Public Key Cryptography
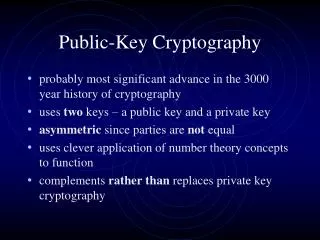
Public key cryptography plays a vital role in ensuring the privacy and authenticity of digital communications. This method addresses key security concerns: Can anyone else see the messages? Is it genuinely Alice sending the message? Has the message been altered? By leveraging encryption schemes, digital signatures, and message authentication codes, we can maintain the integrity of data exchanges. Alice can communicate securely by encrypting her message with Bob’s public key, ensuring only Bob, with his private key, can decrypt it.

Public Key Cryptography
E N D
Presentation Transcript
Some Security Issues • Can anyone see the messages? • Is it really Alice who is sending the message? • Has the message been tampered with? • Privacy • Authenticity • Integrity
How cryptography helps • Encryption Schemes • Digital Signatures • Message Authentication Codes • Privacy • Authenticity • Integrity
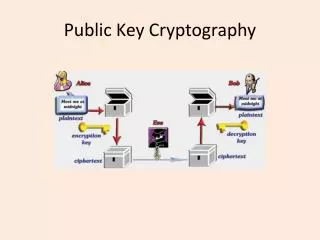
Encryption This can be done in two ways: • Alice and Bob agree on a secret key and use the secret key to encrypt/decrypt messages • Alice encrypts her message using Bob’s public key, send it to Bob. Bob uses his private key to decrypt the message and vice versa.