Differentiated Services Architecture: Enhancing Internet Traffic Management
320 likes | 427 Vues
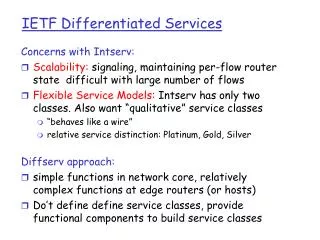
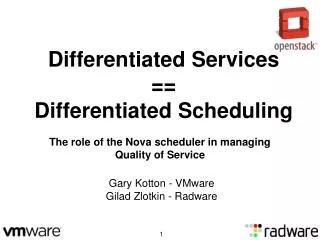
This presentation explores the Differentiated Services Architecture (DSA) developed for the Internet, articulating its necessity in managing distinct service types amid congestion. With a focus on the implementation challenges and mechanisms such as Assured and Premium services, the architecture employs two-bit marking in packet headers to prioritize traffic effectively. Through addressing issues of bandwidth allocation, queuing, and ensuring reliable service performance, the presentation underscores the principles underlying DSA and the role of Bandwidth Brokers in managing marked traffic allocations.

Differentiated Services Architecture: Enhancing Internet Traffic Management
E N D
Presentation Transcript
A Differentiated Services Architecture for the Internet References - K. Nichols, V. Jacobson, L. Zhang - D. Clark, J. Wroclawski Presented by Liping Zhang
Overview • Introduction • Two different service types: implementation and problems • Two-bit differentiated services architecture • Problems with end-end bandwidth allocation based on level of marked traffic • Discussion
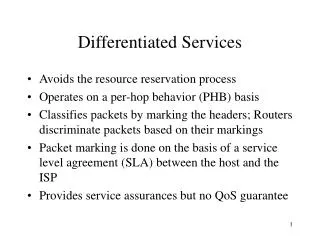
Introduction • Why do we need differentiated services? • Different users • Different applications • Service allocation • For example, one goal of assured service is to allocate the bandwidth of the Internet to different users in a controlled way during periods of congestion
How to describe a service • What is provided to the customer • E.g., 1 Mbps, continuously available • To where is this service provided • A single destination • A group • All nodes on local provider • Everywhere • Level of assurance provided to service • What level of performance uncertainty can user tolerate
Two distinct service types • Assured service • D. Clark • Premium service • V. Jacobson
Assured service • Provide different levels of best-effort service at times of network congestion • Expected capacity • “In” packets unlikely to be dropped • “Out” packets - no assurance • Queuing • Best effort
Mechanism for assured service Counter Counter Out- and in- dropper First-hop Host Marking packets according to the service profile RIO scheme, packets are treated preferentially
RIO algorithm • RED - Random Early Detection • Packets dropped with low but increasing probability as queue grows; instead of waiting until it is full and dropping all new packets • RIO • Run two RED algorithms for “in” and “out” with different dropping frequencies
Premium service • Fundamentally different Internet best effort service - high priority traffic has its own queue in routers • Shaped, hard-limited to provisioned peak rate • No bursts are injected into net • Virtual wire, available whenever needed • Regular flow pattern, no queuing • Shared, with best-effort
Mechanism for premium service Intra-network Host Router First-hop H-Q: premium, no dropping L-Q: best effort, dropping on congestion
Two-bit differentiated services architecture • Deploying both services • More bits available in IP header, why not both • Forwarding path mechanisms • Leaf routers • Input interface: a traffic profile • Output interface: two queues (HQ, LQ) • Intermediate routers • Only have forwarding function • Border routers • A Profile Meter at the input interface
Traffic flow from end-host to ISP Company A Internal Router Host 2 Border Router 1 First-hop Router 3 ISP Border Router
Forwarding path primitives • General classifier • In leaf routers, transport-level signature matching • Bit-pattern classifier • Performs a two-way decision based on bit-pattern • Bit setter • A- and P-bits must be set or cleared in several places • Priority queues • Shaping token bucket • At the leaf router for Premium traffic • Policing token bucket • At border router, for both P and A services
Block diagram of leaf router input functionality Marker 1 Flow1 Flow N Arriving packet Marker N Forwarding Engine Clear A&P bits Packet Classifier Best Effort
Markers to implement the two different services Wait for token Set P bit Packet Input N Test if token Set A bit Packet Input Y
Router output interface for two-bit architecture P-bit set? High-priority No If A-bit set? Inc a_cnt Low-priority If A-bit set? dec a_cnt RIO queue management
Border router input interface Profile Meters Token available ? N Clear A bit A set Y Forwarding Engine Is packet marked ? Not marked Y P set N Token Available Drop Packet
Passing configuration information • Request to the leaf router • Average rate, burst, service type (P or A) • Ways of passing the message • RSVP, SNMP, network administrator • Authenticating the sender
Architectural framework for marked traffic allocation • Preconfiguring of usage profiles is practical • Paying for level of service that is always available • Allocation follows organizational hierarchies • Each organization must be responsible for its DM • Only bilateral agreements work
Bandwidth Brokers (BB) • Roles • Allocating and controlling bandwidth shares • Responsibilities • Parcel out a region’s marked traffic allocation and set up the leaf routers within the local domain • Managing messages sent across boundaries to adjacent region BBs
Examples • A statically configured example with no BB message exchanged • A statically configured example with BB messages exchanged • Dynamic allocation and additional mechanism
RSVP and BBs • Existing bilateral relations between BBs of adjacent trust regions are necessary for resource allocation • A few bits in the packet header are used to mark the service class • RSVP resource setup: hop-by-hop • Use RSVP between two adjacent ISPs (BB1/BR1 and BB2/BR2)
Discussion • Extensibility of the current 2-bit architecture • Service allocation for multicast • Who should request the service • Sender or receiver • Deployment issues • Security issues
2-bit differentiated services architecture • Providing Controlled-Load and Guaranteed service • P service for C-L service • A constrained case of C-L service • P service for G service • The service model of P service fits G service model