Enhancing Security: Secondary Authentication & Phishing Prevention Research
80 likes | 193 Vues
Explore the weaknesses of secondary authentication methods like secret questions and the dangers of phishing attacks. Investigate alternate authentication methods and propose solutions to improve online security.

Enhancing Security: Secondary Authentication & Phishing Prevention Research
E N D
Presentation Transcript
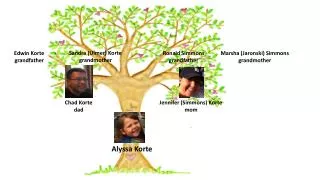
Secondary Authentication and Phishing Alyssa Ritchie
Outline • Secondary Authentication • Phishing • Secondary vs. Primary Authentication • New authentication systems
Secondary Authentication Studies have already shown that secret questions are a weak authentication tool. Many of the answers can be found in the public domain, Facebook or just guessing. We suspect that people will select only a small portion of the total available questions. xkcd
Secondary Authentication Because people come from different backgrounds, a lot of questions will not be applicable to many people. Using a survey, I hope to determine whether my hypothesis is correct.
Phishing Hackers will use phishing attacks such as website forgery where they spoof a website and trick the user into volunteering personal information to a source they thought trustworthy.
Phishing • Alternate authentication methods • Identifying pictures • Using different symbols
Secondary vs. Primary Authentication • Time • Mistakes • Memorization • Frequency of Use
Goals • Show ineffectiveness and the security concern of current secondary authentication methods • Propose an alternate secondary authentication • Create an addition to the current password system to stop phishing