First Annual Commonwealth Information Security Conference
1.75k likes | 1.99k Vues
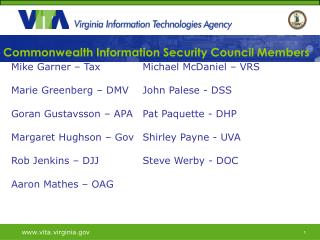
First Annual Commonwealth Information Security Conference. www.vita.virginia.gov. Agenda. Walter Kucharski Top 10 Commonwealth Information Security Issues/Opportunities/Concerns/Risks John Green Application Security: Why Firewalls Aren’t Enough Anymore

First Annual Commonwealth Information Security Conference
E N D
Presentation Transcript
First Annual CommonwealthInformation Security Conference www.vita.virginia.gov
Agenda • Walter KucharskiTop 10 Commonwealth Information Security Issues/Opportunities/Concerns/Risks • John GreenApplication Security: Why Firewalls Aren’t Enough Anymore • Keynote: Gino MenchiniGovernment IT: The New Expectations and Challenges • Randy MarchanyUnintended Consequences: Don't Create New Risks • Eric TaylorIT Seppuku: Why Do We Still Suffer Security Violations • Bob BasketteSocial Engineering: Building Bridges to Confidential Data
Commonwealth Information Security Conference November 2, 2009
AGA Top Ten List -- 2009 • STIMULUS MONEY -- ARRA • DATA SECURITY • VITA/NORTHROPGRUMMAN • ENTERPRISE APPLICATION/DATA EXCHANGE STANDARDS • MORE TIMELY FINANCIAL INFORMATION AUDITOR OF PUBLIC ACCOUNTS
AGA Top Ten List -- 2009 • ADMINISTRATIVE DUTIES CONSOLIDATION • SUCCESSION PLANNING • PERFORMANCE MANAGEMENT / MEASURES • CONTRACT MANAGEMENT • PPEA / PPTA AUDITOR OF PUBLIC ACCOUNTS
The FUTURE -- 2009 • Financial statements will need to be completed and issued with 90 days and the single audit within 4 months • The State needs newer accounting systems and one sole enterprise application will probably not be the answer • Data security concerns will continue to grow • There will be increasing e-commerce and data exchange between federal, local and state government • Information technology infrastructure and systems will become commodities and shared AUDITOR OF PUBLIC ACCOUNTS
Concerns • WHAT IS PRIVACY? • WHAT IS TRANSPARENCY? AUDITOR OF PUBLIC ACCOUNTS
Concerns • DATA SECURITY -- Employees • VITA/NORTHROP GRUMMAN • DATA EXCHANGE STANDARDS • MORE TIMELY FINANCIAL INFORMATION • CONSOLIDATING ADMINISTRATIVE DUTIES AUDITOR OF PUBLIC ACCOUNTS
Concerns • ACCOUNTING/ WORKFLOW SYSTEM CONTROLS WILL REPLACE MANUAL CONTROLS • E-COMMERCE AND DATA EXCHANGE BETWEEN FEDERAL, LOCAL AND STATE GOVERNMENT • SHARED INFORMATION TECHNOLOGY INFRASTRUCTURE AND SYSTEMS AS COMMODITIES 7 AUDITOR OF PUBLIC ACCOUNTS
What is an ISO • Paper pusher or Policeman • Management Oversight or One of the Gang • Tail-end Reviewer or System Developer and Guardian • Risk Manager or Elephant Parade Cleaner AUDITOR OF PUBLIC ACCOUNTS
Application Security:Why Firewalls Are Not Enough John Green Chief Information Security Officer Commonwealth of Virginia www.vita.virginia.gov www.vita.virginia.gov
Today’s Agenda Introduction Lessons From History Threats and Vulnerabilities Opportunities For Mitigation Resources Questions www.vita.virginia.gov
Application Vulnerabilities Skyrocketing! • Web vulnerabilities have increased from 1.9% of all published vulnerabilities in 2006 to over 52% in 2009. • Application vulnerabilities from 2007 to 2008 increased by 154%. • WhiteHat Security said about 70% of websites it scans are likely to have at least one critical website vulnerability. www.vita.virginia.gov Source: http://www.ncircle.com/index.php?s=solution_Web-Application-Vulnerability-Statistics
Largest Breaches In History www.vita.virginia.gov
Why? Money! = www.vita.virginia.gov
Firewall Are No Longer Enough Firewalls have been around a while Primary purpose: To stop unwanted traffic from crossing network boundaries Hackers are walking right through them Perimeter firewalls are necessary, but no longer sufficient! History shows us why www.vita.virginia.gov
Impenetrable Defenses Of France "We could hardly dream of building a kind of Great Wall of France, which would in any case be far too costly. Instead we have foreseen powerful but flexible means of organizing defense, based on the dual principle of taking full advantage of the terrain and establishing a continuous line of fire everywhere."— Maginot www.vita.virginia.gov
21st Century Maginot Line Internet Internal Networks Router Router Email Maginot Line: Term used now for something that is confidently relied upon but ends up being ineffective. Web www.vita.virginia.gov
May 10, 1940 - What Went Wrong? Defenses based on past threat Perimeter protection No layered defenses Holes Ardennes Forest Belgium was an ally Maginot Line never fell Bypassed Surrendered www.vita.virginia.gov
Firewalls Do Not Stop Today’s Threat Internet Internal Networks DB Server DB Server Router Router Email Web www.vita.virginia.gov
2008 Symantec Threat Report 63 percent of vulnerabilities affected Web applications, an increase from 59 percent in 2007 There were 12,885 site-specific cross-site scripting vulnerabilities identified, compared to17,697 in 2007; of the vulnerabilities identified in 2008, only 3 percent (394 vulnerabilities) had been fixed at the time of writing. The education sector represented the highest number of known data breaches that could lead to identity theft, accounting for 27 percent of the total The government sector ranked second and accounted for 20 percent of data breaches that could lead to identity theft. Hacking ranked second for identities exposed in 2008, with 22 percent; this is a large decrease from 2007, when hacking accounted for 62 percent of total identities exposed. www.vita.virginia.gov Source: http://www.symantec.com/business/theme.jsp?themeid=threatreport
OWASP Top 10 Application Flaws www.vita.virginia.gov Source: http://www.owasp.org/index.php/Top_10_2007
WASC Application Vulnerability Statistics Web Application Security Consortium (WASC ) Report 2008 includes data from 12186 web applications evaluated. Compared to 2007, the number of sites with wide spread SQL Injection and Cross-site Scripting vulnerabilities fell by 13% and 20%, respectively, however, the number of sites with different types of Information Leakage rose by 24%. On the other hand, the probability to compromise a host automatically rose from 7 to 13 %. www.vita.virginia.gov Source: http://projects.webappsec.org/Web-Application-Security-Statistics
SQL-injection Information Can occur whenever client-side data is used to construct an SQL query without first adequately constraining or sanitizing the client-side input. The use of dynamic SQL statements (the formation of SQL queries from several strings of information) can provide the conditions needed to exploit the backend database that supports the web server. SQL injections allow for the execution of SQL code under the privileges of the system ID used to connect to the backend database. Malicious code can be inserted into a web form field or the website’s code to make a system execute a command-shell or other arbitrary command. In addition to command execution exploitation, this vulnerability may allow a malicious individual to change the content of the back-end database and therefore the information displayed by the website. www.vita.virginia.gov
Cross-Site Scripting (XSS) Allows a malicious individual to utilize a website address that does not belong to the malicious individual for malicious purposes. Cross Site Scripting attacks are the result of improper filtering of input obtained from unknown or untrusted sources. Cross-Site Scripting attacks occur when a malicious individual utilizes a web application to send malicious code, generally in the form of a browser side script, to an unsuspecting user. The parameters entered into a web form is processed by the web application and the correct combination of variables can result in arbitrary command execution. www.vita.virginia.gov
Cross-Site Scripting (XSS) The unsuspecting user’s browser has no way to know that the script should not be trusted, and will execute the script. Because the unsuspecting user’s browser believes that the script came from a trusted source, the malicious script can access any cookies, session tokens, or other sensitive information retained by the unsuspecting user’s browser. The injected code then takes advantage of the trust given by the unsuspecting user to the vulnerable site. These attacks are usually targeted to all users of a web application instead of the application itself. www.vita.virginia.gov
Opportunities For Mitigation Personnel Awareness & Training Systems Development Life Cycle New Development Application Procurement Legacy Applications www.vita.virginia.gov
Systems Development Life Cycle • Project Initiation • Classify the data that the system will process • Determine if sensitive data absolutely must be collected and/or stored • Perform risk analysis based on known requirements & classification of data • Develop an initial IT System Security Plan • Project Definition • Identify, document & incorporate security control requirements into IT System design specifications • Develop evaluation procedures to validate that security controls • Update the IT System Security Plan to include controls • Implementation • Execute the evaluation procedures • Conduct a risk assessment to evaluate overall system risk • Update the IT System Security Plan to include controls • Disposition • Require that data retention schedules are adhered to • Require that electronic media is sanitized prior to disposal www.vita.virginia.gov
New Development • Push security involvement to the front end of development: • Security Design (for sensitive systems) • Encrypted communication channels • Sensitive information shall not be stored in hidden fields • Application Development • Application-based authentication shall be performed for access to data that is not considered publicly accessible • Support inactivity timeouts on user sessions • Data storage must be separated from the application interface • Validate all input irrespective of source, focus on server-side • Implement a default deny policy for access control • Use the least set of privileges required for processing • Internal testing must include one of: penetration testing, fuzz testing or source code auditing • Clear cached and temporary data upon exit • Production and Maintenance • Scan internet-facing sensitive applications periodically for vulnerabilities www.vita.virginia.gov
Applications Procurement • Work to incorporate language into contracts that includes: • General • Personnel, Security Training, Background Checks • Vulnerabilities, Risks and Threats • Application Development • Development Environment • Secure coding, Configuration management, Distribution, Disclosure, Evaluation • Testing • General, Source Code, Vulnerability and Penetration Test • Patches and Updates • Tracking Security Issues • Delivery Of The Secure Application • Self Certification • No Malicious Code • Security Acceptance And Maintenance • Acceptance • Investigating Security Issues www.vita.virginia.gov Source: http://www.sans.org/appseccontract/
Legacy Applications • Periodic application vulnerability scanning • Strong configuration management • If vulnerabilities are identified: • Each application may have specific challenges • Case by case analysis may reveal options: • Easy fix • Virtualization • Host based intrusion prevention • Application firewall technology • Third party integration • Other technology www.vita.virginia.gov
Resources www.vita.virginia.gov
www.OWASP.org www.vita.virginia.gov
2009 CWE/SANS Top 25 www.vita.virginia.gov
http://iase.disa.mil/stigs/checklist/ www.vita.virginia.gov
http://trustedsignal.com/secDevChecklist.html Recommended! www.vita.virginia.gov
Organizational Resources • Agency Information Security Officer • Commonwealth Security and Risk Management • Other Resources? CommonwealthSecurity@vita.virginia.gov www.vita.virginia.gov
Conclusions Largest breaches in history due to application vulnerabilities Firewalls are necessary but won’t protect vulnerable applications SQL injection and Cross Site Scripting top the lists of vulnerabilities measured and attacked Many opportunities to address the problem of insecure code Plenty of resources to help, USE THEM! www.vita.virginia.gov
GEN. Patton on “Usefulness of Firewalls” "Fixed fortifications are monuments to the stupidity of man." www.vita.virginia.gov
Questions? Thank You! John.Green@vita.virginia.gov www.vita.virginia.gov
IT’S ALL ABOUT SERVICE DRAFT for Review_v.4 Gino Menchini Managing Director
The City of New York Resident population of over 8 million; daytime population of 10 million Over 350,000 City employees, 300,000 retirees New York City Government includes its 5 counties The 1 million student school system reports to the Mayor Annual budget exceeds $59.5 billion dollars If New York City was a private sector corporation, it would be in the Top 30 of the Fortune 500 companies Over 120 agencies, offices, and organizations make up “The City”
New York City as a Bellwether – Local Government IT on Steroids New Breed of Leadership – Significant expansion in the role of IT Mayor Michael R. Bloomberg – Business & IT experience Younger commissioners, senior staff, and legislators demand more of IT Higher expectations on Government from the public They demand to perform transactions seamlessly through the Government walk-in, web and call centers Public’s perception of the competency of an administration is increasingly shaped by the ease of access/response
The role of IT in Emergency Response and Preparedness Focus on Public Safety Technologies 911 & CAD systems and infrastructure - 311 First Responder Radio infrastructure Command and Control Communications Greater Dependence on: GIS Email – Blackberries New Technologies Video Surveillance Systems – Sensor systems Hospital Emergency Room monitoring systems AVL Emergency Management Systems Real time Crime Center Intelligent Transportation systems Access control systems Telecomm carrier infrastructure survivability – post 9/11 Municipal IT infrastructure – Redundancy/Survivability
New York City as a Bellwether – Local Government IT on Steroids IT is now at the decision making table – Are we ready? Guide and manage a larger volume of IT projects simultaneously while advancing our IT Strategy Be prepared to deliver IT projects rapidly – high availability systems Provide solutions to address the problem of the day – Be relevant
NYC Department of Information Technology and Telecommunications - Then
The role of the NYC Department of Information Technology and Telecommunications - Now
New York City’s Agencies and IT Highly diverse range of services, unlike private sector. Virtually the entire range of Government Public Sector Services are provided by New York City – from Child care to Anti-terrorism, Street cleaning to fresh water reservoirs. Agencies are organized and staffed to focus on their area of responsibility and specialization (silos). Specialized agency specific IT applications need to be implemented and supported by agencies. High availability is required. Security is expected.
Unintended Consequences: Don’t Create New Risks Randy Marchany, VA Tech IT Security Office