Short Non-interactive Zero-Knowledge Proofs
This paper explores advancements in non-interactive zero-knowledge proofs (NIZK) focusing on the efficient usage of hidden random bits. We present two novel techniques: one that enhances the efficiency of hidden random bits implementation and another that leverages probabilistically checkable proofs to reduce soundness errors. Our results demonstrate that circuit size and hidden bits can be managed to optimize the performance of zero-knowledge proofs. These advancements contribute significantly to cryptographic protocols and enhance security levels while addressing efficiency concerns.

Short Non-interactive Zero-Knowledge Proofs
E N D
Presentation Transcript
Short Non-interactive Zero-Knowledge Proofs Jens Groth University College London TexPoint fonts used in EMF. Read the TexPoint manual before you delete this box.: AAAAAAAAAAAAA
Non-interactive zero-knowledge proof CRS: 0100…11010 Statement: xL (x,w)RL Proof: Zero-knowledge: Nothing but truth revealed Soundness: Statement is true Prover Verifier
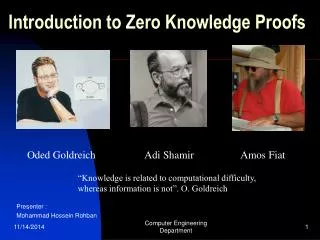
Non-interactive zero-knowledge proofs Adaptive soundness:Adversary sees CRS before attempting to cheat with false (C,) • Statement C is satisfiable circuit • Perfect completeness • Statistical soundness • Computational zero-knowledge • Uniformly random common reference string • Efficient prover – probabilistic polynomial time • Deterministic polynomial time verifier
Our results • Security level: 2-k • Trapdoor perm size: kT = poly(k) • Circuit size: |C| = poly(k) • Witness size: |w| |C|
Hidden random string - soundness Statement: xL (x,w)RL 0 1 0 1
Hidden random string – zero-knowledge Statement: xL 0 1
Two new techniques • More efficient use of hidden random bits • Kilian-Petrank: |C|∙k∙(log(k)) hidden random bits • This work: |C|∙polylog(k) hidden random bits • More efficient implementation of hidden bits • Trapdoor permutations: kT = poly(k) bits per hidden random bit • Naccache-Stern encryption: O(log k) bits per hidden random bit
Implementing the hidden random bits model Statement: xL (x,w)RL Epk(0;r1) c1 01...0 c1 Epk(1;r2) c2 11…1 1 ; r2 Epk(0;r3) c3 00…1 c3 K(1k) (pk,sk) Epk(1;r4) c4 10…0 0 ; r4
Naccache-Stern encryption • pk = (M,P,g) sk = (M) • M is an RSA modulus • P = p1p2…pd where p1,…,pd are O(log k) bit primes • P | ord(g) = (M)/4 and |P| = O(|M|) • Epk(m;r) = gmrP mod M • Dsk(c): For each pi compute m mod pi c(M)/pi = (g(M)/pi)mChinese remainder gives m mod P
Naccache-Stern implementation of hidden bits 0 if m mod pi even 1 if m mod pi odd if m mod pi is -1 Statement: xL (x,w)RL ?1? ; 1 Epk(010;r1) c1 01...0 10? ; 2 Epk(101;r2) c2 11…1 ??1 ; 3 Epk(011;r3) c3 00…1 K(1k) (pk,sk) ??? ; 4 Epk(110;r4) 10…0 c4
Revealing part of Naccache-Stern plaintext • Ciphertext c = gmrP • How to prove that m = x mod pi? • Prover reveals such that P = (cg-x)(M)/pi • Shows P = (gm-xrP)(M)/pi = (g(M)/pi)m-x • Can compute the proof as = (cg-x)(P-1 mod (M)/P)P/pi • Can randomize proof by multiplying with s(M)/P • Generalizes to reveal m mod iSpi with a proof consisting of one group element
Zero-knowledge • Simulator sets up pk = (M,P,g) such that ord(g) = (M)/4P and g = hP mod M • Simulator also sets up the CRS such that it only contains ciphertexts of the form gt mod M • For any m ZP we can compute r = ht-m mod M such that gt = gm(gt-m) = gmrP mod M • This means the simulator can open each ciphertext to arbitrary hidden bits
Efficient use of the hidden random bits Statement: xL (x,w)RL 0 1 0 1
Kilian-Petrank Probably hidden pairs are 00 and 11 • Random bits not useful; need bits with structure • Use statistical sampling to get “good” blocks 10 11 00 01
Kilian-Petrank continued • Reveal blocks of bits so remaining “good” blocks of bits have a particular structure (statistically) • Reduce C to a 3SAT formula • Assign remaining “good” blocks to variables in • For each clause reveal some bits in the blocks assigned to the literals of the clause • An unsatisfied clause has some probability of the revealed bits not satisfying certain criterion • Repeat many times to make the probability of cheating negligible for each clause
Probabilistically checkable proofs • Polynomial time algorithms f, fw: f: C belongs to gap-3SAT5 fw: w x if C(w)=1 then (x)=1 • is a gap-3SAT5 formula • All variables appear in exactly 5 clauses – thrice as positive literal and twice as negative • Either all clauses are simultaneously satisfiable or a constant fraction are unsatisfiable
Strategy • Compute = f(C) and prove that it is satisfiable • With the most efficient probabilistically checkable proofs (Dinur 07 combined with BenSasson-Sudan 08) we have || = |C| polylog(k) • Seems counterintuitive to make statement larger • However, since allows for a constant fraction of “errors” less repetition is needed to make the overall soundness error negligible • It is ok if the prover cheats on some clauses as long as cannot cheat on a constant fraction
Summary • Technique 1: Reduce soundness error with probabilistically checkable proofs • Technique 2: Implement hidden random bit string with Naccache-Stern encryption