf
Last but not least • PCI-DSS Compliance • The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes https://wiki.postgresql.org/images/2/24/Achieving_PCI_Compliace_PgConfNYC2014.pdf
Questions? beldmit@tcinet.ru